Hackers are rapidly weaponizing a little-known Microsoft authentication feature to hijack enterprise accounts, as device code phishing surges across the threat landscape.
The spike in activity is closely tied to the public release of criminal toolkits and phishing-as-a-service (PhaaS) platforms, making the once obscure technique widely accessible.
New kits are appearing almost weekly, many seemingly generated or refined using AI-assisted “vibe coding,” where attackers replicate or slightly modify existing tools to produce near-identical attack chains at scale.
Device code phishing represents a natural evolution of credential harvesting. As organizations improve defenses against password theft and MFA bypass techniques, attackers are shifting toward methods that exploit legitimate authentication workflows.
Instead of stealing credentials directly, adversaries trick users into authorizing malicious applications, granting attackers persistent access without raising immediate suspicion.
Security researchers in proofpoint warn that attackers are abusing the OAuth device authorization flow to steal Microsoft 365 access tokens, enabling stealthy account takeovers that bypass traditional phishing defenses.
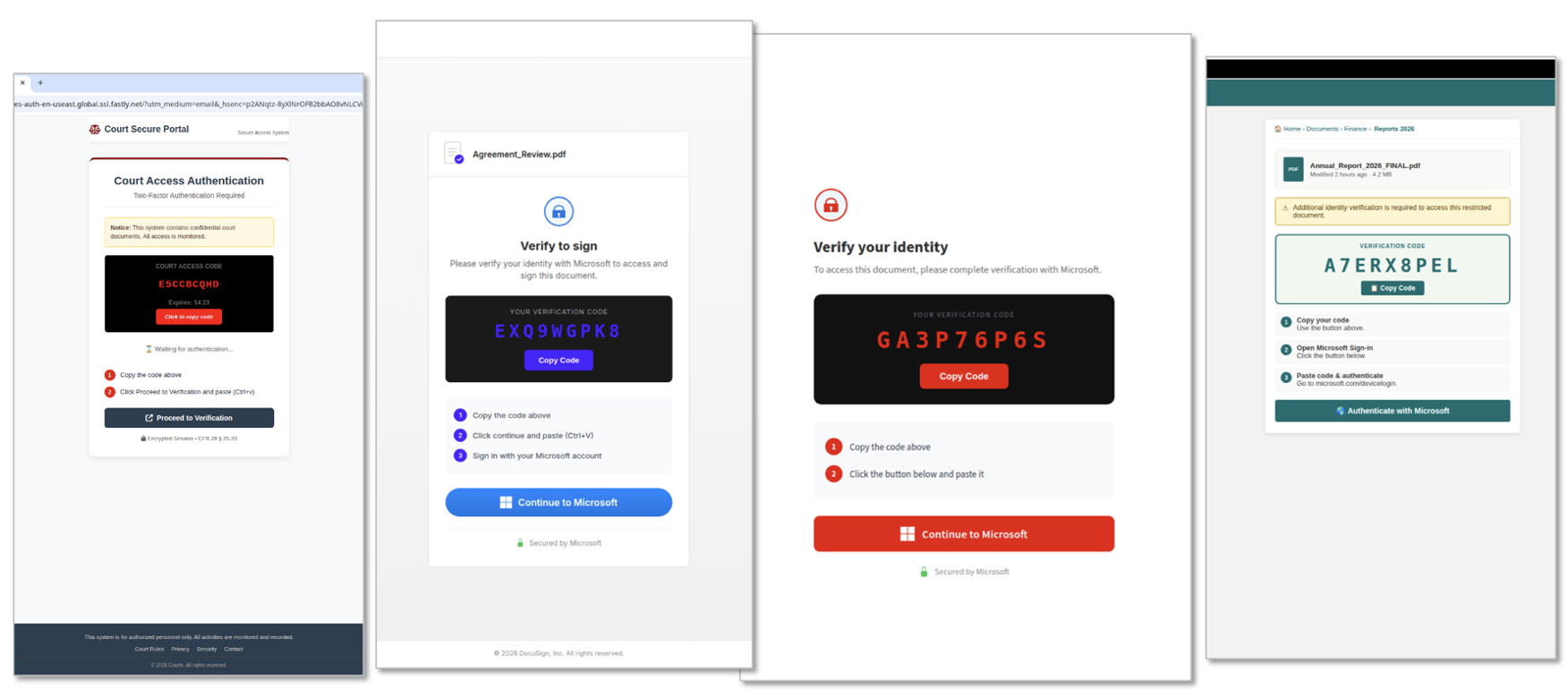
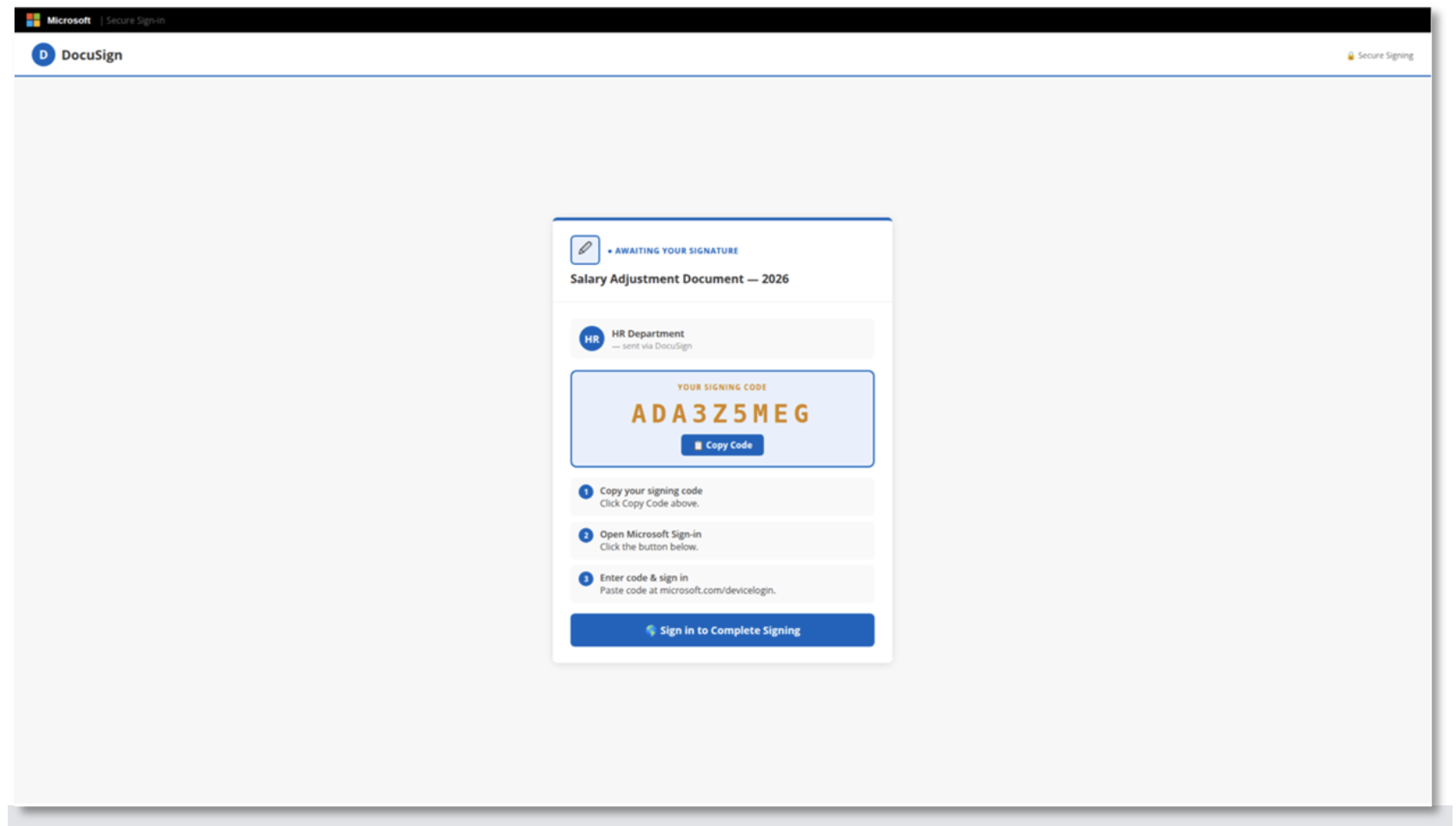
In a typical campaign, victims receive phishing emails containing links, attachments, or QR codes. These messages often impersonate trusted brands like Microsoft, DocuSign, or Adobe.
When clicked, the link initiates a legitimate Microsoft device login process. The user is presented with a unique device code and instructed to enter it at the official Microsoft device login page.
This is where the attack succeeds. By entering the code, the victim unknowingly authorizes an attacker-controlled application.
Hackers Exploit OAuth Device
Microsoft then issues authentication tokens tied to the victim’s account, which the attacker captures and uses to access email, cloud data, and other connected services.
A key innovation driving the recent surge is on-demand device code generation. Earlier versions of the attack relied on pre-generated codes that expired within 15 minutes, limiting success rates.
