Are MacBooks less likely to be hacked? #shorts

Source link
Related Articles
All Mix →Thoughts on Sam Harris’ Book on Free Will
Sam Harris’s book on free will came out today and I read it during dinner (it’s a short read). Here’s what I had to say…
Ron Paul is Seriously Flawed as a Candidate; We’re Just So in Love With Him That We’re Not Paying Attention
Table of Contents He Doesn’t Believe in the Separation of Church and State He’s Not For Federally Supported Public Education Yeah, That Means No Federal…
Smartsheet Celebrates One Year with HackerOne
As a collaboration and dynamic work management platform, Smartsheet (NYSE:SMAR) is tasked with protecting some of their customers’ most sensitive assets while also releasing new…
Hack the Box: How does linux work?
Hack the Box: How does linux work? Source link
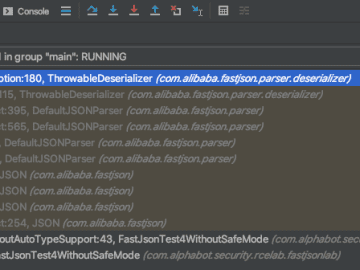
Fastjson: exceptional deserialization vulnerabilities – Alphabot Security
Table of Contents Intro Typical Fastjson RCEs (using the autoType-feature) Now it gets interesting… The global Fastjson instance How many autoType checks? But can you…
The ultimate lame jokes collection
Due to the exceptional times we’re going through – no i’m not going to try to sell you some snakeoil solution – I don’t have…