3CX VOIP Compromised & Supply Chain Threat

Source link
Related Articles
All Mix →My Only Shot at Immortality
Like my religious friends, I too would like to live forever. The thought of there being an end to my learning–a point at which my…
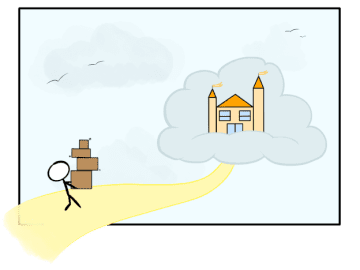
Migrating to the cloud but without screwing it up, or how to move house
Table of Contents Re-host Re-platform Re-factor A practical guide to moving to cloud services with minimal downtime, using AWS examples. For an application that’s ready…
Why do you Duplicate so much with Bug Bounties?
Why do you Duplicate so much with Bug Bounties? Source link
Press information: Detectify sees significant increase in detected vulnerabilities powered by its Crowdsource community
STOCKHOLM, January 27, 2022. Detectify, the SaaS security company powered by ethical hackers, closed 2021 with significant corporate momentum propelled by its Crowdsource community. In 2021, Detectify…
Wireless: WPA2 Enterprise Integration With Active Directory 2008 Using NPS
Table of Contents Setup 1. Install AD and Create Users 3. Configure Your Wireless Access Point 4. Configure Your Clients Fin So I finally got…
John Mick, Developer, Afonso: “Automation makes you smarter, not lazier”
Automation doesn’t lead to laziness, at least when it comes to security. Everyone (or everyone we like) wants a better, more secure web. You’re definitely…