VPNs, Proxies and Secure Tunnels Explained (Deepdive)

Source link
Related Articles
All Mix →The Power of Bug Bounty and VDP
Table of Contents Why VDP and Bug Bounty? A Global Community of Researchers Unmatched Creativity Time Spent Leadership Buy-in Budget Why VDP and Bug Bounty?…
Claude Code is the Biggest AI Development Since ChatGPT
I’ve had a number of thoughts around Claude Code in the last couple of days. I’ve especially been trying to put into words a feeling…
The DOD Improves Their Security Posture Through the DIB-VDP
Who is DC3’s DCISE? Krystal Covey: The Defense Collaborative Information Sharing Environment (DCISE) is the operational hub for the DOD’s DIB Cybersecurity (CS) Program offering…
The Moral Market Fallacy | Daniel Miessler
Many conservatives and libertarians are deeply confused about the morality of markets. They view markets as pure and benign forces with the ability to grant…
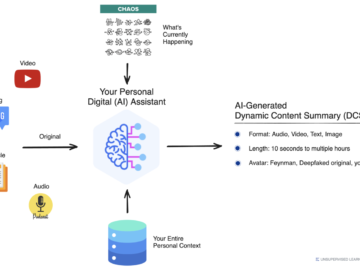
Dynamic Content Summaries (DSC)
Table of Contents Scenario: Book Too Long, Please Summarize Any format, length, and avatar Summary One of the coolest things I can’t wait to come…
Product update: Dynamic API Scanning, Recommendations and Classifications, and more
Table of Contents What have we shipped to customers over the last few months? Introducing Dynamic API Scanning Not sure what to scan? We do. …