We are proud to share that Flashpoint has been named a Challenger in the inaugural 2026 Gartner® Magic Quadrant for Cyber Threat Intelligence Technologies.
“We see this recognition as a testament to Flashpoint’s ability to execute at the highest levels for the world’s most discerning threat intelligence customers, with our unique combination of primary source collection and human analysis at the core,” — Josh Lefkowitz, CEO at Flashpoint.
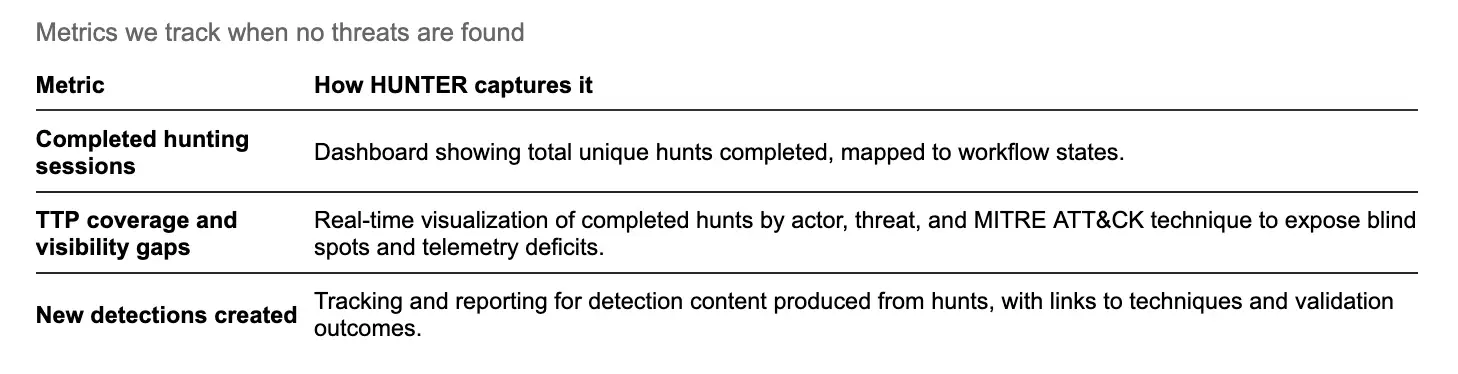
The Gartner Magic Quadrant provides organizations with a wide-angle view of vendors in the cyber threat intelligence market. By applying a graphical treatment and a uniform set of evaluation criteria, the Magic Quadrant helps organizations assess how well technology providers are executing their stated visions and performing against Gartner’s market view. Vendors are evaluated based on their Ability to Execute and Completeness of Vision:
- Ability to Execute reflects the Gartner assessment of the vendor’s product and/or service, overall viability, sales execution and pricing, market responsiveness and record, marketing execution, customer experience, as well as operations.
- Completeness of Vision comprises the Gartner view of the vendor’s overall market understanding, marketing strategy, sales strategy, offering (product) strategy, business model, vertical/industry strategy, innovation, and geographic strategy.
“We believe, and our customers consistently validate, that the future of threat intelligence lies at the critical intersection of intelligence depth and application,” says Lefkowitz. “That’s why Flashpoint pairs unmatched access to primary-source environments with the ability to operationalize that intelligence across security workflows, enabling organizations to make faster, more informed decisions.”
A complimentary copy of the Gartner® Magic Quadrant for Cyber Threat Intelligence Technologies is available to download here.
Market Dynamics and Growth of the Threat Intelligence Market
The threat intelligence market has expanded in both scope and strategic importance as organizations contend with a broader and more complex threat environment. What was once a supporting function within security operations is now expected to inform decisions across vulnerability management, fraud prevention, and enterprise risk. This shift has raised the bar for how intelligence is collected, analyzed, and applied.
Gartner describes this evolution as a move toward unified cyber risk intelligence (UCRI) — an approach that brings together diverse internal and external data sources with advanced analytical capabilities to improve decision-making. As noted in The Evolution of Threat Intelligence Is Unified Cyber Risk Intelligence, “the future of threat intelligence is unified cyber risk intelligence (UCRI)… defined by the convergence of multisignal collection and advanced analytical capabilities.” In our opinion, this model reflects the reality that no single source provides sufficient visibility, and that intelligence must be corroborated across environments to be actionable.
