Your Guide to Burp

Source link
Related Articles
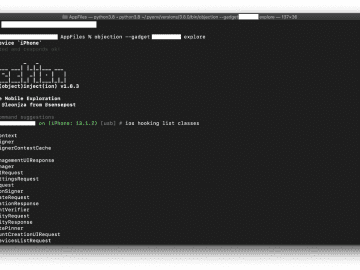
All Mix →Low-Hanging Apples: Hunting Credentials and Secrets in iOS Apps
Diving straight into reverse-engineering iOS apps can be daunting and time-consuming. While wading into the binary can pay off greatly in the long run, it’s…
Are Creativity and Materialism Opposites?
I’ve been thinking a lot about what matters in life recently–specifically about focusing in on the things that matter, and trimming much of the rest.…
One Apple Fanboy’s White-hot Anger at the iPad Commercial
Before I go into this, I want to articulate exactly how much of an Apple fanboy I am. I camped for the first iPhone I…
Why Your Website Needs a “Discovered Content” Section
Table of Contents Setup 1. Friendfeed 2. Filter the Data 3. Massage the Data 4. Make It Available to Your Users Setup Help One of…
The Top 5 Most Common Security Issues I Discover When Reviewing Code
Table of Contents 1. Sensitive Information in Log Files 2. Poor Cryptography Choices 3. Insufficient Access Controls 4. Unsecured Caches 5. Trusting the Client Too…
My first OOB XXE exploitation
Table of Contents Recon Never trust user input application message Exploitation Digging Conclusion Recently on a BugBounty program I came across my first XXE, blind…