- The Problem with Calling QA “Non-Production”
- What Changes in Cloud
- Security Responsibility Has Shifted Left
- Where Cloud Risk Actually Begins
- Misconfiguration Is Still the Fastest Way to Fail
- Privilege Quietly Becomes Permanent
- Your Test Framework Is Also a Workload
- Prevent What You Can. Detect What You Could Not.
- The Difference Between Visibility and Insight
- Conclusion
- FAQs
Key Takeaways
- Most security failures do not begin where they are discovered. By the time risk becomes visible in production, the decisions that created it are often already sitting in test environments.
- “Temporary” test infrastructure often becomes permanent, creating persistent misconfigurations, excessive permissions, and shadow assets.
- A public Jenkins server, an over-permissioned S3 bucket, or an outdated automation container rarely looks like a security event. That is precisely why attackers prefer these places.
- Quality Engineering (QA) teams now directly influence enterprise risk through infrastructure provisioning, CI/CD pipelines, and automation frameworks.
- Mature cloud security treats QA as a strategic control point rather than an afterthought by integrating posture scanning, entitlement management, and workload protection from the outset.
The Problem with Calling QA “Non-Production”
Most security conversations begin at the wrong end of the problem.
We start with the breach, the alert, the investigation, and the inevitable question: how did it happen? Attention moves to production because that is where consequences become visible. But production is rarely where the story begins. By the time an incident reaches the SOC, the conditions that made it possible have often been quietly sitting elsewhere. Inside a test environment that no one considered particularly dangerous.
Production environments attract discipline because failure there is expensive and visible. QA environments often inherit the opposite logic: speed matters more, temporary decisions are tolerated, and security reviews are deferred because the environment is assumed to be transitional.
What Changes in Cloud
In cloud security, temporary architecture has a habit of becoming permanent. As cloud delivery accelerates, infrastructure is provisioned through CI/CD pipelines long before production, often using the same templates, permissions, and access patterns that will later be deployed downstream. The speed of this model outpaces the discipline of review, and the testing infrastructure often survives far longer than intended. That makes test environments the first place where configuration risk appears.
Example:
A Jenkins controller deployed on an Amazon Web Services EC2 instance for QA automation is assigned a public Elastic IP for easier remote access. What appears to be a simple operational choice immediately creates internet-facing exposure—opening paths for brute-force attempts, credential theft, malware insertion, crypto-mining abuse, and unauthorized access to test data. The system was built for testing, but the risk profile is production-grade.
That is usually how cloud risk enters an organization, through infrastructure created early in the delivery pipeline and treated as temporary, therefore unworthy of scrutiny. Before the breach, there is almost always a test environment.
Qualys Insights
Security Responsibility Has Shifted Left
Cloud platforms have changed the mechanics of software delivery. Developers and QA engineers do far more than simply test applications; they provision environments, manage storage, configure access, interact with cloud resources, and support release pipelines that directly shape the organization’s security posture. A QA engineer spinning up an EC2 instance is not just creating infrastructure for automation. They are defining network exposure. A deployment pipeline that applies database changes is not simply about enabling release speed. It is establishing privilege boundaries that may persist long after the release is complete.
By following security best practices during cloud resource provisioning, validating configurations, and reviewing compliance scan reports, QA teams can identify misconfigurations, configuration drift, excessive permissions, and potential vulnerabilities long before they reach production. Even without owning cloud security, maintaining visibility into posture scans across test environments helps prevent lower-environment risks from quietly becoming production incidents.
