a Hacker’s Backdoor: Service Control Manager

Source link
Related Articles
All Mix →Server-Side Template Injection Vulnerability in Confluence Data Center and Server (CVE-2023-22527)
Table of Contents Introduction Exploitation Previous Confluence Vulnerabilities Conclusion References Product Changelog Introduction On January 16 2024, Atlassian issued a significant alert on a critical…
Embracing Resilience: HackerOne’s Approach to Disaster Recovery
Table of Contents So, What Is Disaster Recovery? The Plan in Action: Ensuring Continuity Annual Drills: Beyond Compliance Targets and Performance: Striving for Excellence Continuous…
The Real Future of Tech · Joseph Thacker
Table of Contents Good Calls Big Picture of The Future Bye In 2016, my friend Daniel Miessler wrote a book called “The Real Internet of…
UXss on brave browser via scan QR Code
Brave Software disclosed a bug submitted by mrzheev: https://hackerone.com/reports/1884042 – Bounty: $500 Source link
The White House Should Prioritize Cybersecurity in its Budget
Next week, the White House will release its budget proposal for Fiscal Year 2025. With Congress still arguing about how to fund the government in…
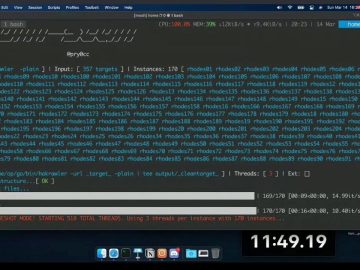
NahamCon 2021 – Introduction to Axiom – The Dynamic Infrastructure Framework for Everybody! @pry0cc
NahamCon 2021 – Introduction to Axiom – The Dynamic Infrastructure Framework for Everybody! @pry0cc Source link