Yorkshire Post Building Demolition #4

Source link
Related Articles
All Mix →Ambassador Spotlight: samux | HackerOne
Table of Contents What made you want to become an ambassador? Why do you think people should join this program? What is your role as…
Game On! Adding Privacy to Threat Modeling
Table of Contents Elevation of Privilege: Background Elevation of Privilege: Why a Game? Elevation of Privilege: How to Play The Privacy Extension OH HAI! Another…
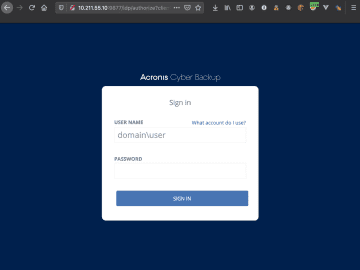
Exploiting Acronis Cyber Backup for Fun and Emails – RCE Security
Table of Contents CVE-2020-16171: Exploiting Acronis Cyber Backup for Fun and Emails Root Cause Analysis Finding Unauthenticated Routes Sending Fully Customized Emails Including An Attachment…
Why Religion is More Dangerous Than Handguns
We’ve been debating agnosticism and atheism here for the last couple of weeks. One of the sub-arguments that has pronounced itself has come from my…
Solving the challenges of a bug bounty program manager (BBPM). Strategic execution for security leaders.
As more organizations lean on third-party platforms, cloud infrastructure, and remote development teams, the attack surface grows, often faster than internal security teams can manage.…
Continuously Hack Yourself because WAF security is not enough
Table of Contents WAF’s Got My Back… right? Scanners Gonna Scan Signatures vs. Payloads Trusting ethical hackers to help verify relevant vulnerabilities How to Continuously…