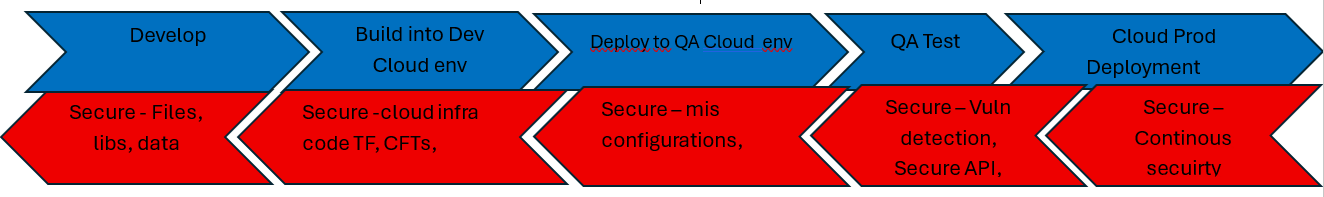
The shift is often described as “security moving left,” but that phrase can sound procedural, while the real change is structural. Security is no longer adjacent to QA. The question is not whether QA owns security, but whether cloud security can succeed if QA remains outside the model. In practice, it cannot.
Where Cloud Risk Actually Begins
The first signs of cloud risk are seldom dramatic. What becomes a security incident in production often begins as an ordinary engineering decision in QA—an access rule, a reused template, an inherited permission.
For QA teams, that exposure usually appears in four places:
| Area | Typical QA Responsibility | Security Consequence |
| Configuration | Test servers, automation infrastructure, storage | Public exposure, weak access controls, misconfigured services |
| Identity | CI/CD roles, deployment permissions, service accounts | Excessive privilege, privilege persistence, lateral movement |
| Workloads | Containers, automation frameworks, test dependencies | Vulnerable libraries, exposed secrets, runtime compromise |
| Infrastructure as Code | Terraform, CloudFormation, deployment templates | Misconfigurations repeated at scale |
None of these activities looks like “security work” in the traditional sense; rather, they look like normal engineering operations.
Misconfiguration Is Still the Fastest Way to Fail
Cloud Security Posture Management (CSPM) exists because misconfiguration remains the fastest path to exposure, as it is the easiest problem to normalize.
Example:
An S3 bucket created to store automation reports may be technically private, yet broad IAM permissions and inherited account-level access can make it functionally exposed. Missing logs, deleted reports, or altered artifacts often appear to be operational anomalies, but they are signs of over-permissioned access. In cloud environments, private infrastructure becomes vulnerable long before it becomes publicly visible.
This is the nature of cloud misconfiguration: It looks practical when it’s created. Access is broad because collaboration is easier. Permissions are inherited because release speed matters more than review. Security drift happens quietly because nothing visibly breaks.
That is why CSPM matters. CIS Benchmarks and cloud provider standards from Amazon Web Services, Microsoft, and Google create a consistent baseline for secure configuration. Without that discipline, cloud security becomes an assumption rather than a control.
Privilege Quietly Becomes Permanent
Cloud Infrastructure Entitlement Management (CIEM) addresses a simple problem: permissions granted for deployments often remain in place long after the deployment is complete.
CI/CD pipelines run with elevated access because the release depends on them. The risk begins when temporary privilege becomes permanent entitlement. Successful deployment creates a false sense of legitimacy, as though operational success proves the model is secure.
Example:
A Terraform pipeline provisioning an Azure Managed SQL Server receives elevated IAM permissions to apply schema changes and execute DDL operations. The deployment succeeds, but the same identity may also be able to modify schemas, create stored procedures or triggers, and alter security objects. What begins as deployment access quietly becomes full production database risk.
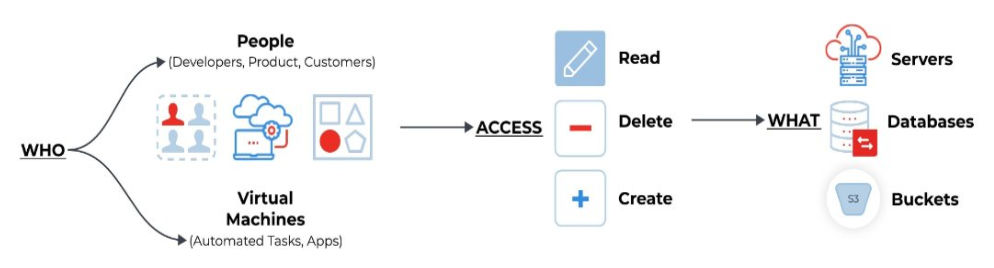
Least privilege is not a compliance exercise. It is blast-radius control. CIEM makes that visible by showing where entitlement sprawl exists and how far a single compromised credential can reach.
