When you find out your P1 is a dupe

Source link
Related Articles
All Mix →IT Security FAQ 1: What should you think about when approving an app on Facebook?
There are all kinds of apps on Facebook – quizzes, games and corporate sweepstakes. But it might be a good idea to keep track of…
Sponsored Interview: Pentera
Daniel Miessler speaks with Aviv Cohen about Pentera’s Automated Security Validation platform, which is similar but different to automated pen testing and attack surface management,…
UL NO. 416: Tracking AI Agent Activity, 400 SF Cameras, AI Sleeper Agents…
Table of Contents TOC INTRO MY WORK TECHNOLOGY HUMANS IDEAS & ANALYSIS NOTES DISCOVERY RECOMMENDATION OF THE WEEK APHORISM OF THE WEEK Continue reading online…
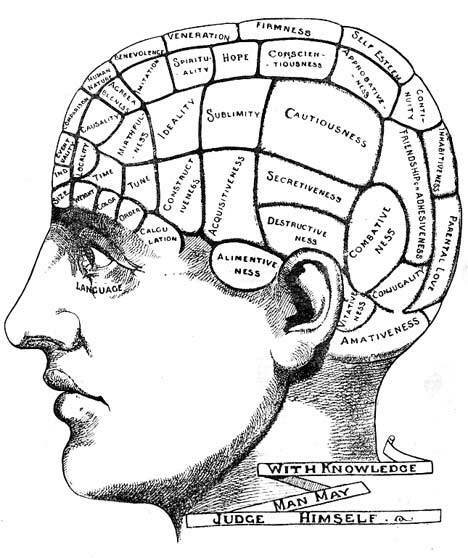
Will Power in Finite Supply
An interesting study has just been published in Psychology and Health that shows that when you restrain yourself emotionally you deplete what seems to be…
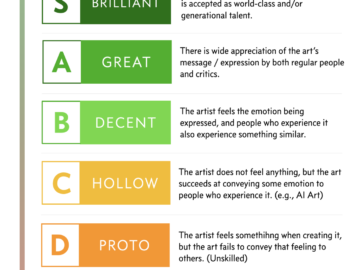
The Art Quality Tier List (AQTL)
I think I just figured out what art is. Took me decades. Here’s my definition, which has two primary components: Indirect expression of something that…
Introducing domains and scan profiles
We have listened to your feedback and renamed scopes and targets to domains and scan profiles. This update is just a name change and does…