Modern phishing kits now generate codes dynamically when a victim clicks the link, allowing attackers to target users at any time without worrying about expiration windows.
Platforms like EvilTokens, first advertised on Telegram in early 2026, have industrialized this process. The service provides ready-made phishing templates, infrastructure, and automation tools capable of scaling business email compromise (BEC) campaigns.
Affiliates can even manage multiple compromised Microsoft 365 accounts through dedicated dashboards.
Threat actors are also combining device code phishing with “account takeover jumping,” where a compromised email account is used to spread phishing messages internally or to trusted contacts. This significantly increases the likelihood of success, as messages appear to come from legitimate sources.
One notable actor, tracked as TA4903, has shifted almost entirely to device code phishing in 2026. In recent campaigns, the group impersonated HR departments and government entities, distributing PDF attachments containing QR codes.
These codes redirected victims through cloud-hosted infrastructure to convincing phishing pages that guided them through the device authorization process.
Interestingly, some campaigns show signs of poor operational security. Researchers observed emails with blank message bodies and exposed infrastructure details, suggesting that many attackers rely heavily on automated or AI-generated tools without fully understanding them.
The trend also reflects a broader shift in the cybercrime ecosystem. Following disruptions to traditional adversary-in-the-middle (AiTM) phishing services like Tycoon 2FA, many operators have pivoted to device code phishing.
Competing platforms such as ODx and Kali365 now integrate device code capabilities, further accelerating adoption.
Despite its rapid growth, the technique relies heavily on social engineering. Much like the earlier “ClickFix” trend, victims must be convinced to copy or enter a code into a trusted platform.
In one campaign observed in April, the threat actor distributed PDFs masquerading as SharePoint documents with URLs leading to device code landing pages.
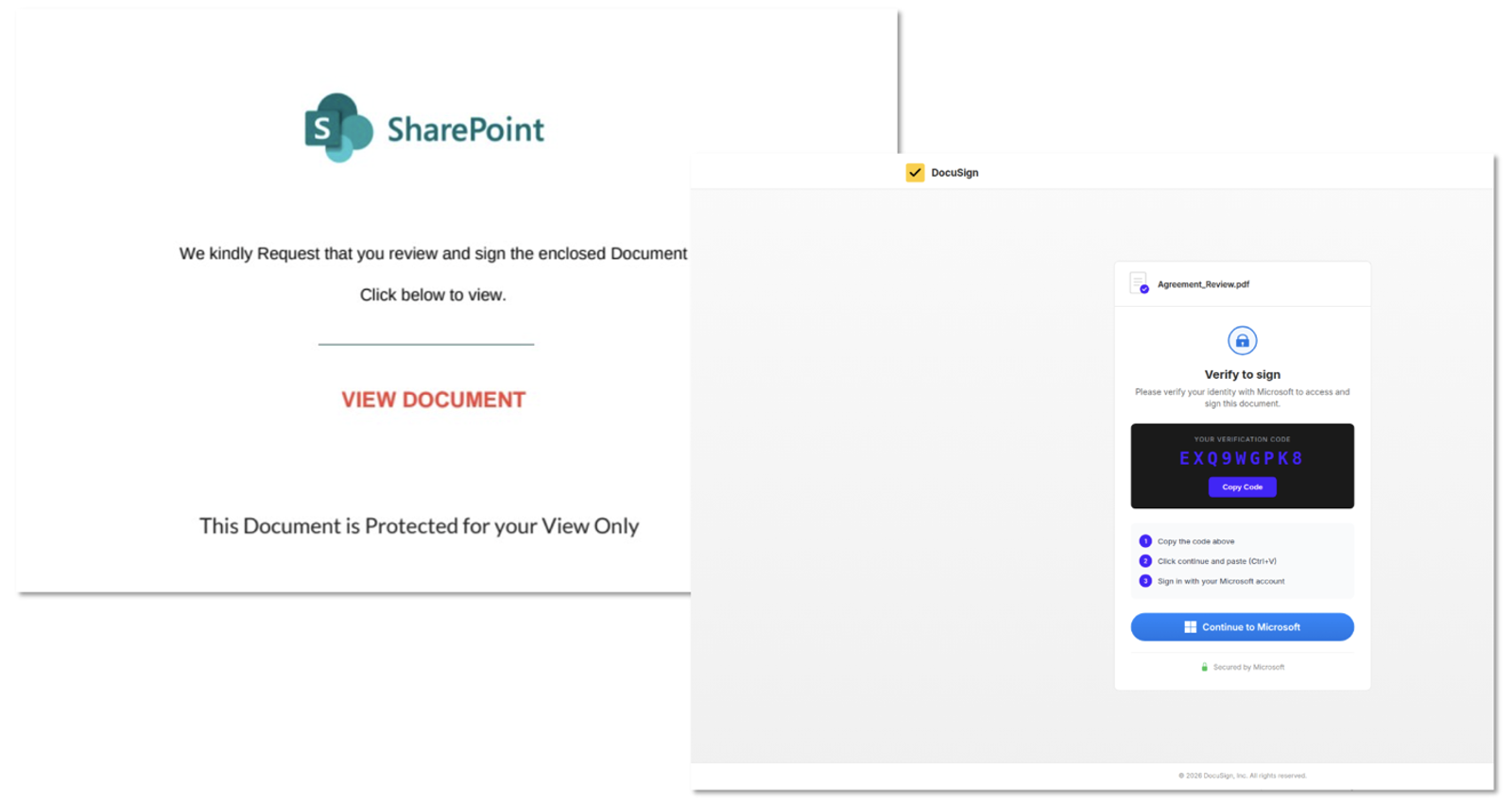
The familiarity of Microsoft’s login process makes these attacks particularly effective, as users believe they are completing a routine authentication step.
