WHY YOU SUCK AT HACKING // How To Bug Bounty

Source link
Related Articles
All Mix →NCSC Recognises The Work Of Ethical Hackers With An Appreciation Event
The NCSC’s VRS Journey Since 2018, 844 hackers have submitted vulnerabilities to the NCSC’s VRS. The NCSC invited a selection of those hackers who have…
Cybernoz
3 min read
What’s the difference between Attack Surface Monitoring and Vulnerability Scanning?
Table of Contents What are the different types of vulnerability scanning? A growing tech stack and fast development widen the attack surface What is attack…
Cybernoz
6 min read
INTERVIEW WITH @_BASE_64 : 19 Y/o | TOP 150 WORLDWIDE on H1 | METHODOLOGY, MINDSET & MORE…
INTERVIEW WITH @_BASE_64 : 19 Y/o | TOP 150 WORLDWIDE on H1 | METHODOLOGY, MINDSET & MORE… Source link
Cybernoz
1 min read
AI Solution Factories | Daniel Miessler
Everyone is trying to figure out whether developers are screwed or not. Some say they are, and others say more AI just means more need…
Cybernoz
4 min read
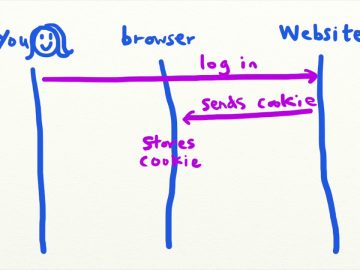
Intro to CSRF (Cross-Site Request Forgery) – Security Simplified
Intro to CSRF (Cross-Site Request Forgery) – Security Simplified Source link
Cybernoz
1 min read
AI Is Worse If You Think It’s Someone’s Fault
I am troubled by how many people are upset by AI. I mean, they’re really upset. Having just written a thing on framing, I think…
Cybernoz
4 min read