Researchers Uncover New Infrastructure Tied to FIN7 Cybercrime Group
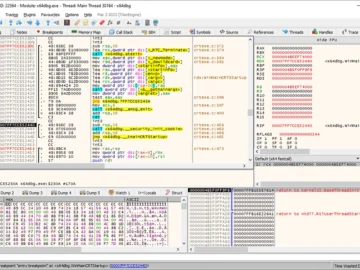
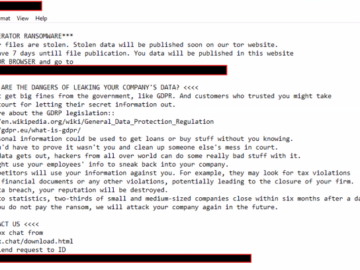
Aug 19, 2024Ravie LakshmananCybercrime / Network Security Cybersecurity researchers have discovered new infrastructure linked to a financially motivated threat actor known as FIN7. The two…