A group of China-linked hackers known as Mustang Panda has expanded its spying efforts to target the Indian financial sector and political circles in South Korea. The Acronis Threat Research Unit discovered the group’s latest activity after its previous campaign involving Venezuela-related lures designed to target US government earlier in 2026.
Targeting HDFC Bank and Diplomacy Experts
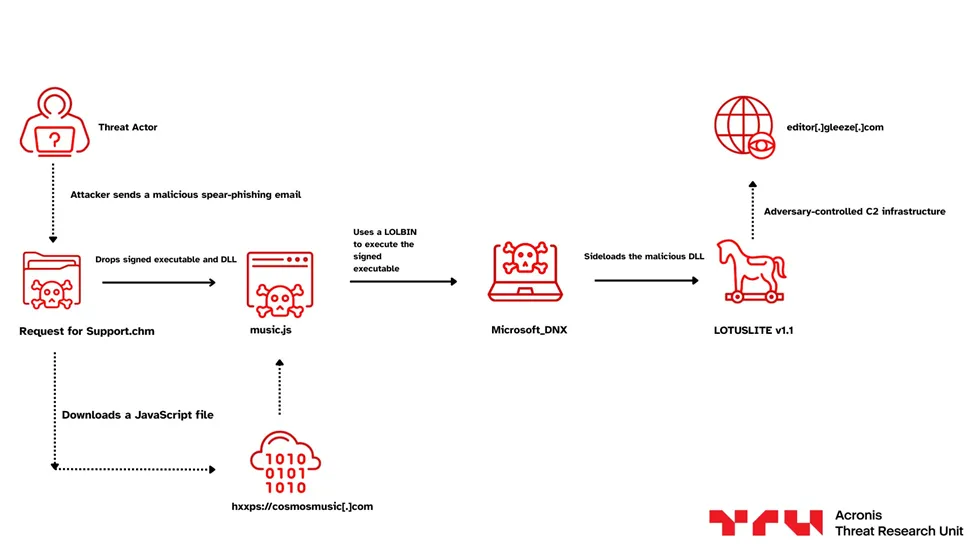
The hackers reportedly began this dual-sided campaign in March 2026. In India, they used a file named Request for Support.chm to trick workers in the banking sector. This file contained a pop-up window that mentioned HDFC Bank Limited to look official, and when a user clicked the file, it triggered a chain of events that involved downloading a malicious JavaScript file called music.js from the domain cosmosmusiccom.
Acronis’ investigation, shared with Hackread.com, revealed that the hackers didn’t stop at support tickets. They even made fake pop-up windows that looked like real HDFC Bank software. While the workers thought they were looking at a banking app, a new version of the LOTUSLITE backdoor, called LOTUSLITE v1.1, was actually spying on the system.
In another part of the campaign, the group pretended to be Victor Cha, a former Director for Asian Affairs at the US National Security Council. Using a fake Gmail account ([email protected]) with Mr Cha’s real photo, they sent out Google Drive links to folders named March 30. Inside were fake invitation letters crafted to infect the computers of policy-makers.
Same Tricks, New Names
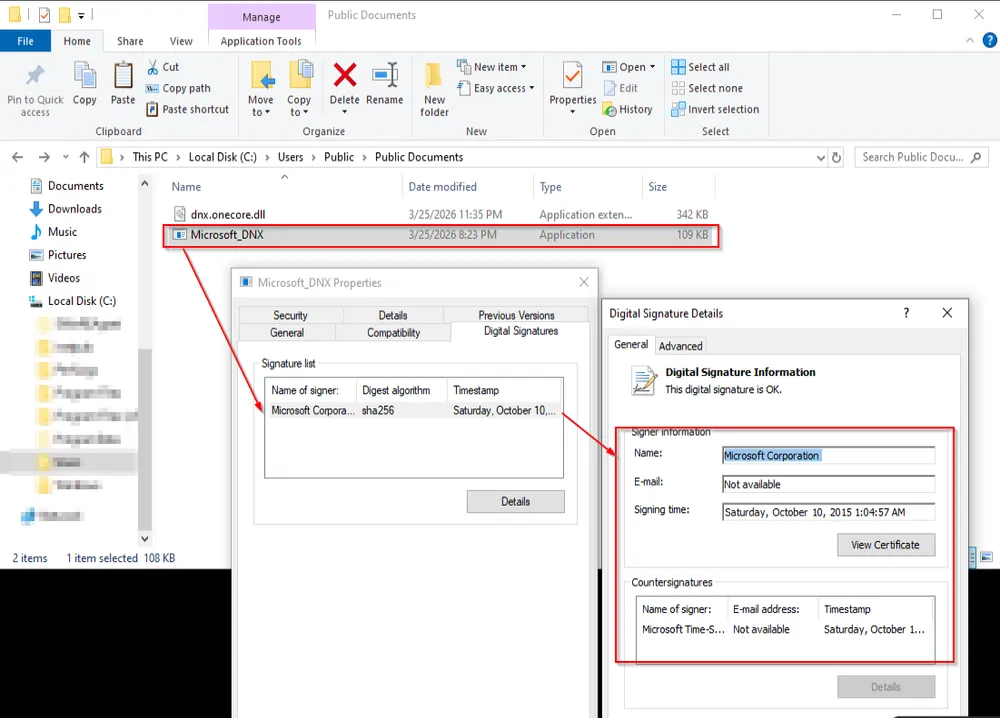
The hackers are using a method called DLL sideloading. They basically take a safe file signed by Microsoft (like Microsoft_DNX.exe) and put their own malicious file right next to it. The computer trusts the Microsoft name, so it lets that infected file run without a second thought.
According to researchers, the group is trying to hide better. They rotated the internal code marker or ‘magic value,’ a specific code used to identify their traffic, from 0x8899AABB to 0xB2EBCFDF, and also replaced a command flag named –DATA with a new one called –ZoneMAX.
Researchers also noted that the hackers used a service called Gleeze to communicate with their server at editorgleezecom. This is the same infrastructure used in previous attacks, which helped experts link the activity to Mustang Panda.
Even though the group tried to update their methods, they left behind old code names like KugouMain and DataImporterMain in the new files. They even left a message in the code mentioning a security researcher who has been tracking them.
Still, they are constantly upgrading their impersonating expertise and using trusted software to lure users, which makes it essential for everyone to stay sceptical of any unexpected emails or files, even if they look official.