- Quick Reference: March 2026 Vulnerability Table
- Key Trends: March 2026
- Exploitation Analysis
- Interlock Ransomware Group Exploits Cisco FMC Zero-Day (CVE-2026-20131)
- Critical Deserialization of Untrusted Data Vulnerability Affecting Cisco Secure FMC Software and Cisco SCC Firewall Management (CVE-2026-20131)
- Take Action
In March 2026, Insikt Group® identified 31 high-impact vulnerabilities that should be prioritized for remediation, 29 of which had a Very Critical Recorded Future Risk Score.
These vulnerabilities affected products from the following vendors: Cisco, Microsoft, Google, ConnectWise, Langflow, Citrix, Aquasecurity, Nginx UI, Qualcomm, F5, Craft CMS, Laravel, Apple, Synacor, Wing FTP Server, n8n, Omnissa, SolarWinds, Ivanti, Hikvision, Rockwell, and Broadcom. This month’s most affected vendors were Microsoft and Apple, together accounting for approximately 32% of the 31 vulnerabilities.
One vulnerability (CVE-2017-7921 affecting Hikvision) is approximately nine years old, reinforcing how attackers continue to exploit long-known weaknesses in environments where patching has lagged. Legacy and unpatched systems remain attractive targets. Defenders should not discount older CVEs; instead, they should prioritize based on observed activity, maintain strong asset visibility, and apply compensating controls where remediation is not possible.
In March, Insikt Group® created Nuclei templates for a high-severity path traversal vulnerability in MindsDB (CVE-2026-27483) and a critical missing authentication vulnerability in Nginx UI (CVE-2026-27944). Additionally, Insikt Group® had already published a Nuclei template for CVE-2025-68613 (n8n) in December, prior to its exploitation this month. We also identified public proof-of-concept (PoC) exploits for 10 of the 31 vulnerabilities.
Quick Reference: March 2026 Vulnerability Table
All 31 vulnerabilities below were actively exploited in March 2026. The table below also provides examples of public PoCs identified by Insikt Group®. These PoCs were not tested for accuracy or efficacy. Vulnerability management teams should exercise caution and verify the validity of PoCs before testing.
#
Vulnerability
Risk
Score
Affected Vendor/Product
Vulnerability Type/Component
Public PoC
1
99
Cisco Secure Firewall Management Center (FMC)
CWE-502 (Deserialization of Untrusted Data)
2
99
Microsoft SQL Server (2016 SP3, 2017, 2019, 2022, 2025)
CWE-284 (Improper Access Control)
No
3
99
Microsoft .NET (9.0, 10.0) and Microsoft.Bcl.Memory
CWE-125 (Out-of-bounds Read)
No
4
99
Google Skia
CWE-787 (Out-of-bounds Write)
No
5
99
Google Chromium V8
CWE-119 (Improper Restriction of Operations within the Bounds of a Memory Buffer)
No
6
99
ConnectWise ScreenConnect
CWE-347 (Improper Verification of Cryptographic Signature)
No
7
99
Langflow
CWE-94 (Code Injection), CWE-95 (Eval Injection), CWE-306 (Missing Authentication for Critical Function)
8
99
Citrix NetScaler
CWE-125 (Out-of-bounds Read)
9
99
Aquasecurity Trivy
CWE-506 (Embedded Malicious Code)
10
94
Microsoft Windows
CWE-59 (Link Following)
No
11
94
Nginx UI
CWE-306 (Missing Authentication for Critical Function)
No
12
89
Qualcomm (Multiple Chipsets)
CWE-190 (Integer Overflow or Wraparound)
No
13
99
F5 BIG-IP
CWE-121 (Stack-based Buffer Overflow)
No
Table 1: List of vulnerabilities that were actively exploited in March based on Recorded Future data.
Key Trends: March 2026
- Most commonly observed weaknesses: CWE-502 (Deserialization of Untrusted Data) and CWE-94 (Code Injection).
- Two vulnerabilities and one exploit kit (consisting of 23 exploits, 12 of which are currently associated with specific CVEs) were linked to malware campaigns.
