Zara Data Breach: 197,000 Customers Exposed in Third-Party Security Incident

Nearly 200,000 Zara customers were exposed in a third-party breach linked to ShinyHunters, revealing emails, purchase history, and support data.
Personal data belonging to nearly 197,000 Zara customers has been compromised following a cyberattack on a former technology provider used by Inditex, the Spanish fashion giant behind some of the world’s most recognized retail brands including Bershka, Pull&Bear, and Massimo Dutti.
The breach came to light last month when Inditex confirmed unauthorized access to databases hosted by a third-party vendor. The company was careful to limit the alarm: the compromised databases did not contain names, passwords, payment details, addresses, or phone numbers.
“Inditex has immediately applied its security protocols and has started notifying the relevant authorities of this unauthorized access, that stems from a security incident that affected a former technology provider and has impacted several companies operating internationally,” reads a statement by Inditex.
“Operations and systems haven’t been affected and customers can continue to access and use its services safely,”
What was exposed, however, tells a different story about the scale of the incident.
The data breach notification service Have I Been Pwned analyzed the stolen dataset and confirmed that 197,400 unique email addresses were among the compromised records, alongside order IDs, product SKUs, geographic locations, purchase history, and customer support tickets, enough to paint a detailed picture of individual shopping habits and interactions with the brand.
“In April 2026, the fashion brand Zara was among a number of organisations targeted by the ShinyHunters extortion group as part of their “pay or leak” campaign. The group claimed the breach was related to a compromise of the Anodot analytics platform and subsequently published a terabyte of data allegedly including 95M support ticket records.” reads the alert by HIBP. “The data contained 197k unique email addresses alongside product SKUs, order IDs and the market the support ticket originated in. Zara’s parent company Inditex advised that the incident didn’t affect passwords or payment information.”
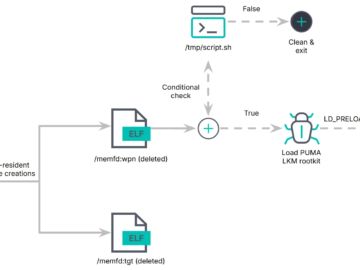
The extortion group ShinyHunters claimed the attack and the theft of a 140GB archive from BigQuery instances by exploiting compromised Anodot authentication tokens, the same technique they have used against dozens of other companies.
“Your Bigquery instances data was compromised thanks to Anodot.com.” the cybercrime group wrote on its Tor data leak site. “The company failed to reach an agreement with us despite our incredible patience, all the chances”

ShinyHunters has previously claimed breaches at Google, Cisco, Vimeo, Rockstar Games, Instructure, and the European Commission.
The Anodot vector is significant. ShinyHunters has told journalists that stolen Anodot tokens gave them access to analytics infrastructure across multiple large organizations simultaneously, a single point of failure that cascaded into dozens of separate breaches. The gang has also run coordinated vishing campaigns targeting employees’ SSO accounts at Microsoft Entra, Okta, and Google to move laterally into connected SaaS environments.
Inditex has not yet named the compromised provider or attributed the attack to a specific threat actor, despite ShinyHunters having publicly claimed it and released data as proof.
Zara is the flagship fashion brand of Inditex, one of the world’s largest apparel groups. Inditex reported revenue of about €38.6 billion in fiscal 2025 and employs roughly 160,000 people worldwide. Zara operates in more than 90 countries through thousands of stores and online platforms, making it one of the most globally recognized fast-fashion retailers.
Rival retailer Mango disclosed its own data breach last October, after a marketing vendor was hacked and customer data used in promotional campaigns was exposed. In that case, no extortion group has come forward, and the attackers remain unidentified.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, data breach)