Your Test Framework Is Also a Workload
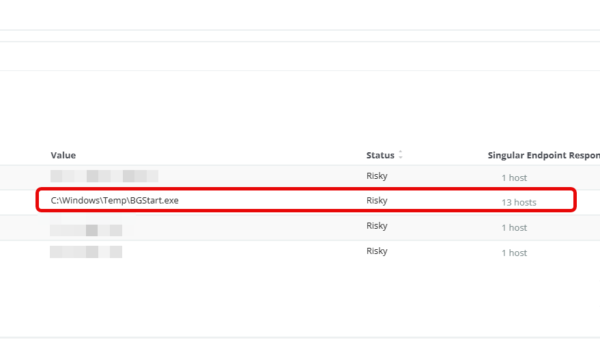
QA teams tend to think about automation through the lens of speed, stability, and coverage. Attackers look at the same systems and see an entry point.
Example:
A Java TestNG automation framework running inside Docker may execute reliably while still carrying outdated versions of Log4j or Jackson Databind, along with plaintext credentials in configuration files. Functional testing passes, but the workload remains exposed. Known vulnerabilities inside those dependencies create an entry point for lateral movement, privilege escalation, data exfiltration, or ransomware. What looks like stable test infrastructure can quietly become an enterprise attack path.
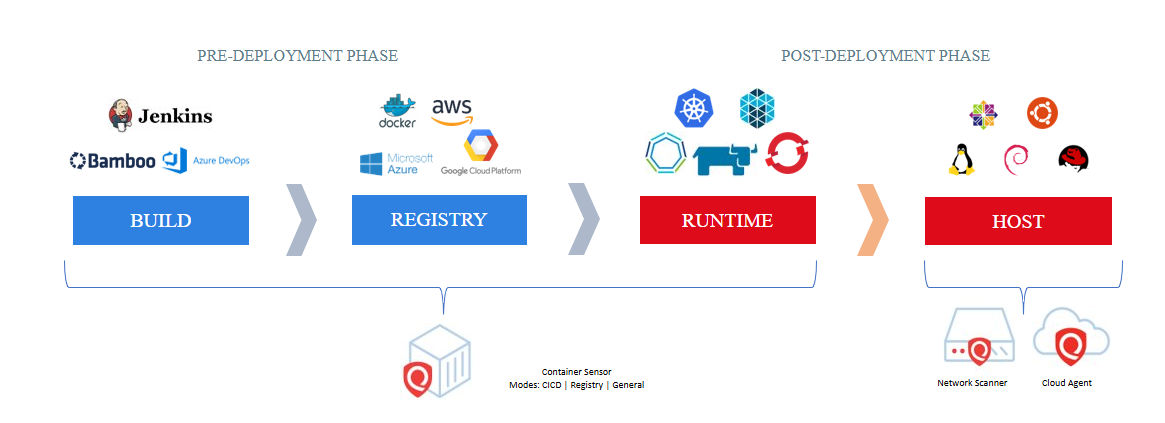
Cloud Workload Protection (CWP) focuses on the workloads themselves: virtual machines, containers, serverless functions, databases, and the software components running inside them. They are the systems engineering teams touch every day. Because these issues rarely interrupt testing, they remain invisible. CWP addresses this by continuously identifying vulnerable libraries, exposed secrets, outdated dependencies, and runtime anomalies that functional testing does not reveal.
