A threat cluster tracked as “Vortex Werewolf” (also known as SkyCloak) has been observed targeting Russian government and defense organizations.
The attack begins not with a typical malicious attachment, but with a highly credible phishing link. Vortex Werewolf distributes URLs that masquerade as legitimate Telegram file-sharing resources.
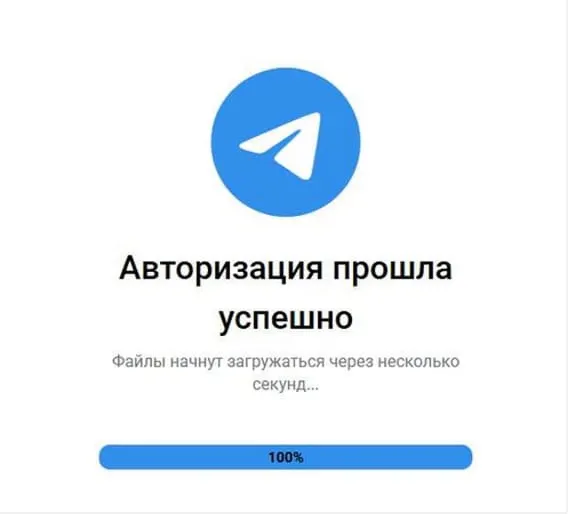
These links, often hosted on domains designed to look like trusted file repositories, lead victims to a webpage that mimics a Telegram login or file download verification screen.
When a victim interacts with this page, they are prompted to enter their phone number and a confirmation code sent to their Telegram account.
If the account is protected by two-factor authentication (2FA), the page also requests the cloud password. This process allows the attackers to hijack the victim’s active Telegram session, granting them unauthorized access to chats and contacts.
According to a new report from BI.ZONE Threat Intelligence, the attackers utilize a multi-stage infection chain that begins with Telegram-themed phishing and ends with a fully persistent, Tor-enabled remote access channel into secure networks.
Once the “verification” is complete, the site automatically triggers the download of a ZIP archive, such as Spisok na peremeshchenie.zip (“Movement List”), hosted on public cloud services like Dropbox.
The Infection Chain
The LNK file executes a PowerShell command that extracts a hidden directory containing a suite of tools.
To evade detection by security researchers, the malware performs immediate environment reconnaissance.
It checks the number of recent files and running processes; if the system appears to be a virtual machine or a sandbox (indicated by low activity), the malware terminates itself.
If the system passes these checks, the script establishes persistence by creating scheduled tasks in the Windows Task Scheduler.
These tasks ensure that the malware restarts automatically if the computer is rebooted. The attackers rename legitimate software components to blend in with normal system operations.
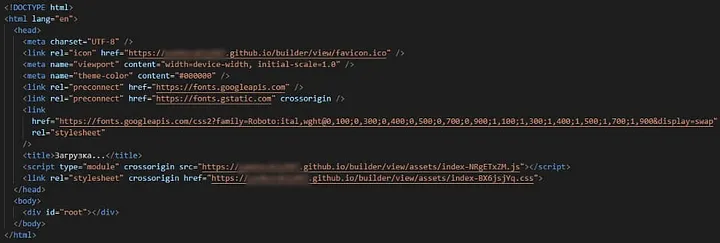
Vortex Werewolf uses GitHub Pages to host static JavaScript and CSS resources, creating a dedicated repository for each phishing domain.
Tor executable is renamed photoshopexpress.exe, the OpenSSH server is renamed finalcutpro.exe, and the obfuscation proxy tool (obfs4proxy) is disguised as visualstudiocode.exe.
Technical Deep Dive: Tor and SSH
The ultimate goal of Vortex Werewolf is to maintain covert, long-term access to the victim’s network.
The malware installs a customized version of OpenSSH for Windows and configures it to accept connections only via key-based authentication, turning off password logins to prevent unauthorized third-party access.
Simultaneously, the malware launches a Tor Hidden Service. By routing traffic through the Tor network, the attackers can connect to the infected machine without revealing their own IP address or location.
System Volume Information, hidden directory containing another ZIP archive, logLength (without a file extension).

logLength(Source : BI.ZONE).Crucially, the malware uses obfs4 bridges to obfuscate this traffic, making it look like random noise rather than recognizable Tor data. This allows the attackers to bypass standard network firewalls that might otherwise block Tor connections.
Through this hidden tunnel, Vortex Werewolf exposes critical network protocols specifically RDP (Remote Desktop Protocol), SMB (file sharing), SFTP, and SSH directly to the attackers.
This grants them full control over the compromised system, allowing them to move files, execute commands, and pivot to other machines within the organization’s network.
While Vortex Werewolf shares some tactical similarities with another group known as Core Werewolf such as targeting the defense sector and using SSH for backdoors threat intelligence analysts currently treat them as distinct clusters.
Investigations into the network infrastructure reveal that Vortex Werewolf has been active since at least December 2024, utilizing infrastructure that includes GitHub Pages for hosting phishing assets and Cloudflare for traffic management.
Indicators of compromise
| # | Hash Value |
|---|---|
| 1 | fc8a6cc400dd822b6f5fc40c85a547cf7f266169edddb84a90f4b3f25956318c |
| 2 | 86b1e4e48d1d4ce1acf291b21c2ffa806bca9b6cad6a6519263fa1705486eb94 |
| 3 | 8f4836cca1850053e87a769a84baed3cdde060ad3fce26f101a20b37375835f1 |
| 4 | 1cf423b7b55c2d7018262c847ba58e1955443e1d84ca0bca4f94f2a9cc5794d7 |
| 5 | 1280cca4b520bfd018296c4d1645b7c9c8c7c4608752506285dad0e251b22e32 |
| 6 | 7ccf33529389ff080c1aaea1678c9f7a3546ab950670138f8a7f35c7638578cb |
| 7 | 2a9b971c835e2ee5f190d068c602601fdaf718d8bfe085c2032d59a6f25ed082 |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.