
Would you prefer a password-less login? #cybersecurity #shorts

Source link
Related Articles
All Mix →What’s Intigriti’s impact and position?
You asked, and we answered. At Intigriti, we’ve been paying close attention to the questions most frequently asked by those with a bug bounty program…
OWASP API Security Top-10 for 2023 Risk Ratings
As you know by now, the final version of the OWASP API Security Top-10 2023 has been released. At first blush, the final 2023 release…
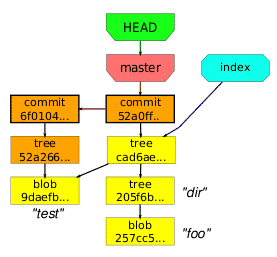
Git: Ignore WordPress Cache Files using .gitignore
I’ve had a nagging problem for some time where I couldn’t figure out quite how to ignore my wp-content/cache directory when doing syncs with git.…
[tl;dr sec] #271 – Threat Modeling (+ AI), Backdoored GitHub Actions, Compromising a Threat Actor’s Telegram
Table of Contents Threat modeling (with) LLMs, tj-actions woes, reading a threat actor's Telegram C2 Working on Your Personality AppSec Cloud Security Supply Chain Blue…
New Ways to Use HackerOne
We are on a mission to empower the world’s hackers and security teams to fix software vulnerabilities together. Since HackerOne was founded in 2012, our…
Cyber Security Reporting | Is Public Disclosure the Right Choice?
Table of Contents Public Disclosure on HackerOne Control the Message Disclosure For Your Needs There are over 1,600 publicly disclosed vulnerability reports on the HackerOne…

![[tl;dr sec] #271 - Threat Modeling (+ AI), Backdoored GitHub Actions, Compromising a Threat Actor's Telegram](https://image.cybernoz.com/wp-content/uploads/2025/03/1743072871_tldr-sec-271-Threat-Modeling-AI-Backdoored-GitHub.png)