Successful attacks can result in full account takeover, data theft, financial fraud, and lateral movement within enterprise environments. In some cases, access gained through stolen tokens has been used to launch ransomware or long-term espionage operations.
Security experts emphasize that defenses remain consistent regardless of the toolkit used. Organizations can mitigate risk by restricting or blocking device code authentication flows through conditional access policies, or limiting usage to trusted devices, users, and network locations.
As attackers continue to innovate, awareness and control over authentication workflows are becoming critical to defending modern cloud environments.
Indicators of Compromise
| Indicator | Description | First Seen |
| onedrive-7tu[.]techroboticslabmade-techie-com-s-account[.]workers[.]dev | EvilTokens Device Code Phishing Landing | 26 March 2026 |
| voicemail-59f[.]admin-treyripple-com-s-account[.]workers[.]dev | EvilTokens Device Code Phishing Landing | 24 March 2026 |
| voicemail-wx7[.]mark-squires-expressrancnes-com-s-account[.]workers[.]dev | EvilTokens Device Code Phishing Landing | 24 March 2026 |
| voicemail-lyr[.]nbuckley-cambek-com-s-account[.]workers[.]dev | EvilTokens Device Code Phishing Domain | 24 March 2026 |
| f8uh-dwam-j4l5[.]pvasquez-princetonpartners-com-s-account[.]workers[.]dev | EvilTokens Device Code Phishing Landing | 1 May 2026 |
| ytgw-9n30-xlwd[.]pvasquez-princetonpartners-com-s-account[.]workers[.]dev | EvilTokens Device Code Phishing Landing | 1 May 2026 |
| z6e43e5886fe-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 019d442e-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| jo2c9ada427c6-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 7806d4cf9366-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| ee10bbf6c689-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| yaga9b286ae2c101-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| f36c2774f013-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 2dc62559e005-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 4daa2aea93db-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| ed5ce47d835f-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 6dd5fd945b34-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 0fdba029e6a5-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 019d442a-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| 019d6860-endpoint[.]com | Device Code Phishing Domain | 5 May 2026 |
| stablewebsystems[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| marktkarree-langenfeld[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| crediblebizextension[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| servicewithoutinterruption[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| marketcredibilitysignals[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| kohlhoff-edelstahlverarbeitung[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| reliablesupport[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| europetrustwave[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| trustedengagement[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| methodicalness[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| extendyourcredibility[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| europesignaltrust[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| consistentdigital[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| uninterruptedperformance[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| digitalcontinuity[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| digitalreliability[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| heilbronner-fruehlingssymposium[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| reliableinteractions[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| euromarketsignal[.]de | ODx Device Code Phishing Domain | 30 April 2026 |
| audit-report-9767d3[.]fullerjp09[.]workers.dev | TA4903 Device Code Phishing Landing | 15 April 2026 |
| hti-245401512[.]hs-sites-na2[.]com | TA4903 Device Code Phishing Landing | 5 April 2026 |
| 7740f766-8d1d-46ad-a6bc-onedrive[.]p-9jluifuu[.]workers[.]dev | ARToken Device Code Landing | 2 May 2026 |
| panel[.]hewktree[.]net | ARToken Device Code Panel | 2 May 2026 |
Note: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.







