A coordinated malware operation is abusing fake GitHub repositories to distribute a LuaJIT-based loader, SmartLoader, and a follow-on StealC infostealer, with at least 109 malicious repos active across 103 accounts.
The campaign blends cloned open source code, obfuscated Lua stages, and blockchain-backed C2 resolution to evade detection and keep infrastructure agile.
Instead of relying on GitHub releases, the actor embedded a ZIP archive deep in the repository, then rewrote the README to push users toward that hidden download.
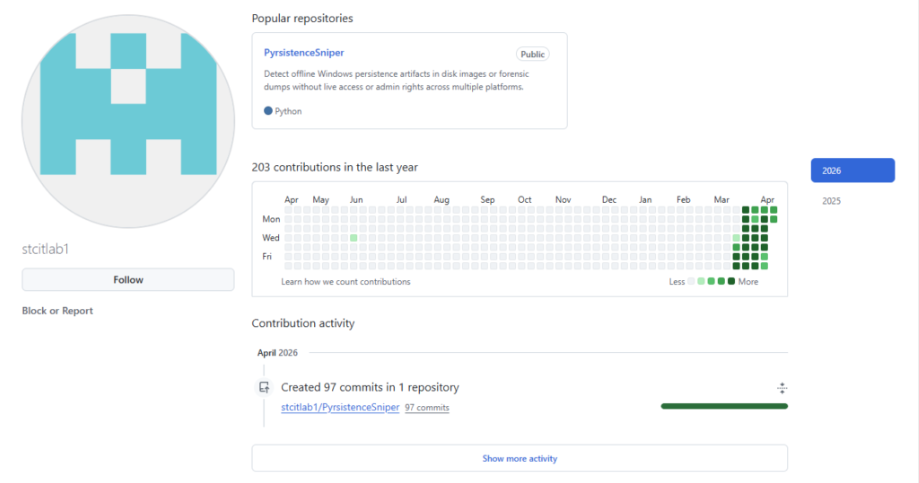
As of 2026-04-12, at least 109 malicious repositories across 103 GitHub accounts follow this pattern, indicating a scaled, automated ecosystem rather than a one-off copycat.
The timeline of ZIP timestamps, PE compilation times, and commit history shows the activity stretching for at least seven weeks, with new repositories still being created through early April 2026.
The operation began with the discovery of a trojanized clone of a legitimate security project on GitHub, where the attacker copied the full source tree but rewired the delivery path.
Multiple accounts host several malicious projects in parallel, and contribution activity appears in tight bursts, suggesting centralized tooling that can update lures and links in batches.
Infrastructure reuse, consistent staging layouts, and uniform SmartLoader behavior collectively point to a single operator or a tightly coordinated cluster.
Fake GitHub repositories as a lure
The attacker’s lure relies on search visibility and user trust in trending open source tools. Newly popular repositories with rising stars are cloned under fresh accounts, preserving filenames and code so that casual inspection still looks legitimate.
The README is heavily modified: detailed installation steps and technical notes are stripped, replaced with large shields.io-style “Download” badges and colored markdown buttons that all resolve to the same embedded ZIP path.
Repository descriptions and topics are also tuned, sometimes with unrelated SEO terms, to help fake copies sit alongside originals in GitHub search results.
The embedded archives live under paths that resemble normal build artifacts (for example, nested “project-name-version.zip”), which helps them blend into the tree.
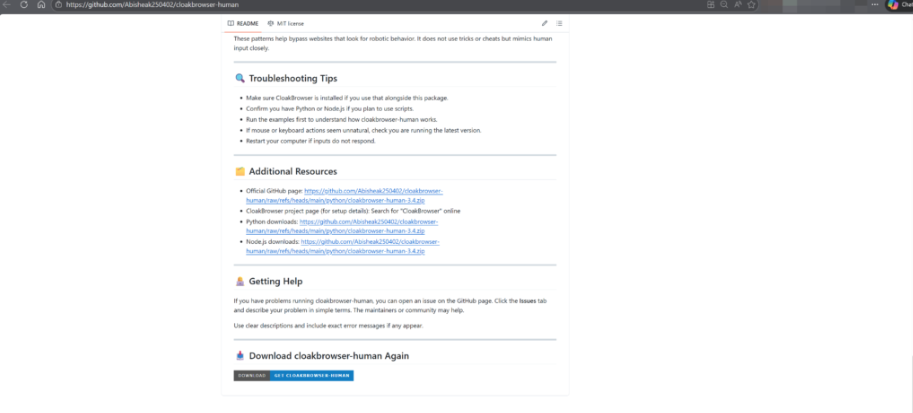
This combination realistic code, aggressive download prompts, and buried ZIPs creates an effective social engineering funnel for developers and security researchers alike.
