VoidLink represents a concerning evolution in malware development: a sophisticated Linux command-and-control framework that shows clear signs of being built with AI assistance.
This Linux malware operates as a modular implant designed for long-term access to compromised systems.
It doesn’t discriminate between cloud providers, actively harvesting credentials from AWS, Google Cloud Platform, Microsoft Azure, Alibaba Cloud, and Tencent Cloud.
The implant searches environment variables, configuration directories, and cloud metadata APIs to steal access keys and service tokens.
While the implant demonstrates impressive technical capabilities spanning multi-cloud credential theft, container escape techniques, and adaptive rootkit functionality its source code reveals telltale patterns of LLM-generated code that went into production with minimal human review.
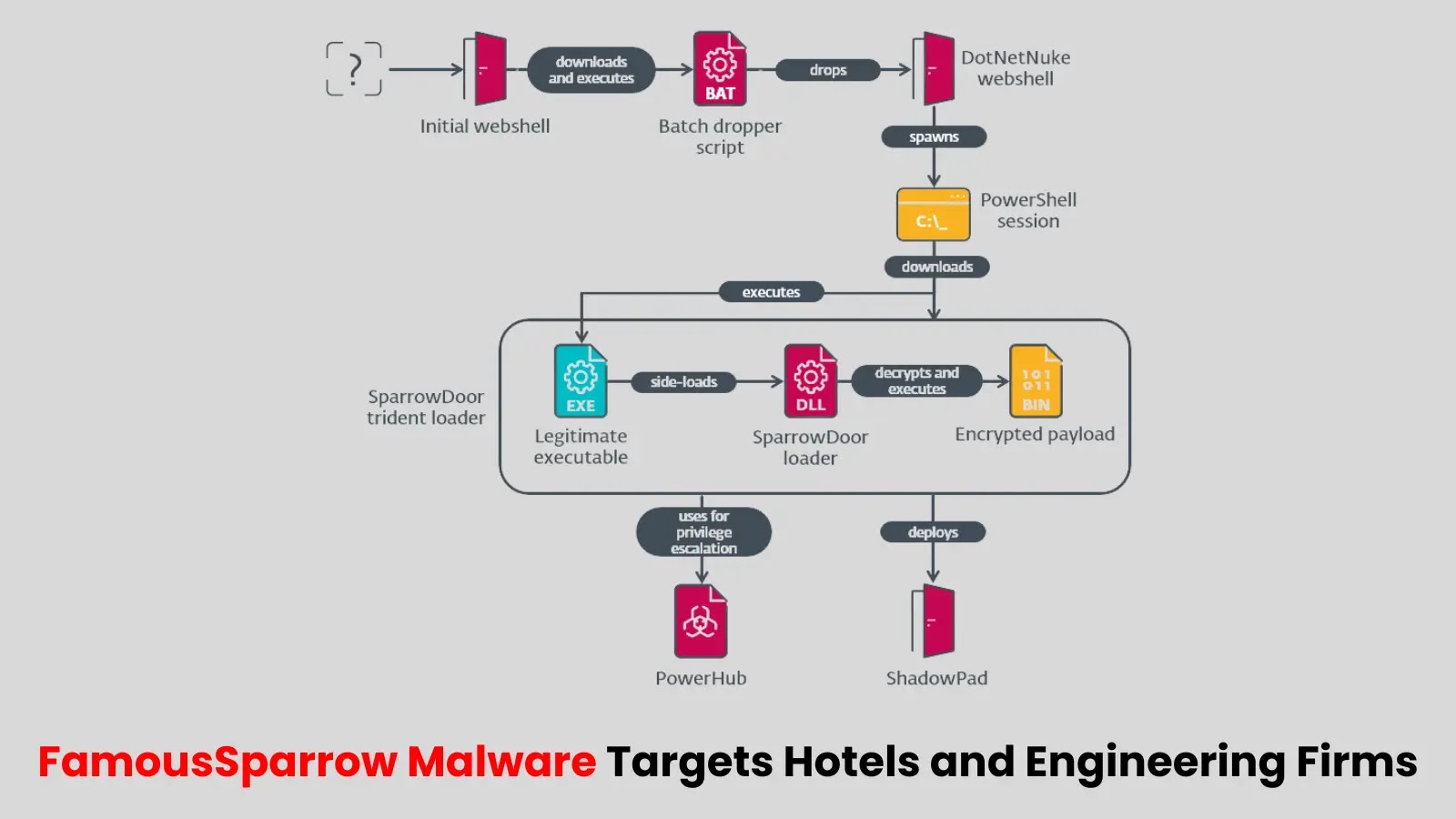
VoidLink goes beyond simple credential theft. It detects whether it’s running inside Docker, Podman, or Kubernetes containers, then loads specialized plugins to break out of these isolated environments.
