Threat actors exploit Microsoft Defender SmartScreen zero-day flaws to circumvent the security mechanisms designed to protect users from malicious websites and downloads.
By leveraging these vulnerabilities, threat actors can evade detection, gain unauthorized access, and execute potentially harmful actions.
Cybersecurity researchers at Tren Micro recently identified that threat actors behind the APT group Water Hydra (aka DarkCasino) have been actively exploiting Microsoft Defender SmartScreen zero-day flaw.
The Trend Micro Zero Day Initiative discovered the vulnerability as CVE-2024-21412, tracked as ZDI-CAN-23100.
Live attack simulation Webinar demonstrates various ways in which account takeover can happen and practices to protect your websites and APIs against ATO attacks
.
Water Hydra Exploits Microsoft SmartScreen
The Water Hydra group emerged in 2021 and was found to be hitting the finance sector worldwide hard. Initially linked to Evilnum, they unveiled DarkMe RAT in the DarkCasino campaign (Sept 2022).
A streamlined infection process has been actively used by the Water Hydra group since later January 2024.
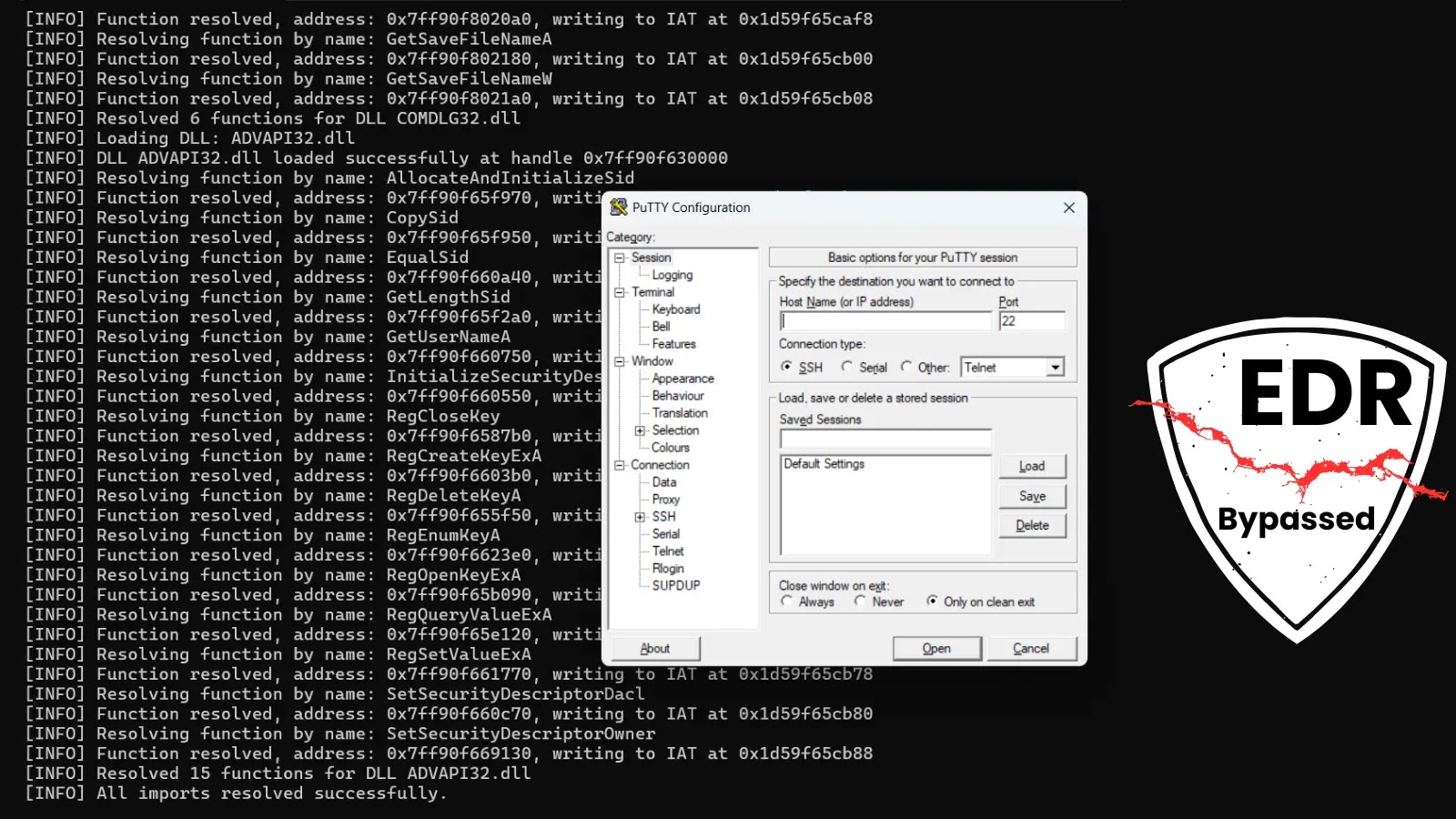
Water Hydra streamlined the DarkMe infection process in January 2024 by updating its infection chain and using CVE-2024-21412 to run a malicious Microsoft Installer File (.MSI).
Water Hydra’s spearphishing campaign (T1566.002) hit forex and stock trading forums using DarkMe malware. Social engineering tactics involved fake stock tools posted on a compromised Russian site (fxbulls[.]ru).
Notably, this site shares a name with a legit broker (fxbulls[.]com), on the Apple App Store’s MT4 removed and later reinstated due to Russian sanctions.
The campaign tricks victims with an internet shortcut (.url), abusing the search protocol in Windows Explorer by exploiting the CVE-2024-21412. Water Hydra employs imagress.dll to disguise the shortcut as a JPEG that helps bypass SmartScreen and compromise Windows.
An unusual twist involves referencing another internet shortcut (2.url) within the initial one by exploiting a SmartScreen zero-day (CVE-2023-36025).
Water Hydra manipulates Windows Explorer by tricking the users into triggering the CVE-2024-21412 exploit that enables the exploration of MotW flaws, and evades SmartScreen. The infection chain operates discreetly, as it’s undisclosed to the user.
After SmartScreen bypasses the second 2.url executes a ZIP-embedded batch file from the WebDAV share by initiating the DarkMe DLL loader without user awareness. The entire process occurs stealthily by leaving users oblivious.
Post-exploitation, the actor connects to a WebDAV server to download a genuine JPEG with the same name as the Trojan that deceives the victim into thinking they opened the intended file, unaware of the DarkMe infection.
Zero-day attacks pose grave risks to organizations by exploiting undisclosed vulnerabilities like CVE-2023-38831 used by Water Hydra before disclosure.
APT groups like APT28 and APT29 leverage such exploits by worsening threats. Furthermore, bypassing patches like CVE-2023-36025 with CVE-2024-21412 underscores how APTs adapt to security measures.
Stay updated on Cybersecurity news, Whitepapers, and Infographics. Follow us on LinkedIn & Twitter.