A Go‑based remote administration tool known as Vshell is emerging as a favored alternative to Cobalt Strike among both red teams and threat actors.
Though marketed as a legitimate network administration and security testing platform, recent analyses indicate that Vshell’s powerful post‑compromise capabilities are increasingly used in unauthorized operations.
Developed as a cross‑platform command‑and‑control (C2) framework, Vshell allows operators to remotely manage Windows and Linux hosts, perform lateral movement, and proxy traffic within victim networks.
Despite its claimed defensive use, public repositories and screenshots have referenced offensive tools such as Mimikatz suggesting its potential alignment with attack operations.
Since its first release in 2021, Vshell’s distribution has alternated between open‑source and closed‑source releases, complicating attribution and version control.
Some versions are freely available on GitHub, while others circulate privately among Chinese‑language security communities.
Censys data shows that Internet‑facing Vshell panels often appear beside other intrusion frameworks, including Cobalt Strike, in open web directories sometimes hosting hundreds of connected “client” agents that act as communication relays for network pivoting.
In 2022, the project rebased itself on NPS, a Chinese intranet penetration proxy, making the two tools’ network communication features nearly identical. This pivot enhanced Vshell’s reliability for red teams and attackers seeking high‑performance tunneling.
Milestones and Adoption
Security research by NVISO traces Vshell’s evolution across five core versions.
| Version | Year | Description |
|---|---|---|
| v1 | 2021 | Introduced as “teamserver,” operated via AntSword |
| v2 | 2022 | Added local web interface |
| v3 | 2022 | Rebased onto NPS and expanded protocol support |
| v4 | 2023 | Licensing, redesigned UI, nginx impersonation |
| v4.6 | 2024 | End of public releases; possible private development |
Throughout 2025, Vshell surfaced in multiple threat campaigns. Reports linked it to Operation DRAGONCLONE, UNC5174’s SNOWLIGHT, and several phishing incidents analyzed by Trellix.
These cases highlight its growing role as a post‑compromise tool in both espionage and financially motivated intrusions.
Censys scanning reveals Vshell deployments across various geographies, with Mandarin as the default interface language.
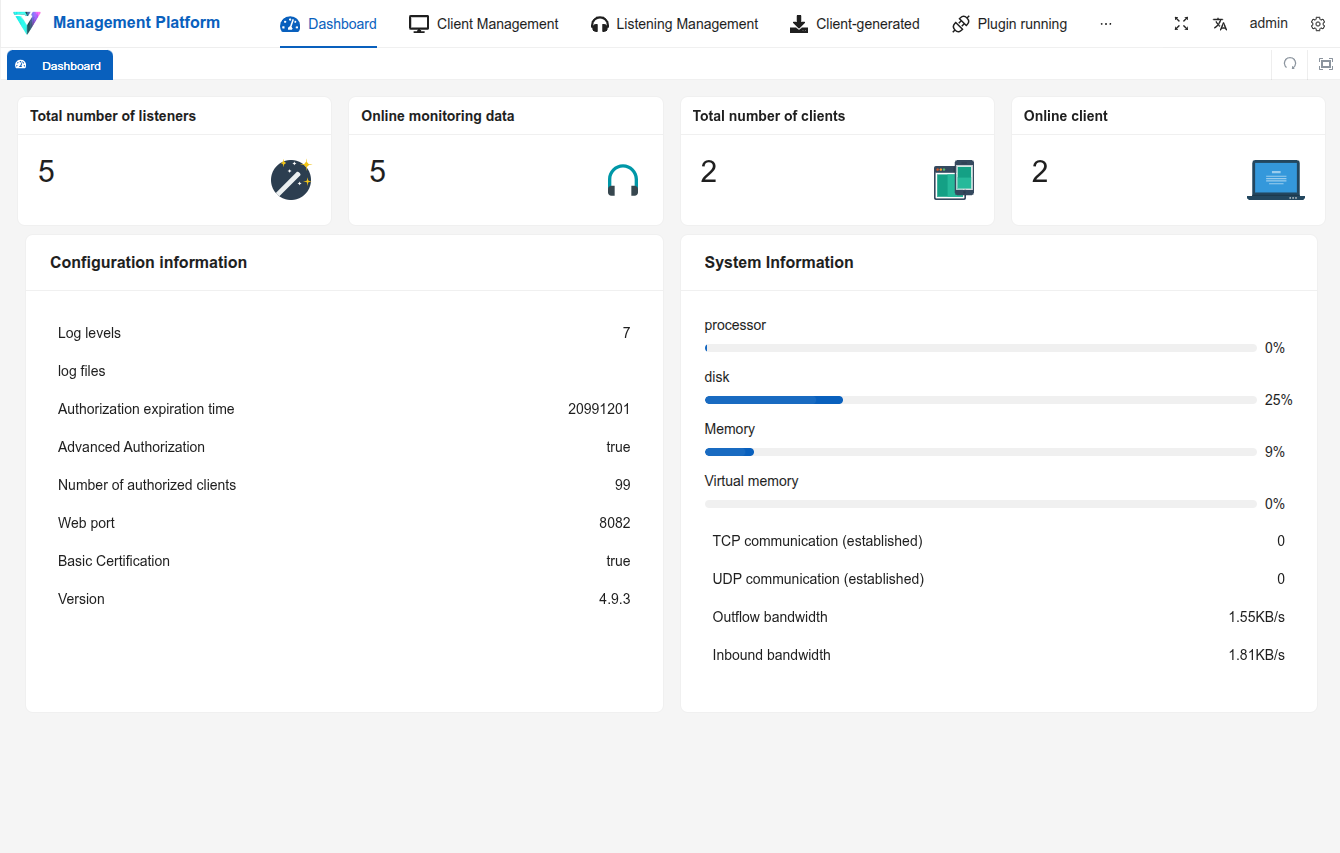
Its architecture mirrors Cobalt Strike framework: a central controller manages implants (clients) through configurable “listeners.” Common listener types include TCP, UDP (KCP), WebSocket, DNS, and DNS‑over‑HTTPS/TLS.
