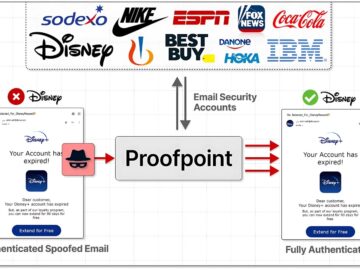
Proofpoint’s Email Protection Service Exploited to Send Millions of Phishing Emails
A massive phishing campaign dubbed “EchoSpoofing” has exploited a critical vulnerability in Proofpoint’s email protection service, allowing cybercriminals to send millions of perfectly spoofed phishing…