ZeroDayRAT targets Android and iOS devices, combining real-time surveillance with direct financial theft within a single browser panel.
The Malware-as-a-Service (MaaS) ecosystem is entering a new phase, blending mobile surveillance and financial crime into one seamless platform.
Active promotions for this RAT (Remote Access Trojan) began on Telegram channels on February 2, 2026, highlighting its dual purpose: real-time spying and direct financial theft through an easy-to-use browser dashboard.
After purchasing access via Telegram, the attacker deploys an infected APK (for Android) or a malicious payload (for iOS). Once installed, the malware offers full control over the victim’s device, including live feeds, communications, and banking activity.
ZeroDayRAT is designed to compromise every layer of a target’s mobile ecosystem digital behavior, physical surroundings, and finances.
Researchers from Cyberthint have uncovered a new mobile spyware service, ZeroDayRAT, which enables even non-technical actors to perform advanced spying and theft operations on both Android and iOS devices.
Infection Vectors and Control Panel Access
The RAT predominantly spreads through Smishing campaigns fraudulent SMS messages impersonating legitimate service providers or app updates. Attackers also distribute fake versions of popular apps via WhatsApp, Telegram, and rogue app stores.
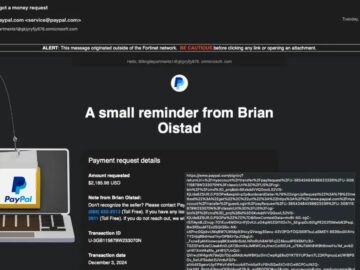
Once a device is compromised, the attacker accesses a user-friendly web control panel compatible with the latest OS versions (Android 16 and iOS 26.2).

This unified interface provides a digital profile of the victim, displaying the device model, carrier, most-used apps, and even the last SMS interactions.
ZeroDayRAT transforms a compromised phone into a live surveillance device. Through the control panel, the actor can track GPS coordinates in real-time, monitor location history, and remotely activate the camera and microphone.
It supports ambient listening and screen recording, turning the device into a 24/7 spy tool.Its integrated keylogger captures every keystroke and biometric input with millisecond precision.
Clipboard data and app transition logs are also exfiltrated to the command panel, enabling complete behavioral analysis.
The RAT’s financial theft modules are designed for direct revenue generation. Using Clipboard Injection, it hijacks cryptocurrency transfers by replacing copied wallet addresses from apps like Binance, MetaMask, and Trust Wallet with the attacker’s own.
Moreover, Overlay Attacks impersonate login screens for Apple Pay, Google Pay, PayPal, and local banking apps to harvest credentials.
ZeroDayRAT is sold under a tiered subscription: $250 daily, $1000 weekly, or $3500 monthly.
Threat researchers confirmed through Telegram conversations that the seller uses XSS Forum’s Escrow service, a sign of legitimacy uncommon among scam vendors. This practice implies the RAT is fully operational and backed by a functioning criminal network.
Integrated OTP interception captures two-factor authentication codes from SMS, enabling real-time bypasses of security controls.
Technical Observations and Credibility
While evidence suggests that ZeroDayRAT poses a genuine risk, analysts spotted anomalies during review.

A screenshot from its alleged cryptocurrency theft module displayed a suspicious browser tab label “Create USDT Wallet Address”, likely part of a mock-up or reused demo footage. This inconsistency raises partial doubts about the full capability set advertised.
ZeroDayRAT represents the shifting axis of threat evolution enabling cybercriminals to perform state-grade espionage via renting ready-made kits.
It joins a growing wave of mobile-centric malware families, including Anatsa, Arsink, and NFCShare, that exploit everyday digital habits to infiltrate user data and finances.
As mobile RATs mature, enterprises and users must remain vigilant against Smishing schemes and unknown app installations, reinforcing that the biggest threats often arrive via the smallest clicks.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.