Many default to port TCP/8084, but flexible configuration allows blending into normal traffic patterns.
Each listener type supports encrypted communication channels, enabling stealthy tunneling across corporate networks.
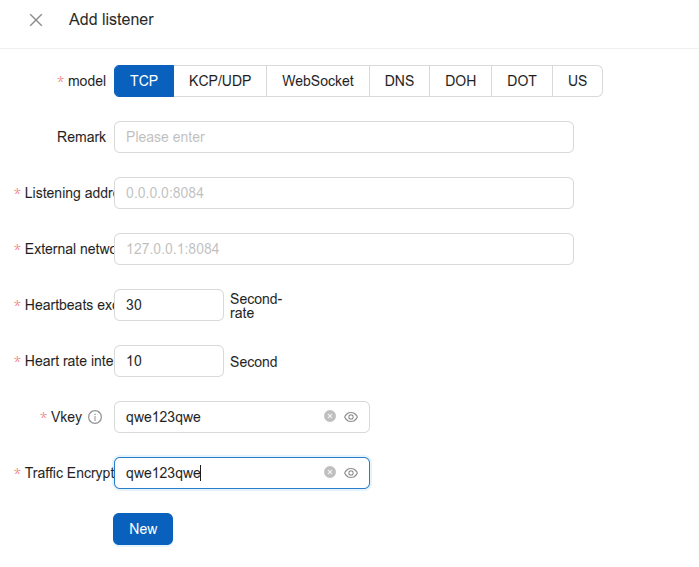
For defenders, this variety significantly broadens the detection surface, requiring multi‑protocol monitoring and deeper inspection of outbound traffic anomalies.
Censys Observations
Censys telemetry indicates fewer than five legacy Vshell panels online at a time, but over 850 active listeners remain visible through ongoing scans.
Censys Threat Hunting module customers can identify Internet-facing Vshell exposure, using the following query:
host.services.threats.name = "Vshell" or web.threats.name = "Vshell"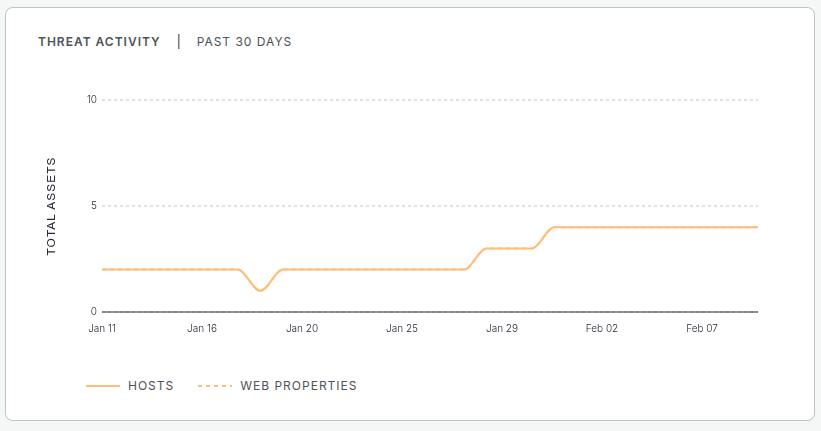
Security teams should treat Vshell as a credible threat component. Detecting its presence typically requires monitoring high‑numbered TCP ports, DNS tunneling activity, and anomalous WebSocket sessions.
Newer versions now employ digest authentication, reducing fingerprintable elements previously used to identify older builds.
Like other dual‑use frameworks, Vshell demonstrates a trend toward operational hardening less visible signatures, limited open interfaces, and modular communication.
Its continuous refinement and availability make it a viable, lower‑cost alternative to commercial adversary simulation tools.
Because it incorporates NPS elements, some detection artifacts may overlap. Persistent visibility into external‑facing infrastructure particularly web servers and firewalls remains essential to mitigating Vshell‑enabled access.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