- Interlock Ransomware Group exploited a zero-day in Cisco Secure Firewall Management Center to compromise enterprise networks, deploy custom remote access trojans (RATs), and facilitate ransomware operations.
- Separately, the DarkSword iOS full-chain exploit enabled Safari-based remote code execution (RCE), sandbox escape, and kernel-level access, leading to deployment of the GHOSTKNIFE, GHOSTSABER, and GHOSTBLADE payloads.
- The Coruna exploit kit similarly compromised iOS devices to deliver the PlasmaLoader (PLASMAGRID) malware.
- 9 of the 31 vulnerabilities (CVE-2026-3910, CVE-2026-33017, CVE-2025-32432, CVE-2025-54068, CVE-2026-20963, CVE-2025-68613, CVE-2025-26399, CVE-2021-30952, and CVE-2023-41974) allowed attackers to conduct RCE.
- These 9 vulnerabilities affected Google, Langflow, Craft CMS, Laravel, Microsoft, n8n, SolarWinds, and Apple.
Exploitation Analysis
This section analyzes two of the highest-impact, actively exploited vulnerabilities this month. Where applicable, it also highlights the availability of Nuclei templates created by Insikt Group®. The full list of reports and detection rules from March is available to customers in the Recorded Future Intelligence Operations Platform.
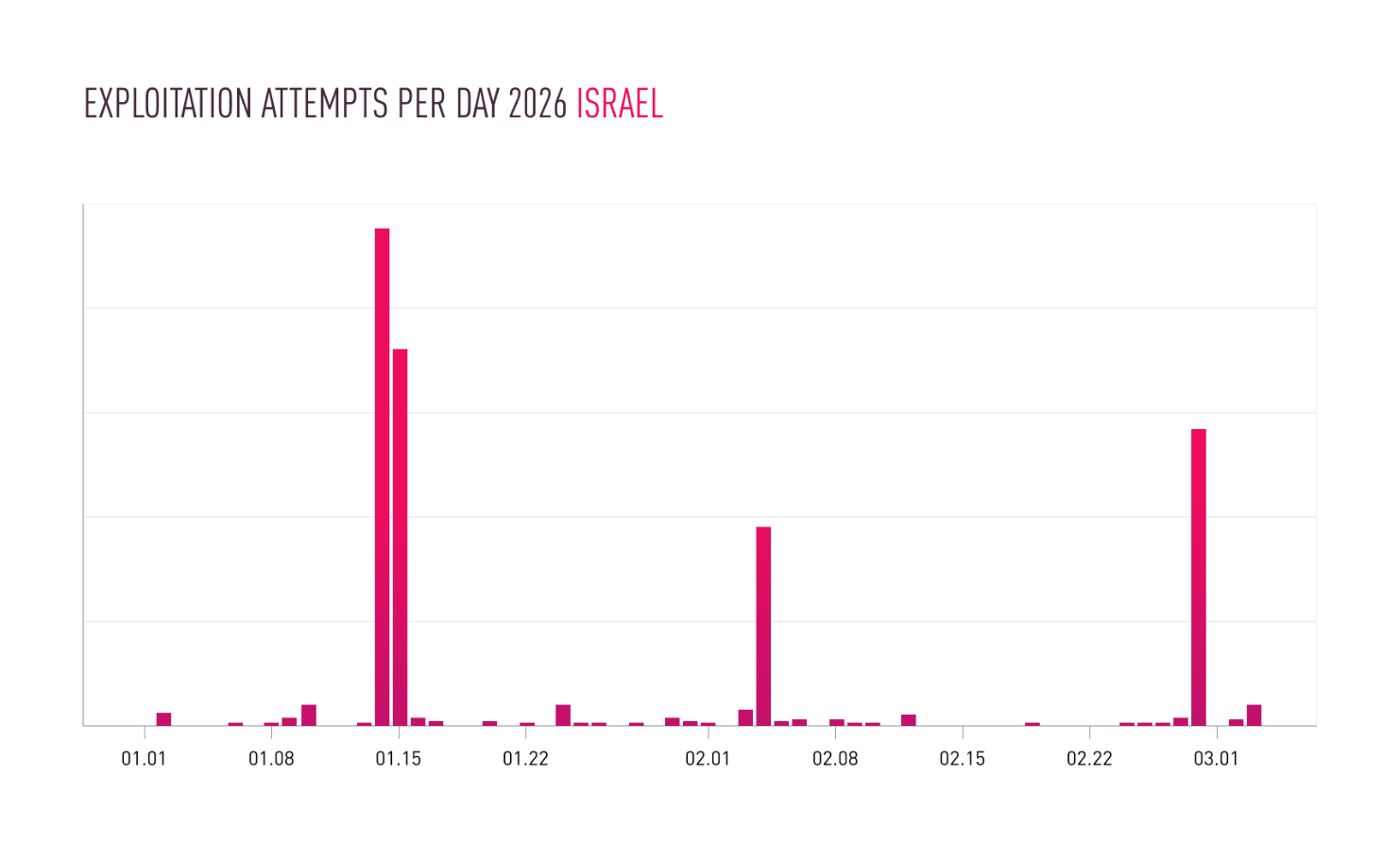
Interlock Ransomware Group Exploits Cisco FMC Zero-Day (CVE-2026-20131)
On March 18, 2026, Amazon Threat Intelligence published an analysis detailing an ongoing Interlock ransomware campaign exploiting CVE-2026-20131. CVE-2026-20131 is a critical vulnerability affecting Cisco’s Secure Firewall Management Center (FMC) software that allows unauthenticated threat actors to execute arbitrary Java code as root on vulnerable devices. Cisco Secure FMC is a centralized management platform that allows administrators to configure, monitor, and control Cisco firewall devices and network security policies across an enterprise environment. According to Amazon Threat Intelligence, Interlock Ransomware Group exploited CVE-2026-20131 as a zero-day vulnerability beginning January 26, 2026, indicating active exploitation prior to its public disclosure and enabling early compromise of enterprise networks.