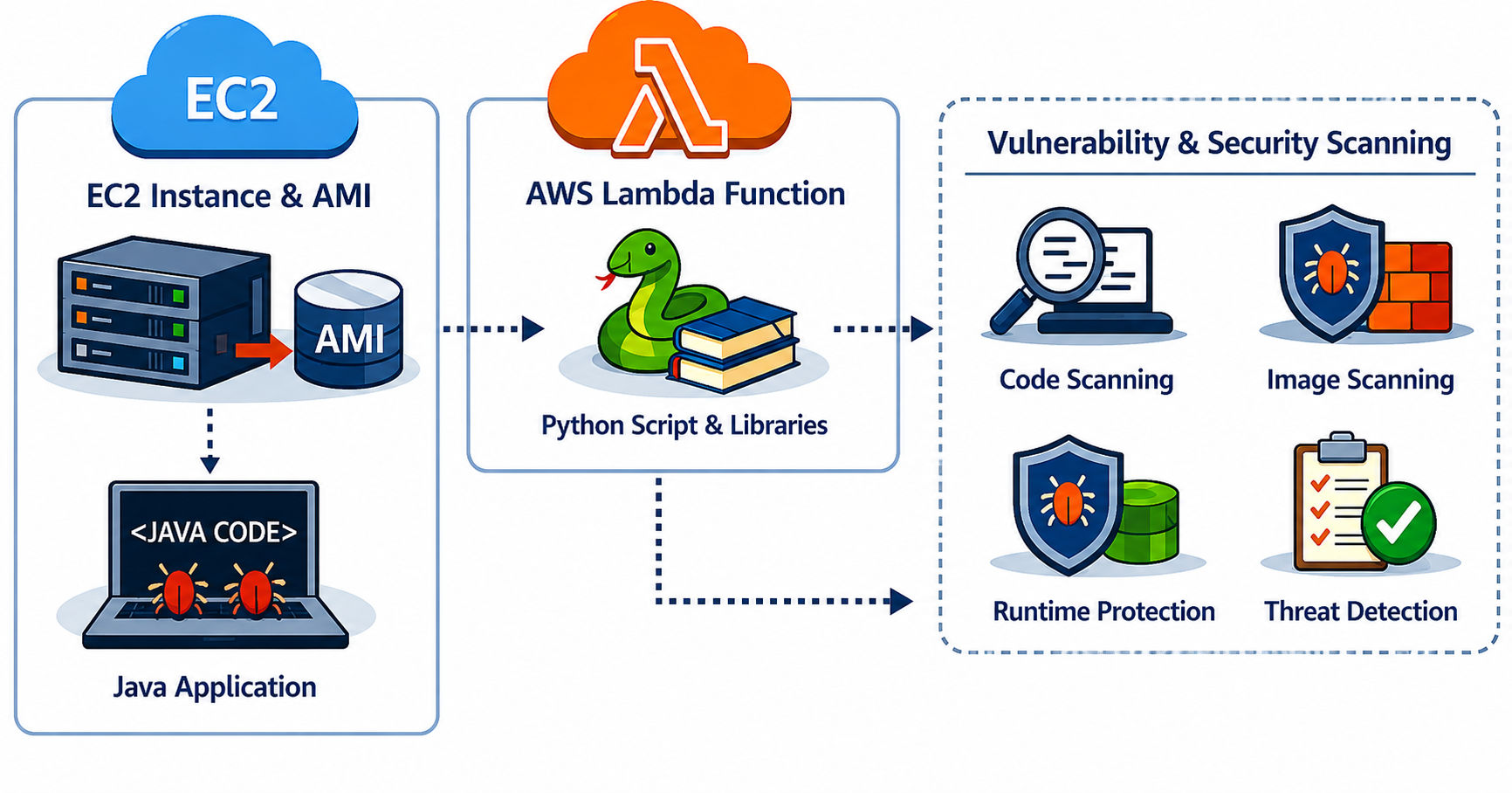
Continuous workload scanning matters because dependency chains are too deep, open-source libraries change too quickly, and secrets spread too quietly for manual review to be enough. QA teams should treat these scans as part of standard engineering practice, working with security teams to review vulnerabilities, exposed secrets, and outdated components before they become production risk.
Prevent What You Can. Detect What You Could Not.
