Nineteen years is a long time to watch an industry transform — and Jennifer Cox has had a front-row seat to all of it.
Two decades ago, cybersecurity barely made it onto the agenda. Today it sits at the top of it. Cox has worked through every stage of that change — across communication strategy, cloud security, global program delivery, and now security automation.
As Director of Solutions Engineering at Tines, she works at a practical intersection: helping organizations cut through the noise of over-engineered tools and actually automate security workflows in ways that stick. It’s less about the technology and more about getting the people, processes, and priorities aligned — something Cox has spent the better part of her career figuring out.
A Bronze Stevie Award winner and recognised across multiple industry honours, she measures success not in tools deployed but in whether security teams are operating with less chaos and whether boards finally understand what they’re being asked to fund.
In this interview, Cox talks about the real barriers to security automation, how teams can stop drowning in alerts, what it takes to speak the board’s language, and why women in cybersecurity should stop waiting to feel ready.
Read Full Interview


Jennifer Cox Interview: The Human Side of Automation
TCE: You have nearly two decades of experience across cybersecurity, communication strategy, and global program delivery. What key changes in the cybersecurity landscape have most influenced how organizations approach security today?
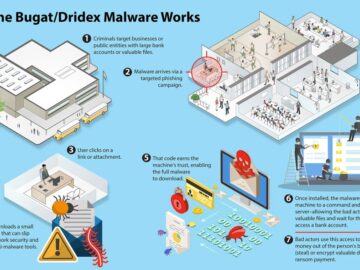
Jennifer Cox: Over nearly two decades, the biggest shift I’ve seen is that cybersecurity has moved from “IT problem” to business risk that boards and regulators actively care about. The rise of ransomware, supply chain attacks, and SaaS sprawl means security is now tightly linked to revenue continuity, brand, and trust.
At the same time, the attack surface has exploded: cloud, remote work, APIs, identities, and third parties have made traditional perimeter thinking obsolete. That’s forced organisations to move from reactive, tool‑centric security to more proactive, automated, and outcomes‑driven programs that tie controls to real business processes.
TCE: In your role at Tines, you work closely with organizations implementing security automation. What are the biggest operational challenges security teams face when trying to automate their workflows?
Jennifer Cox: When I work with teams on automation, the tech is rarely the hardest part; it’s people and process. Many SOCs are stuck in “semi‑automation” mode, where analysts still babysit workflows and manually approve every decision, so they never see the real benefits.
The other big challenge is skills and ownership: you need people who understand both the security problem and how to design reliable automated workflows. Without that, you end up with brittle playbooks, over‑engineered logic, and fear of “breaking production,” which slows everything down.
TCE: Security automation is often positioned as a way to reduce alert fatigue and improve response times. From what you’ve seen, where are organizations gaining the most measurable benefits from automation today?
Jennifer Cox: The most measurable wins I see today are in three areas: alert handling, investigations, and compliance. Automating enrichment, correlation, and deduplication can cut the number of alerts reaching humans by the majority, which directly reduces fatigue and backlog.
On the investigation side, well‑designed workflows shrink time‑to‑conclusion from hours to minutes by gathering evidence, checking context, and making initial determinations automatically. And in governance and compliance, automating evidence collection, control checks, and risk workflows saves huge amounts of manual effort and audit pain.
TCE: Many organizations invest heavily in security tools but still struggle with complexity and integration. What should security leaders look for when evaluating automation platforms to ensure they deliver real operational value?
Jennifer Cox: Security leaders should stop buying “feature lists” and start buying outcomes. I’d look for platforms that are easy enough for your analysts to own day‑to‑day, integrate cleanly with your existing tools, and make it simple to iterate on workflows as your environment changes.
You also want strong guardrails: testing, version control, approval paths, and observability so you can trust automation in production. Finally, pay close attention to how the platform handles failure modes and exceptions; resilient error handling is the difference between “nice demo” and genuine operational value.
TCE: You specialize in bridging complex technical solutions with business outcomes. How can security teams better communicate the value of cybersecurity investments to executive leadership and boards?
Jennifer Cox: Security teams need to translate technical noise into business‑relevant stories. That means moving away from raw counts of alerts or vulnerabilities and focusing on metrics like reduction in high‑risk exposure, time to contain business‑critical incidents, or improved uptime for key services.
I encourage teams to tie every major initiative to a clear narrative: what business process it protects, which risk or regulatory obligation it addresses, and what would happen if we didn’t do it. Executives don’t need every detail of the exploit chain; they need to understand impact, options, and confidence levels so they can make informed decisions.


TCE: As cloud adoption continues to grow, how has the role of solutions engineering evolved in helping organizations maintain strong security and compliance frameworks?
Jennifer Cox: As cloud adoption has grown, solutions engineering has shifted from “here’s how the product works” to “here’s how this fits into your entire security and compliance ecosystem.” You’re no longer just doing feature demos; you’re co‑designing architectures that span multiple clouds, SaaS platforms, and regulatory regimes.
It also means being comfortable speaking both Kubernetes and boardroom. You’re often the translator between engineering, security, legal, and the business, making sure that what’s being built is secure, automatable, and actually usable by the teams who’ll live with it every day.
TCE: Security teams today operate under constant pressure from growing threat volumes and limited resources. What strategies can help organizations build more resilient and efficient security operations?
Jennifer Cox: Resilient security operations start with being ruthless about focus. Not every alert or control is created equal, so prioritisation and risk‑based workflows matter more than ever. Automation should handle repetitive, low‑risk work so humans can focus on complex investigations, threat hunting, and continuous improvement.
I also push teams to build in recovery as a feature: runbooks, tabletop exercises, and post‑incident reviews that feed back into updated playbooks and automations. Over time, this closes the loop; every incident makes your people, your processes, and your automation a little sharper.
TCE: Having led global programs and cross-functional teams, what leadership approaches have helped you align technical teams with broader business objectives?
Jennifer Cox: Leading global and cross‑functional teams, I’ve found that clarity plus autonomy beats command‑and‑control every time. If people understand the “why” behind an objective and how it ties to the business, they’ll usually find better ways to get there than anything you could script.
I focus on three things: listening hard first, co‑creating goals with the team, and being transparent about trade‑offs. That creates psychological safety, which is essential in security, because you want people to surface bad news early, challenge assumptions, and admit when something isn’t working.
TCE: As we mark International Women’s Day, what meaningful progress have you seen in the representation and leadership of women in cybersecurity over the years?
Jennifer Cox: We’ve seen meaningful progress, but it’s been a grind, not a fairy tale. Women now hold a growing share of managerial and CISO roles globally, and more are in hiring and budget‑owning positions than even a few years ago. We’re also seeing increased funding and visibility for women‑led cybersecurity companies, communities, and initiatives.
At the same time, representation at the very top; C‑suite and board level; is still far too low, and retention remains a challenge. So I’d describe the moment as “real momentum with plenty of unfinished work,” which is why I stay so active in communities like WiCyS and mentoring
TCE: For women looking to build long-term careers in cybersecurity and technical leadership, what advice would you share based on your own journey in the industry?
Jennifer Cox: First, you absolutely belong here; even if you don’t look like the stereotype of a security professional. Don’t wait to feel “ready” before you go for the role, the talk, or the promotion; my own career is full of moments where I said yes, panicked a little, and then grew into it. Second, build your support system as intentionally as you build your skills: mentors, sponsors, peers, and communities that will advocate for you when you’re not in the room. And finally, protect your energy; burnout and bias are real, but so is your right to step away from unhealthy environments and choose spaces where you can actually thrive.