VPNs, Proxies and Secure Tunnels Explained (Deepdive)

Source link
Related Articles
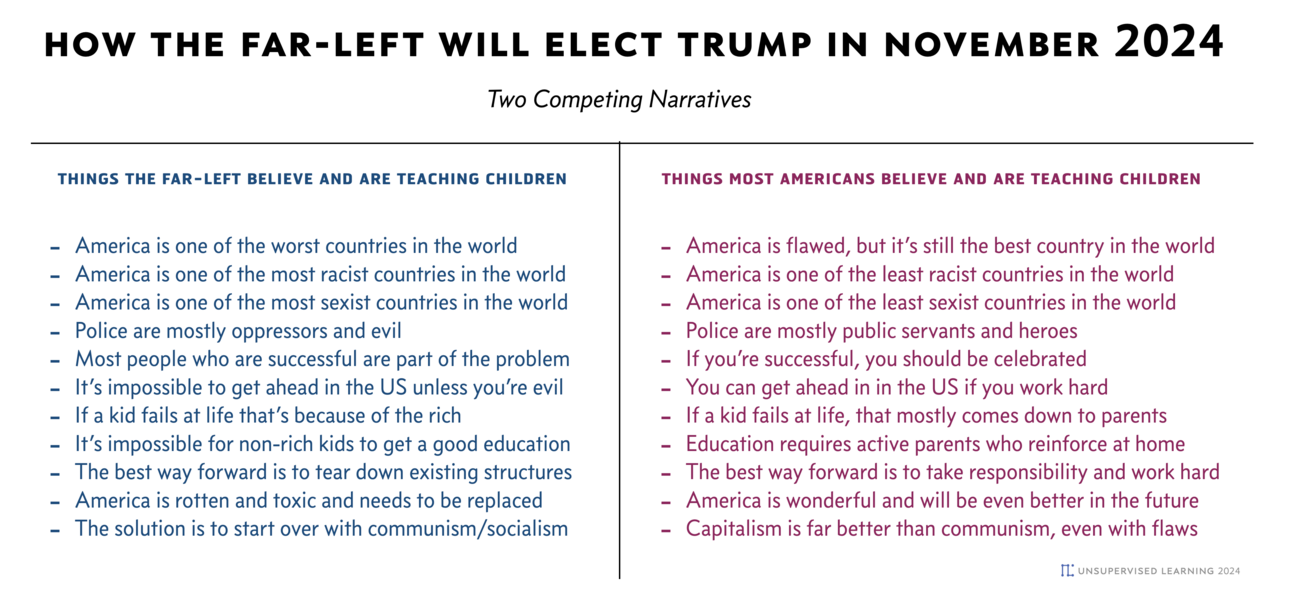
All Mix →How the Far-left Will Elect Trump in November 2024
Click and read the full-size version before continuing As someone who detests Trump, I think I finally figured out why he’s so popular. In short,…
The Hacker-Powered Security Report 2018
Table of Contents Key Findings History of Hacker-Powered Security Trends in Hacker Education Customer Success Stories “Crowdsourced security testing is rapidly approaching critical mass, and…
Kata Containers – Improper file permissions for read-only volumes
An improper file permissions vulnerability affects Kata Containers prior to 1.11.5. When using a Kubernetes hostPath volume and mounting either a file or directory into…
A Crazy Idea Regarding the Obama Administration and Security
I have a wicked crazy idea. What if we in the information security community were to organize a campaign to get level-headed, rational thinkers into…
Improving Security with Wallarm’s NIST CSF 2.0 Dashboard
Table of Contents Business Context and the Importance of NIST CSF Improving Security with Wallarm's NIST CSF 2.0 Dashboard Features and Acceptance Criteria of Wallarm’s…
If This Isn’t Intelligence, I Don’t Know What Is
Table of Contents 1. Tagging my entire site 2. Bring my images home 3. Converting super nasty HTML bundles to Markdown The takeaway Summary (my…