Why aren’t you able to do BUG BOUNTIES or Anything?

Source link
Related Articles
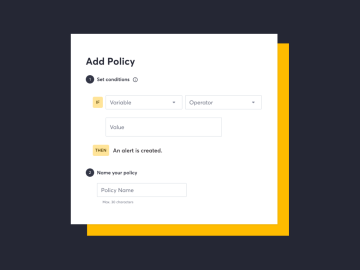
All Mix →Major update to Attack Surface Custom Policies
Table of Contents Set rules on technologies discovered on your attack surface “I’m tasked with ensuring our organization only uses approved technologies on our attack…
Free Burp Suite Professional License For Hackers
Did you know we’ve teamed up with our friends at PortSwigger to offer free 90-day licenses for Burp Suite Professional? Burp Suite is the…
Axiom Scan New Spin Up Options with Whois Module – Apple Passive Recon
Axiom Scan New Spin Up Options with Whois Module – Apple Passive Recon Source link
Exploiting API4 — 8 Real-World Unrestricted Resource Consumption Attack Scenarios (and How to Stop Them) — API Security
Table of Contents Scenario 1: Uploading a Large File Scenario 2: High-Latency Responses Scenario 3: Excessive Response Size (Data Exfiltration) Scenario 4: Financially Impactful API…
How this seasoned bug bounty hunter combines Burp Suite and HackerOne to uncover high-impact vulnerabilities | Blog
Table of Contents Arman S., a full-time independent security researcher and bug bounty hunter, talked us through how he uses Burp Suite Professional and HackerOne…
Q4-2022 API ThreatStats™ Report
We’re pleased to present the latest quarterly review and analysis of API vulnerabilities and exploits. This time, we’re going to split our discussion into two…