Each malicious ZIP typically contains three or four files: a one-line batch launcher, a renamed LuaJIT 2.1.0-beta3 GUI executable, an optional lua51.dll, and an obfuscated Lua script stored under a benign .txt or .log name.
The batch file invokes the interpreter with the payload, using the Windows “start” command and a GUI subsystem binary so no console window appears. Across variants, filenames are cosmetic (loader.exe, unit.exe, boot.exe, java.exe) but the execution model remains stable.
The Lua payload is a single-line, Prometheus-obfuscated SmartLoader script roughly 300 KB in size, with arithmetic-masked constants, encoded strings, randomized identifiers, and a VM-style dispatcher to frustrate analysis.
At runtime, SmartLoader uses LuaJIT’s FFI to declare Windows structures and APIs, then hides its console window, performs anti-debug checks, fingerprints the host, captures screenshots through GDI, and prepares for follow-on tasking.
The script also defines PE parsing structures and thread-creation primitives, enabling in-memory loading of additional PE payloads without touching disk.
Blockchain-backed C2 and StealC delivery
Instead of hardcoding C2 endpoints, SmartLoader queries a Polygon smart contract via JSON-RPC eth_call to polygon.drpc.org, using a fixed contract address and selector that act as a dead drop resolver.
The pattern may reflect the operator’s routine maintenance workflow, including repeated README and link updates across staged repositories, rather than meaningful long-term development activity.
The contract returns an encoded string containing the current C2 URL, which the loader decodes to reach bare-IP HTTP endpoints in a single /24 block.
By changing on-chain data rather than binaries, the operator can rotate infrastructure without rebuilding every staged sample.
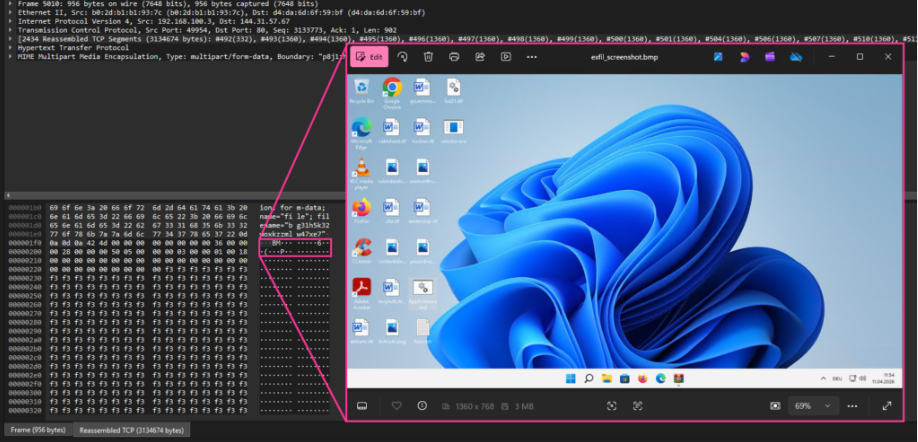
Once a server is resolved, SmartLoader sends multipart/form-data POST requests to /api/
The response contains encrypted “loader” instructions and a “tasks” list, which the malware decrypts in memory and executes; task completion is reported back via POST /task/
In parallel, SmartLoader reaches out to attacker-controlled GitHub repositories hosting encrypted blobs that decrypt into a redundant Lua stage and a packed StealC PE, which the loader reflectively executes using its built-in PE loader.
Persistence is maintained via two scheduled tasks that masquerade as benign software (for example, audio managers or Office components) and point to binaries and Lua stages stored under %LOCALAPPDATA%.
One task executes a cached copy of the Lua stage to survive takedowns of the original GitHub repo, while the other re-downloads a fresh encrypted stage from GitHub on each run to recover from local cleanup.
Defenders can hunt for several high-signal behaviors: unsigned LuaJIT binaries launched via batch files with .txt or .log arguments from user-writable paths, unexpected Lua runtimes or lua51.dll loading from %TEMP% or %LOCALAPPDATA%, non-browser JSON-RPC calls to Polygon endpoints, SmartLoader’s specific smart contract eth_call patterns.
Preventive controls include stricter validation of GitHub sources, blocking unsigned interpreters from user directories, inspecting GitHub raw traffic, and limiting access to blockchain RPC endpoints from non-development systems.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.