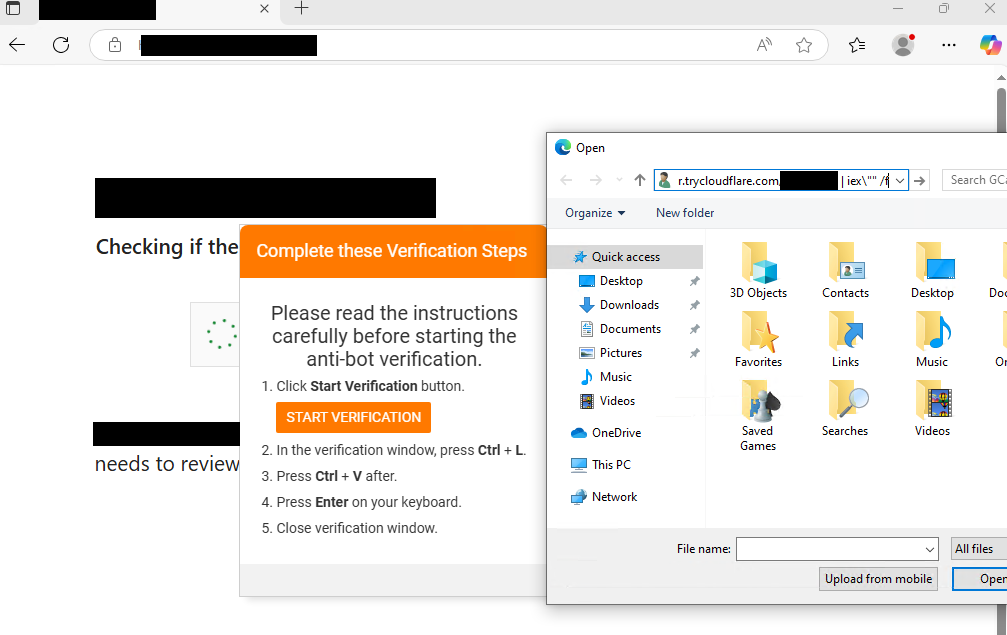
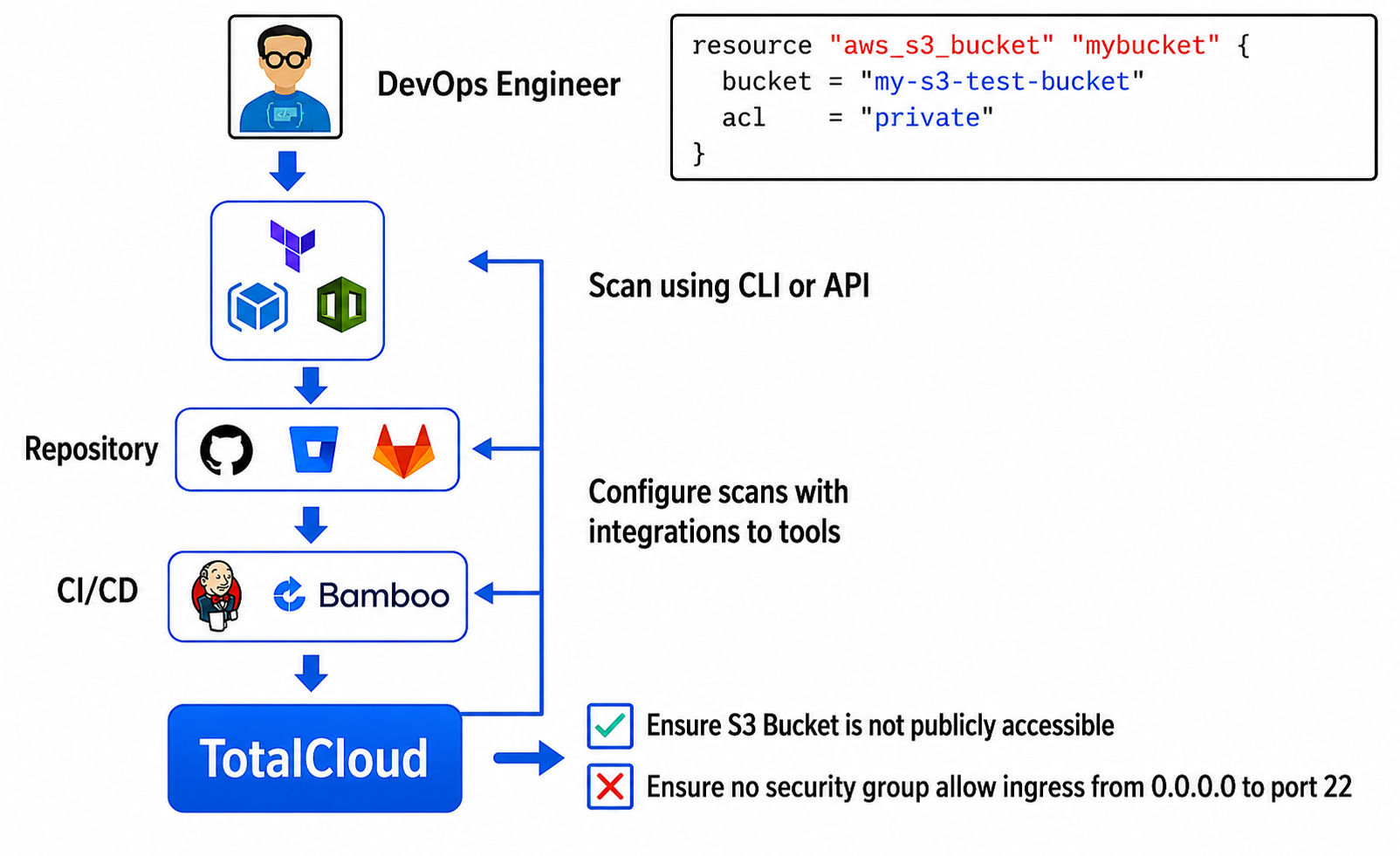
Infrastructure as Code (IaC) sped up cloud operations by making infrastructure repeatable. Templates in Terraform, CloudFormation, and ARM create consistency across environments, but they also make mistakes repeatable.
A permissive IAM role, an exposed storage configuration, or credentials that were never revoked may begin as isolated oversights. Once written into deployment templates, they become policy. Many well-known cloud incidents follow this pattern.
Examples:
- Financial Services Company: Customer PII was exposed due to misconfigured AWS servers, IAM policies, and S3 access controls that unintentionally granted attackers privileged access.
- Technology Company: Customer information was compromised when an API key embedded in an AWS server was used to access a database snapshot.
