Here’s an overview of some of last week’s most interesting news, articles, interviews and videos:
Hackers stole call, text records of “nearly all” of AT&T’s cellular customers
Hackers leveraging stolen Snowflake account credentials have stolen records of calls and texts made by “nearly all” of AT&T’s cellular customers from May to October 2022, the company has confirmed.
Critical vulnerability in the RADIUS protocol leaves networking equipment open to attack
A new critical security vulnerability in the RADIUS protocol, dubbed BlastRADIUS (CVE-2024-3596), leaves most networking equipment open to Man-in-the-Middle (MitM) attacks.
Zero-day patched by Microsoft has been exploited by attackers for over a year (CVE-2024-38112)
CVE-2024-38112, a spoofing vulnerability in Windows MSHTML Platform for which Microsoft has released a fix on Tuesday, has likely been exploited by attackers in the wild for over a year, Check Point researcher Haifei Li has revealed.
Info of 2,3+ million individuals stolen in Advance Auto Parts data breach
Personal information of over 2,3 million individuals has been stolen by attackers as part of the massive data grab via compromised Snowflake accounts without MFA protection, Advance Auto Parts has confirmed by filing notices with the attorney general offices in several US states.
TeamViewer: Network segmentation hobbled Midnight Blizzard’s attack
TeamViewer, the company developing the popular remote access/control software with the same name, has finished the investigation into the breach it detected in late June 2024, and has confirmed that it was limited to their internal corporate IT environment.
BunkerWeb: Open-source Web Application Firewall (WAF)
BunkerWeb is an open-source Web Application Firewall (WAF) distributed under the AGPLv3 free license.
Microsoft’s cybersecurity dilemma: An open letter to Satya Nadella
Microsoft is suffering cybersecurity failures due to systemic problems with strategic leadership.
July 2024 Patch Tuesday forecast: The end of an AV giant in the US
The US celebrated Independence Day last week, providing many with a long weekend leading into patch week. With summer vacations underway, many developers must be out of the office because June was fairly quiet regarding software updates.
Managing cyberattack fallout: Financial and operational damage
In this Help Net Security, Ashley Harrington, Director of Cybersecurity at Aspida, discusses the impact of cyberattack on business operations and financial health.
Strengthening cybersecurity preparedness with defense in depth
In this Help Net Security interview, Chaim Mazal, Chief Security Officer at Gigamon, discusses cybersecurity preparedness measures for businesses, the impact of international inconsistencies on global operations, and the board’s role in cybersecurity.
How companies increase risk exposure with rushed LLM deployments
In this Help Net Security interview, Jake King, Head of Threat & Security Intelligence at Elastic, discusses companies’ exposure to new security risks and vulnerabilities as they rush to deploy LLMs.
Exploring the root causes of the cybersecurity skills gap
In this Help Net Security interview, Koma Gandy, VP of Leadership and Business at Skillsoft, addresses the critical aspects of the cybersecurity skills gap, the need for diverse talent and continuous upskilling in areas like AI and cloud computing.
How nation-state cyber attacks disrupt public services and undermine citizen trust
In this Help Net Security interview, Rob Greer, VP and GM of the Enterprise Security Group at Broadcom, discusses the impact of nation-state cyber attacks on public sector services and citizens, as well as the broader implications for trust and infrastructure.
Info of 2,3+ million individuals stolen in Advance Auto Parts data breach
Personal information of over 2,3 million individuals has been stolen by attackers as part of the massive data grab via compromised Snowflake accounts without MFA protection, Advance Auto Parts has confirmed by filing notices with the attorney general offices in several US states.
Using Authy? Beware of impending phishing attempts
Do you use Authy for your multi-factor authentication needs? If you do, you should keep an eye out for phishing attempts, as well as implement defenses against SIM swapping attacks.
How AI-powered software spreads Russian disinformation on X
The US Justice Department (DoJ) has seized two US-based domains used by Russian threat actors to create fake profiles on X (formerly Twitter) that would spread disinformation in the United States and abroad.
Google removes enrollment barrier for prospective Advanced Protection Program users
Google has removed a potential obstacle for high-risk users who want to enroll in the company’s Advanced Protection Program (APP): they can now do it just by setting a passkey.
Chinese APT40 group swifly leverages public PoC exploits
Chinese state-sponsored cyber group APT40 is amazingly fast at adapting public proof-of-concept (PoC) exploits for vulnerabilities in widely used software, an advisory released by intelligence and cybersecurity agencies from eight countries warns.
Decryptor for DoNex, Muse, DarkRace, (fake) LockBit 3.0 ransomware released
A cryptographic weakness in the DoNex ransomware and its previous incarnations – Muse, fake LockBit 3.0, and DarkRace – has allowed Avast researchers to create a decryptor for files encrypted by all those ransomware variants.
How to design a third-party risk management framework
Most organizations focus on securing routers, servers, firewalls, and other endpoints, but threats can also arise from unfamiliar sources such as third-party networks, which can be used by hackers to attack an organization.
Organizations change recruitment strategies to find cyber talent
An estimated 4 million professionals are needed to fill the growing cybersecurity workforce gap, according to Fortinet.
Travel scams exposed: How to recognize and avoid them
In this Help Net Security video, Aaron Walton, Threat Intel Analyst at Expel, discusses travel scams.
How AI helps decode cybercriminal strategies
With terms like “AI washing” making their way into mainstream business consciousness, the hype surrounding AI is making it harder to differentiate between the true applications and empty promises of the technology.
Cybersecurity jobs available right now: July 10, 2024
We’ve scoured the market to bring you a selection of roles that span various skill levels within the cybersecurity field. Check out this weekly selection of cybersecurity jobs available right now.
Shadow engineering exposed: Addressing the risks of unauthorized engineering practices
Shadow engineering is present in many organizations, and it can lead to security, compliance, and risk challenges. In this Help Net Security video, Darren Meyer, Staff Research Engineer at Endor Labs, discusses why it causes issues and how it should be addressed.
Diversifying cyber teams to tackle complex threats
As cyber threats evolve and increase in volume, traditional approaches for stymieing cyber threats are no longer sufficient.
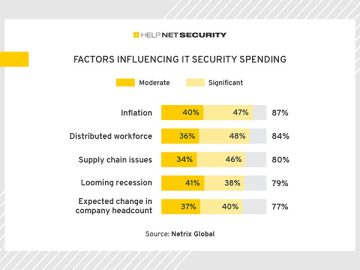
Valuable insights for making the right cybersecurity decisions
This article compiles excerpts from various reports, presenting statistics and insights that could be helpful for CISOs.
New infosec products of the week: July 12, 2024
Here’s a look at the most interesting products from the past week, featuring releases from AttackIQ, IT-Harvest, Pentera, Prompt Security, and Quantum Xchange.