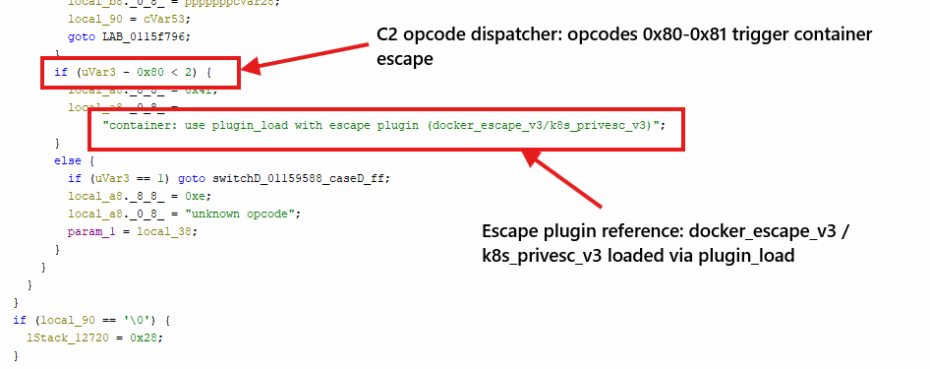
The docker_escape_v3 and k8s_privesc_v3 modules attempt privilege escalation, while the malware specifically targets Kubernetes service account tokens that can provide cluster-wide access.
VoidLink Linux C2
The rootkit component adjusts its hiding techniques based on the host kernel version. Modern systems running kernel 5.5 or newer face eBPF-based stealth that intercepts system calls.
Older kernels encounter loadable kernel modules, while legacy systems below version 4.0 get userland hooking through shared library injection. This adaptability makes VoidLink effective across diverse Linux environments.
Command-and-control communications use AES-256-GCM encryption over HTTPS, disguised as legitimate web traffic.
The implant mimics normal API requests and browser sessions, making network detection more challenging. Analysts discovered a hardcoded C2 server at IP address 8.149.128[.]10.
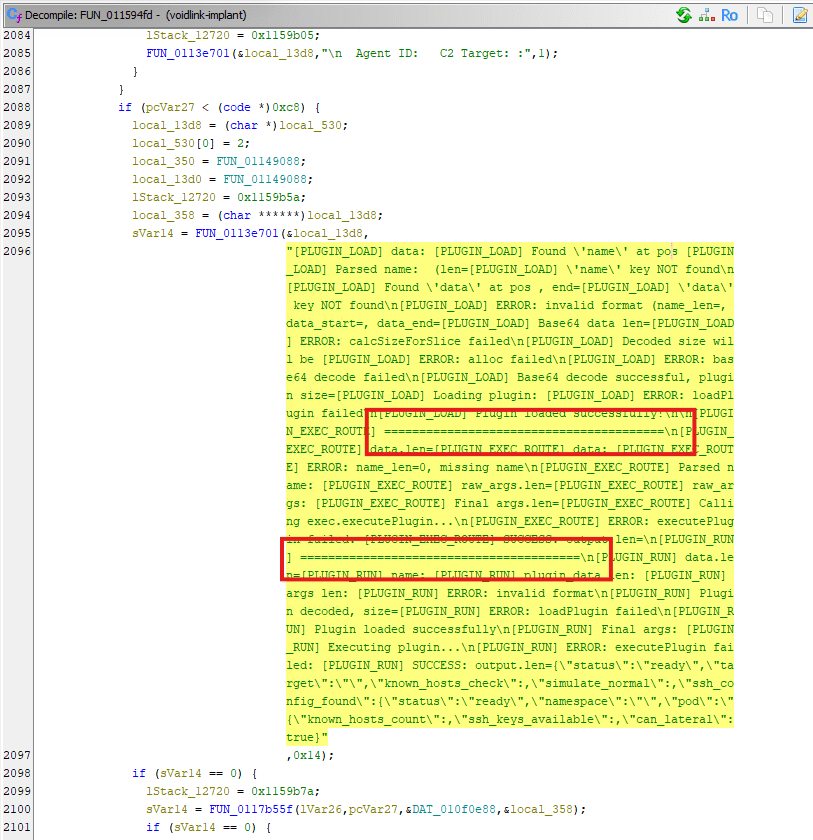
What distinguishes VoidLink from professionally crafted malware is what it leaves behind. The binary contains structured “Phase X:” labels numbering up to eight, with Phase 7 mysteriously absent and Phase 5 duplicated across different functions.
Production code includes verbose debug logging and formal status messages like “successfully initialized” artifacts that experienced malware authors routinely remove.
Pattern-matching analysis revealed excessive use of equals characters in comments, a formatting quirk common in AI-generated code.
The documentation style suggests code produced through multiple LLM prompts without enforced continuity between outputs. Professional developers prioritize stealth over readability and strip debug information; VoidLink does the opposite.
Why This Matters
VoidLink isn’t a research prototype it’s a functional implant with active infrastructure behind it.
The malware successfully combines cloud environment fingerprinting, container-aware lateral movement, kernel-level concealment, and encrypted communications.
What previously required specialized expertise can now be assembled using AI coding agents.
The barrier to producing capable malware has dropped significantly. Threat actors no longer need deep technical knowledge to create implants that evade detection and persist in complex environments.
Defenders should anticipate more AI-assisted malware appearing in the wild, built faster and deployed more widely than traditional development cycles allow.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.