The Interlock Ransomware Group exploits vulnerable Cisco FMC instances via crafted HTTP requests exploiting CVE-2026-20131 to execute arbitrary Java code as root. After gaining access, the threat actors deploy a malicious ELF binary from a staging server at 37[.]27[.]244[.]222 (Intelligence Card) to support follow-on operations.
They then use custom Java- and JavaScript-based RATs, a memory-resident web shell, and proxy infrastructure to maintain access, enable lateral movement, and evade detection. Post-compromise activity includes reconnaissance, data collection and staging, and the use of legitimate tools such as ConnectWise ScreenConnect, Volatility, and Certify for remote access, credential theft, and privilege escalation.
Insikt Group® obtained a screen locker sample (SHA256: 6c8efbcef3af80a574cb2aa2224c145bb2e37c2f3d3f091571708288ceb22d5f) shared by Amazon Threat Intelligence from Recorded Future Malware Intelligence. Sandbox analysis detected the sample as benign. Based on sandbox and static code analysis, the sample performs the following actions on a victim’s machine:
- Changes the machine’s desktop wallpaper that displays a pornographic image
- Delays execution using the Sleep API function for evasion
- Detects debuggers using the GetTickCount API function to compare timing

Figure 1: Risk Rules History from Hash Intelligence Card® for 6c8efbcef3af80a574cb2aa2224c145bb2e37c2f3d3f091571708288ceb22d5f in Recorded Future (Source: Recorded Future)
Recorded Future customers can find additional exploitation details and MITRE ATT&CK techniques associated with the exploitation of Cisco FMC Zero-Day (CVE-2026-20131) in the Diamond Models section of this TTP Instance.
