Why do you Duplicate so much with Bug Bounties?

Source link
Related Articles
All Mix →Understanding DevSecOps | HAHWUL
Table of Contents What is DevSecOps? Why DevSecOps? How to measure maturity? Resources Conclusion Sharing thoughts and approaches on DevSecOps, which integrates development (Dev), security…
Security@ 2020 Call for Speakers is Open
HackerOne’s global Security@ conference is back for its fourth year. This year’s virtual event will take place October 20-22, 2020. Today, we’ve opened our call…
Connecting to Serial Ports from OS X
Get yourself a quality USB-to-serial connector. I bought a TU-S9 myself, and it’s worked flawlessly. Install its driver and reboot. You’ll now have a device…
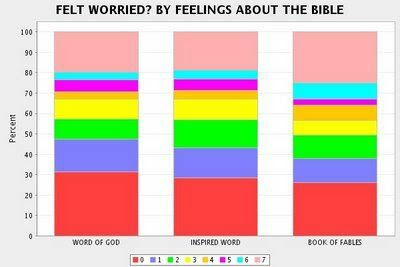
Believers Worry Less Than Non-Believers
This is an interesting piece over at the Audacious Epigone. It shows that the deeply religious worry the least, which makes perfect sense to me.…
Recap: Experts Break Down AI Red Teaming in a Live Q&A
Table of Contents Key Terminology and Concepts Q: What is AI red teaming? Q: What is prompt injection vs. jailbreaking? Q: What is API hacking?…
No, It’s Not Just “Those People” Who Current Healthcare is Failing
62% of bankruptcies are from medical bills. Most medical debtors are well educated and middle class. Three quarters of those who filed bankruptcy had health…