- ISP: Customer data became publicly accessible because of a misconfigured MongoDB instance.
- Transportation Company: Former employees accessed customer PII because their cloud credentials were never revoked and still allowed access to sensitive data.
IaC security is about catching weak decisions before they become standard practice.
But prevention is only half of the model.
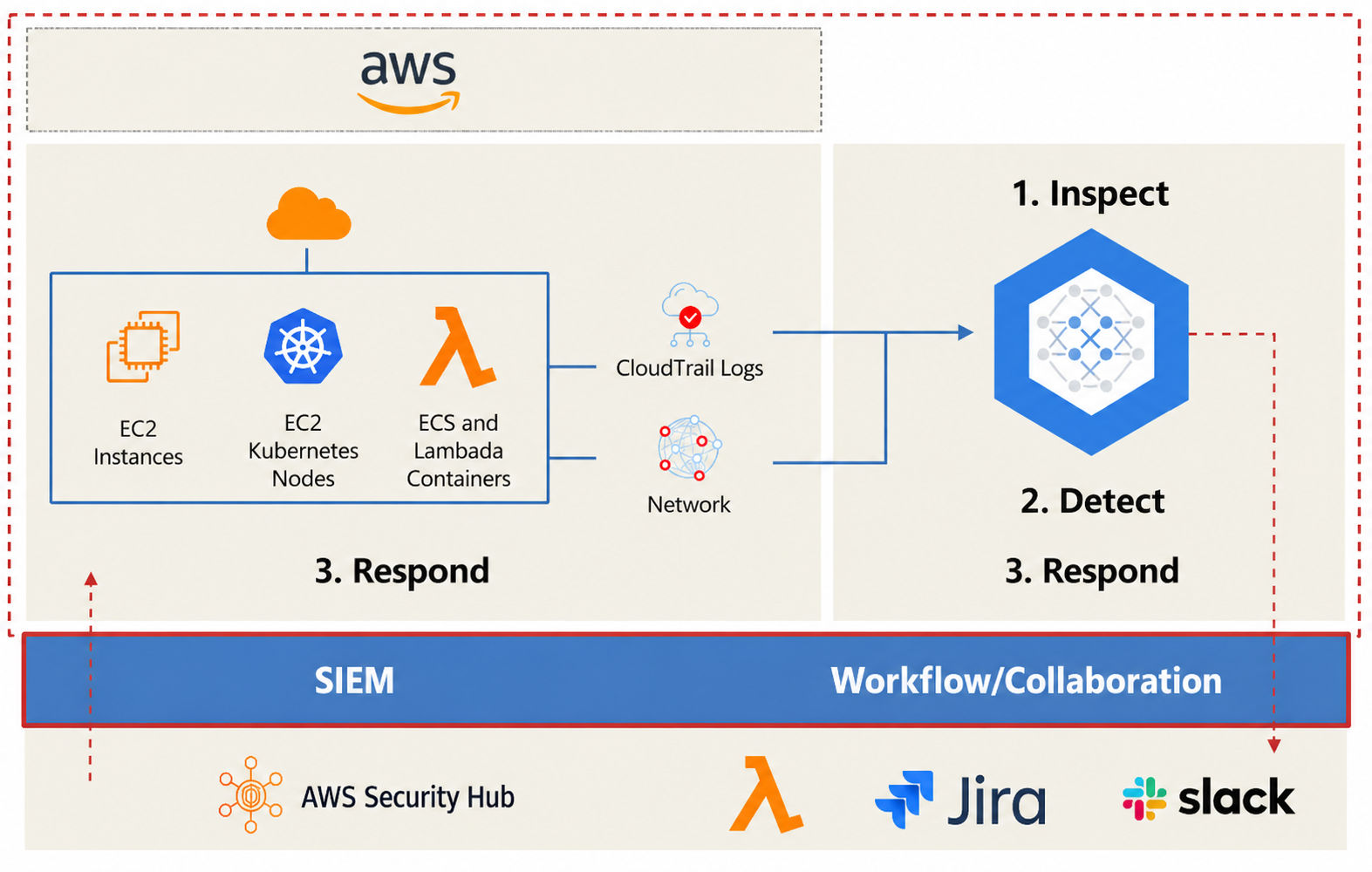
Cloud Detection and Response (CDR) then addresses what still reaches runtime by monitoring for suspicious behavior such as brute-force attempts, anomalous network traffic, malware communication, or crypto-mining activity. Modern detection platforms increasingly rely on behavioral analysis rather than static rules because the question is no longer whether an environment is vulnerable, but how quickly meaningful abnormality can be recognized.
IaC security prevents preventable risk. Detection helps contain the rest. Mature cloud security requires both.
The Difference Between Visibility and Insight
When QA is treated as separate from security, risk is shipped with confidence. A misconfigured workload, an over-permissioned identity, and an exposed container vulnerability are often reviewed as separate findings, even when they belong to the same attack path.
At the same time, the solution is not turning QA engineers into security specialists. It is making security visibility part of where QA already works: reviewing posture reports before release, questioning unnecessary permissions in deployment pipelines, treating automation dependencies as production assets, and validating infrastructure decisions before urgency turns them into permanent architecture.
