The United States has intensified its response to zero-day exploits theft, announcing new sanctions against a Russia-linked cyber tools network accused of stealing sensitive U.S. trade secrets and attempting to sell advanced cyber capabilities to foreign actors.
The U.S. Department of State designated one individual and two entities under the Protecting American Intellectual Property Act (PAIPA), targeting a cyber exploit brokerage operation operating under the name Operation Zero.
Officials say the case reflects a dangerous shift where stolen vulnerabilities—once tightly controlled by governments—are increasingly being traded for cryptocurrency through private intermediaries.
The Zero-Day Exploits Theft Scheme
According to U.S. authorities, the zero-day exploits theft operation began when Peter Williams, an Australian national, allegedly stole eight classified trade-secret exploits from a U.S. defense contractor between 2022 and 2025. These zero-day exploits—software vulnerabilities with no available patches—were intended exclusively for U.S. government and allied use.
Instead, investigators say Williams sold the stolen exploits to Operation Zero for approximately $1.3 million in cryptocurrency payments.
The scale and nature of the breach raise deeper questions about insider threats in the cybersecurity ecosystem. While external hackers often dominate headlines, this case demonstrates how internal access remains one of the most dangerous vulnerabilities in modern cyber defense.


Zero-day exploits are particularly valuable because they allow attackers to bypass traditional security protections. When such tools fall into unauthorized hands, the consequences can affect national security, corporate infrastructure, and global digital trust.
Russian Cyber Tools Broker at the Center of Trade Secrets Theft
Authorities also sanctioned Sergey Sergeyevich Zelenyuk, a Russian national identified as the director and owner of Operation Zero. Investigators say Zelenyuk attempted to expand operations internationally by establishing a UAE-based entity called Special Technology Services LLC FZ (STS).
Officials believe the move was designed partly to bypass existing financial restrictions on Russian-linked cyber activity.
The United States Department of the Treasury simultaneously issued sanctions under Executive Order 13694, targeting Zelenyuk, Operation Zero, STS, and additional affiliated entities.
As a result, any property or financial interests connected to the sanctioned individuals within U.S. jurisdiction are now blocked, and U.S. persons are prohibited from conducting business with them.
The sanctions also send a broader message: cyber exploit marketplaces—especially those operating across borders—are now being treated as national security threats rather than purely criminal enterprises.
Why Zero-Day Exploits Theft Is Becoming a Global Security Concern
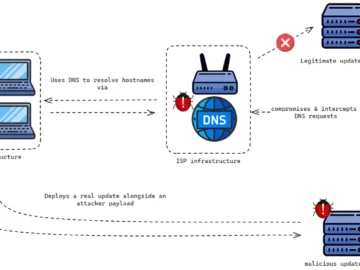
The latest enforcement action reflects a larger trend in the cyber threat landscape. Zero-day exploits theft is no longer limited to espionage operations conducted quietly between rival nations. Instead, a growing ecosystem of brokers, intermediaries, and private cyber vendors is commercializing vulnerabilities for profit.
This commercialization makes cyber risks harder to control. Once a zero-day exploit enters the underground or gray market, it can be reused, resold, or weaponized by multiple actors—including ransomware groups and state-backed hackers.
The U.S. government’s response signals a shift toward targeting the financial and supply-chain infrastructure behind cybercrime, not just the attackers themselves.
However, sanctions alone may not be enough.
The case highlights three ongoing challenges:
- Insider threats remain difficult to detect until damage is done.
- Cryptocurrency continues to enable cross-border cyber transactions.
- Exploit brokerage markets are expanding faster than regulatory frameworks.
In many ways, zero-day exploits theft represents the convergence of cybercrime, cyber espionage, and global digital commerce.
Sanctions Are a Start—But the Cyber Exploit Market Is Growing
The action against Operation Zero is significant, but it also underscores how mature the cyber exploit economy has become. Brokers are now operating openly, marketing vulnerabilities like products and building international networks to avoid enforcement pressure.
Without stronger global coordination and stricter controls around vulnerability sales, cases like this are likely to increase.
The message from U.S. authorities is clear: intellectual property theft tied to cyber weapons will trigger real economic consequences. But the evolving marketplace for exploits suggests the fight against zero-day exploits theft is only entering its next phase.