At the same time, the scale of available data continues to increase, introducing new challenges around prioritization and context. Gartner notes that organizations “receive vast amounts of threat data, and filtering out false positives, redundant information and irrelevant alerts to extract actionable intelligence remains a significant challenge. This “noise” can overwhelm security teams and lead to important threats being missed.” This is where AI plays a growing role. Techniques such as machine learning and natural language processing are increasingly used to correlate signals, identify patterns, and surface relevant risks faster. As intelligence becomes more integrated across the enterprise, the ability to combine multisource collection with AI-driven analysis is shaping how organizations evaluate platforms and build modern threat intelligence programs.
How Security Teams Are Evaluating Threat Intelligence
From Flashpoint’s experience working with the most discerning security and intelligence teams, the value of a threat intelligence platform is measured in how it performs in practice — how quickly it surfaces relevant activity, how much context it provides, and how easily it supports decision-making across workflows.
We see three areas consistently shape how intelligence is evaluated, supported by a combination of human expertise and AI-driven analysis:
- Access to high-signal environments: Intelligence is most useful when it reflects activity at its source. Access to closed forums, encrypted messaging platforms, and illicit marketplaces provides the context needed to understand how threats develop and move.
- Context that supports prioritization: Vulnerability and threat data require context to be actionable. Understanding how activity is discussed and operationalized in real environments allows teams to focus on what requires attention.
- Integration into operational workflows: Intelligence must fit into the systems and processes teams already rely on. Integration across SIEM, SOAR, and internal workflows allows intelligence to be applied consistently at scale.
These areas are closely tied to how Flashpoint has built its platform and how it supports organizations operating in complex threat environments.
Where Intelligence Comes From Matters
A large part of how intelligence performs in practice comes back to the source of the data itself.
We believe, and our customers continue to validate, that Flashpoint’s approach is centered on primary-source collection. That means accessing environments where threat activity is actively discussed, coordinated, and developed, including closed forums, encrypted messaging platforms, and illicit marketplaces. These environments require sustained access and ongoing validation, but they provide a level of visibility that is difficult to achieve through surface-level collection alone.
From our experience, working from these sources changes how intelligence is used. Activity can be observed earlier and understood with more context, with discussions, relationships, and intent preserved.
In practice, this allows teams to:
- Identify emerging activity before it becomes widely visible
- Maintain context across conversations, actors, and environments
- Reduce time spent investigating low-value or unverified signals
Intelligence Has to Fit Into How Teams Actually Operate
Collection alone doesn’t determine whether intelligence is useful. We believe it also has to be delivered in a way that aligns with how teams work.
In our experience, most security teams already have established workflows tied to SIEMs, SOAR platforms, and internal processes. Intelligence that integrates into those workflows can be applied consistently across investigation and response.
In practice, we see this support:
- Delivery of intelligence directly into existing systems
- Consistent application across automated and analyst-driven workflows
- Reduced friction between intelligence, investigation, and response
Over time, this consistency allows teams to build repeatable processes around intelligence rather than treating it as a separate function.
Context Drives Prioritization
The same dynamics apply to vulnerability intelligence.
From our experience, understanding which vulnerabilities exist is only one part of the problem. Determining which ones require attention in a given environment depends on context — how those vulnerabilities are being discussed, shared, or used in active threat activity.
We have seen first-hand that when vulnerability data is connected to real-world activity, teams can:
- Prioritize remediation based on active threat relevance
- Align vulnerability management with observed adversary behavior
- Reduce reliance on static scoring as the sole decision driver
Applying This in Practice
For organizations evaluating providers, challenge intelligence sources, challenge collection agility, challenge exploit prioritization and above all ask yourself is this a partner with a long-term track record of navigating the world’s most complex threat environments?
To see how Flashpoint, the world’s largest private provider of threat intelligence can help you make better decisions, faster and with confidence, schedule a demo.
Gartner Disclaimer
Gartner does not endorse any company, vendor, product or service depicted in its publications, and does not advise technology users to select only those vendors with the highest ratings or other designation. Gartner publications consist of the opinions of Gartner’s business and technology insights organization and should not be construed as statements of fact. Gartner disclaims all warranties, expressed or implied, with respect to this publication, including any warranties of merchantability or fitness for a particular purpose.
This graphic was published by Gartner, Inc. as part of a larger research document and should be evaluated in the context of the entire document. The Gartner document is available upon request from Flashpoint.
Gartner, Magic Quadrant for Cyber Threat Intelligence Technologies, Jonathan Nunez, Carlos De Sola Caraballo, Jaime Anderson, May 4, 2026.
Gartner, The Evolution of Threat Intelligence Is Unified Cyber Risk Intelligence, By Jonathan Nunez, 15 September 2025.
Gartner and Magic Quadrant are trademarks of Gartner, Inc., and/or its affiliates.