Over 90,000 websites are currently at risk due to a vulnerability found in the WordPress Backup Migration Plugin. This vulnerability has enabled unauthenticated remote code execution, making it possible for potential attackers to gain access to these websites.
A group of researchers from Nex Team discovered the vulnerability while participating in the Wordfence Bug Bounty program.
It’s worth noting that the CVE-2023-6553 vulnerability, which allows for remote code execution, has been assigned a critical severity score of 9.8.
This vulnerability allows arbitrary PHP code to be injected and executed by unauthenticated threat actors on WordPress sites that use this plugin.
The Backup Migration plugin for WordPress has a vulnerability in all versions up to and including 1.3.7, which allows attackers to execute remote code.
The vulnerability is present in the /includes/backup-heart.php file, making it possible for attackers to gain unauthorized access to sensitive data and execute malicious code on the website.
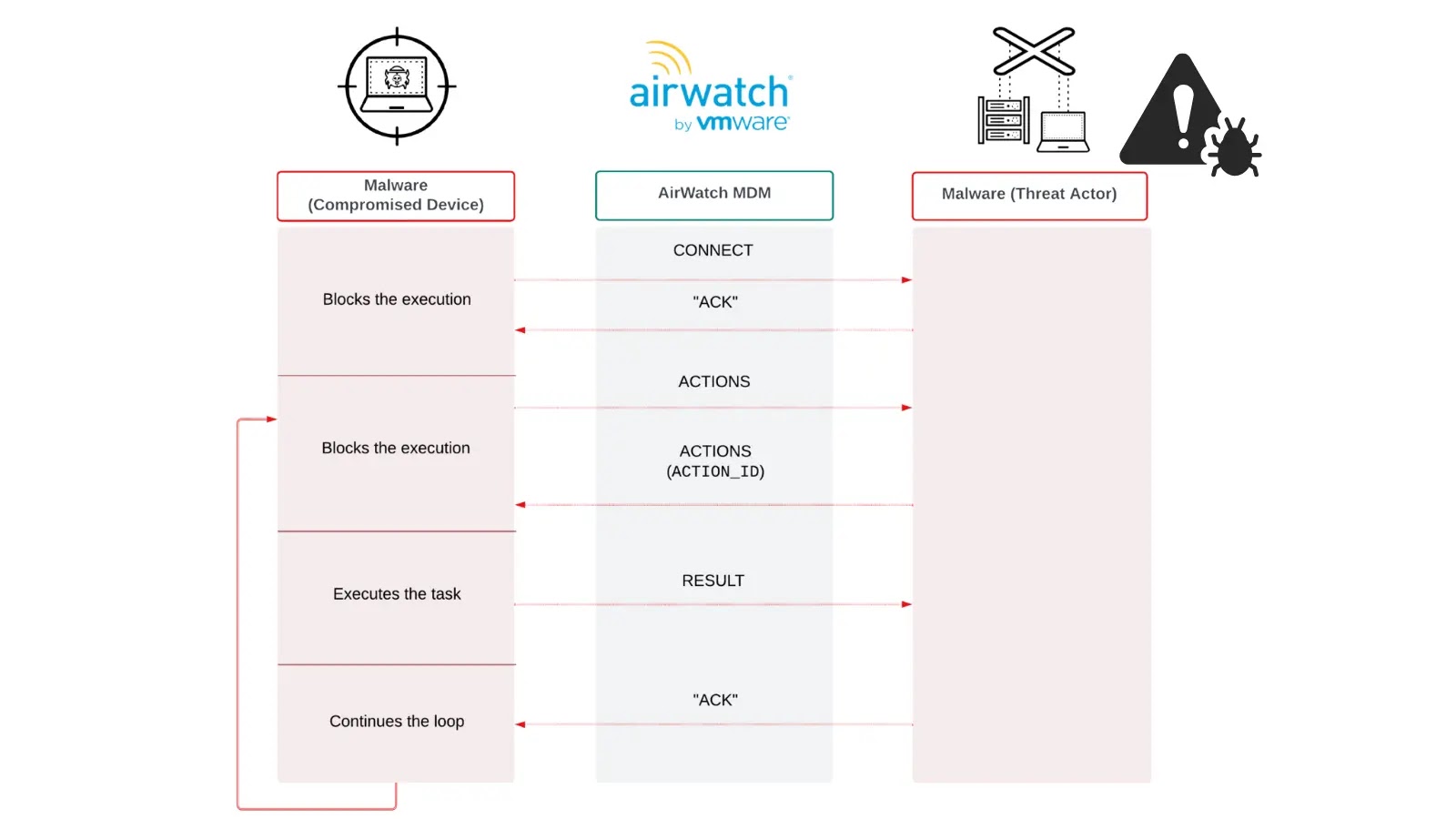
Suppose an attacker gains control of a target computer through some vulnerability and gains the power to execute commands on that remote computer. In that case, this process is called Remote Code Execution (RCE).
This indicates that BMI_ROOT_DIR is modifiable by the user. Threat actors can use this vulnerability to insert malicious PHP code into requests and run arbitrary commands on the underlying server under the WordPress instance’s security context.
After the incident, a new version, 1.3.8, was released that included a patch to address the issue.
It is recommended to update the plugin to the latest version as soon as possible to prevent exploitation of this vulnerability.