Critical Deserialization of Untrusted Data Vulnerability Affecting Cisco Secure FMC Software and Cisco SCC Firewall Management (CVE-2026-20131)
On March 11, 2026, GitHub user Sadaf Athar Khan (sak110 on GitHub) shared an alleged proof-of-concept PoC exploit for CVE-2026-20131. CVE-2026-20131 is a critical Deserialization of Untrusted Data vulnerability affecting Cisco Secure Firewall Management Center (FMC) Software and Cisco Security Cloud Control (SCC) Firewall Management. Cisco Secure FMC Software is a web-based platform for centrally managing firewall policies, events, and device administration. Cisco SCC Firewall Management is a Software-as-a-Service-based (SaaS) solution for centralized configuration, monitoring, and maintenance across firewall deployments.
Exploitation of CVE-2026-20131 allows an unauthenticated remote threat actor to execute arbitrary code and gain root privileges on the affected devices. On March 4, 2026, Cisco published a security advisory and released software updates to fix CVE-2026-20131. The vulnerability resides in the web-based management interface of FMC, where insecure deserialization of a user-supplied Java byte stream allows threat actors to pass serialized objects into Java object handling without sufficient validation. As a result, an unauthenticated remote threat actor can send a crafted serialized Java object to the management interface, trigger arbitrary code execution, and escalate privileges to root.

Based on Sadaf Athar Khan’s repository, the PoC requires a target URL and a command. Once provided, the PoC generates a malicious Java-serialized object using ysoserial, embedding the supplied command within the payload and preparing it for delivery to the specified target.
The PoC then attempts to submit the serialized object to a set of candidate endpoints included in the PoC that accept serialized Java data. A reachable deserialization path allows the application to process the object and run the embedded command on the target host. After delivery, the PoC checks the server’s HTTP response codes and treats an HTTP 500 response as an indication that deserialization triggered command execution. The PoC flags HTTP 200 for manual verification because exploitation could succeed without returning visible output.
Insikt Group® has not tested this PoC for accuracy or efficacy. Recorded Future customers can find MITRE ATT&CK techniques associated with the alleged PoC in the Entities section of this TTP Instance.
Take Action
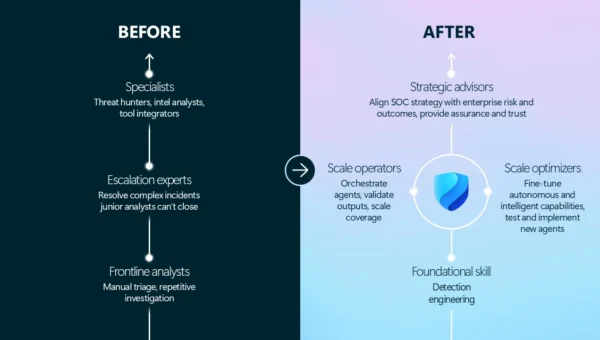
Timely and relevant information on vulnerabilities in your environment and that of your vendors and suppliers is critical for reducing risk. Find out how Recorded Future can support your team by increasing visibility, improving efficiency, and enabling confident decisions.
Vulnerability Intelligence – Prioritize vulnerabilities based on the likelihood of exploitation – not just the severity. Easily understand the risk of exploitation alongside severity, and real-time contextualized intelligence to help you quickly make confident decisions, patch what matters, and prevent attacks.
Attack Surface Intelligence – Identify internet-facing assets vulnerable to a specific CVE. Attack Surface Intelligence provides an outside-in view of your organization to help you actively discover, prioritize, and respond to unknown, vulnerable, or misconfigured assets.
Third-Party Intelligence – Gain an external view of the security posture of your vendors and partners. Eliminate time-consuming research and vendor communication cycles with the ability to promptly assess vulnerabilities in their internet-facing systems.
Insikt Group® – Receive access to exclusive reports on new vulnerabilities and trends from Recorded Future’s team of experts, the Insikt Group®. Download Nuclei templates created by Insikt Group® for select CVEs to test potentially vulnerable instances.
Recorded Future Professional Services – Work with our Professional Services team on a Vulnerability Analysis Engagement. Designed to equip your team with advanced strategies for identifying, prioritizing, and mitigating threats effectively, this program delves into technologies and operations essential for a successful vulnerability management program. (Learn more about how our Professional Services team can help your elevate your team by watching our recent Vulnerability Prioritization Workshop)