Taiwan networking provider Zyxel has released security updates to address a critical vulnerability affecting over a dozen router models that can allow unauthenticated attackers to gain remote command execution on unpatched devices.
Tracked as CVE-2025-13942, this command injection security flaw was found in the UPnP function of Zyxel 4G LTE/5G NR CPE, DSL/Ethernet CPE, Fiber ONTs, and wireless extenders.
Zyxel says that unauthenticated remote attackers can exploit it to execute operating system (OS) commands on an affected device using maliciously crafted UPnP SOAP requests.

However, CVE-2025-13942 attacks will likely be more limited than the severity rating suggests, as successful exploitation requires UPnP and WAN access to be enabled, with the latter disabled by default.
“It is important to note that WAN access is disabled by default on these devices, and the attack can be carried out remotely only if both WAN access and the vulnerable UPnP function have been enabled,” Zyxel said. “Users are strongly advised to install the patches to maintain optimal protection.”
On Tuesday, Zyxel also patched two high-severity post-authentication command-injection vulnerabilities (CVE-2025-13943 and CVE-2026-1459) that allow threat actors to execute OS commands using compromised credentials.
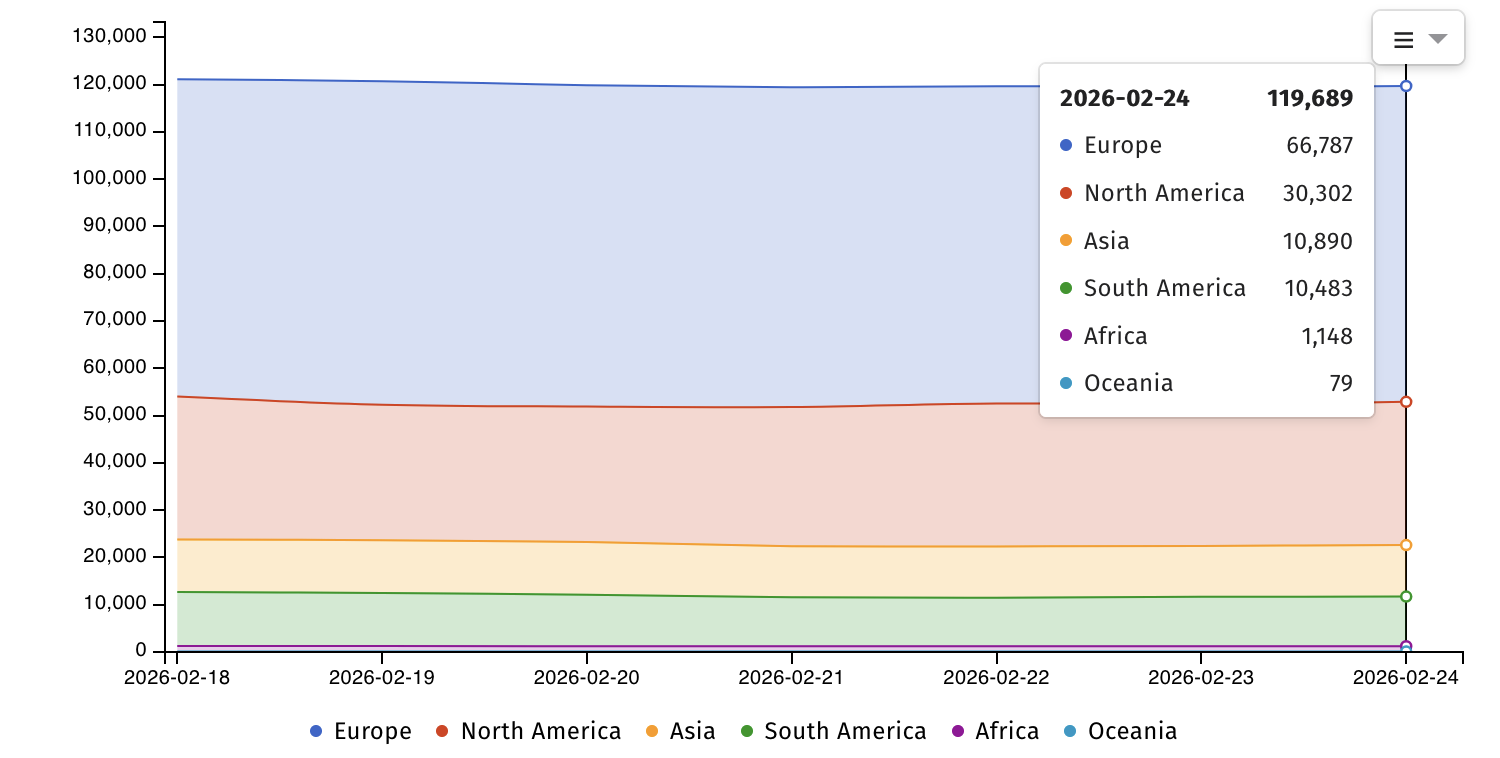
Internet security watchdog Shadowserver currently tracks nearly 120,000 Internet-exposed Zyxel devices, including over 76,000 routers.
Zyxel devices are often targeted in attacks since they’re provided by many internet service providers worldwide as the default out-of-the-box equipment when activating a new internet service contract.
The U.S. Cybersecurity and Infrastructure Security Agency (CISA) is currently tracking 12 Zyxel vulnerabilitiesimpacting the company’s routers, firewalls, and NAS devices that have been or are still actively exploited in the wild.
Earlier this month, Zyxel warned that it has no plans to patch a pair of zero-day security vulnerabilities (CVE-2024-40891 and CVE-2024-40891) that are actively exploited in attacks and affect end-of-life routers still available for sale online. Instead, the company “strongly” advised customers to replace their routers with newer products whose firmware has already been patched.
“VMG1312-B10A, VMG1312-B10B, VMG1312-B10E, VMG3312-B10A, VMG3313-B10A, VMG3926-B10B, VMG4325-B10A, VMG4380-B10A, VMG8324-B10A, VMG8924-B10A, SBG3300, and SBG3500, are legacy products that have reached end-of-life (EOL) for years,” said Zyxel. “Therefore, we strongly recommend that users replace them with newer-generation products for optimal protection.”
Zyxel claims that more than 1 million businesses use its networking products across 150 markets.

Modern IT infrastructure moves faster than manual workflows can handle.
In this new Tines guide, learn how your team can reduce hidden manual delays, improve reliability through automated response, and build and scale intelligent workflows on top of tools you already use.