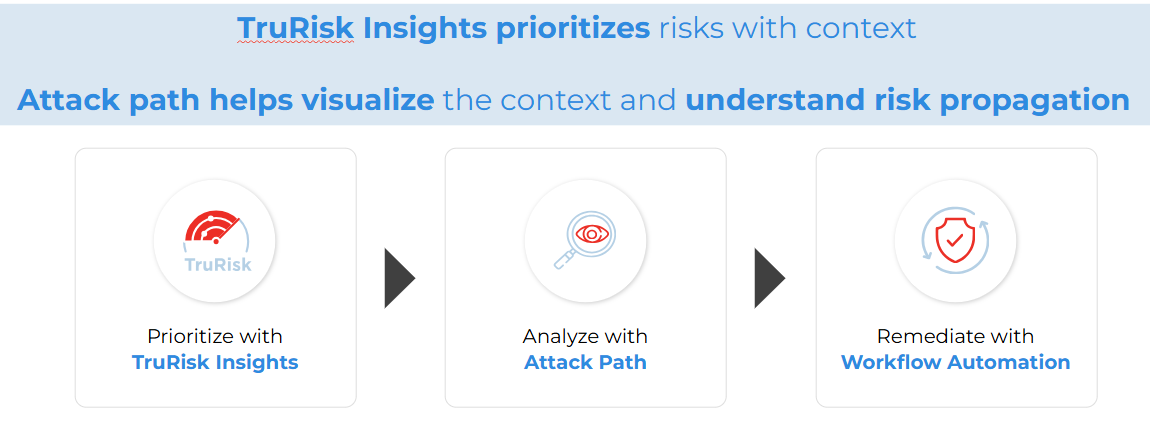
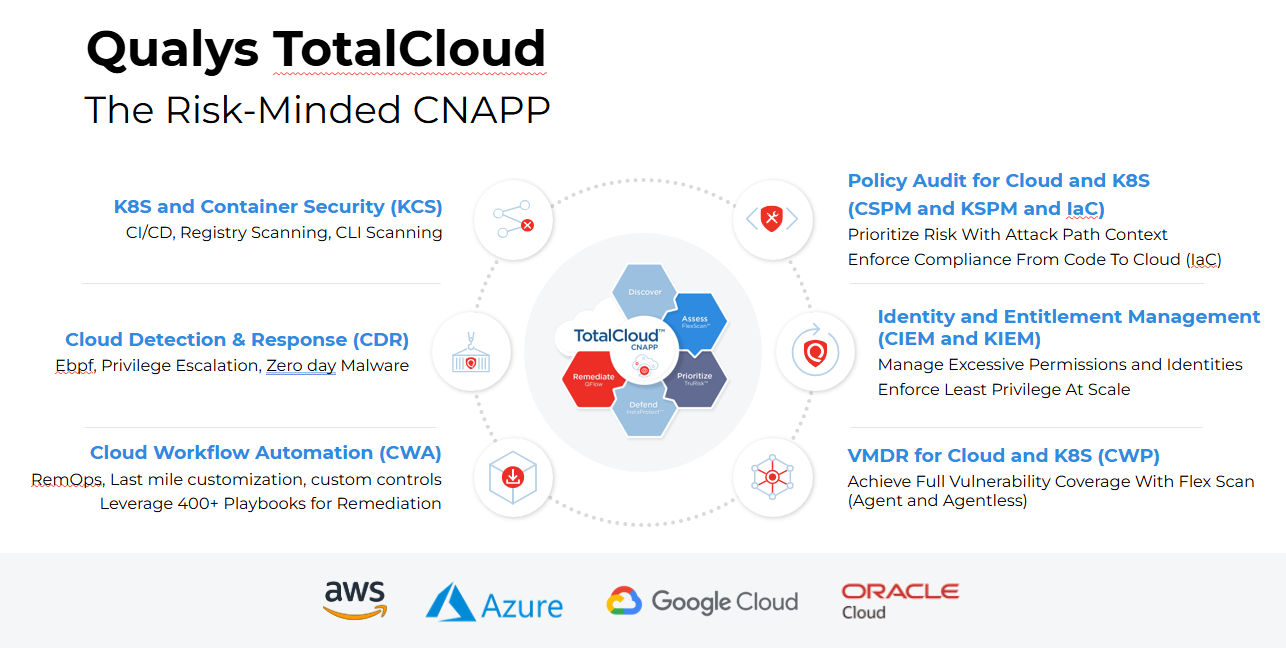
A unified CNAPP model goes beyond consolidation for its own sake, but rather helps teams see posture, entitlements, workload risk, IaC validation, and runtime behavior as parts of the same operational problem rather than isolated alerts. Qualys TotalCloud supports that model by bringing posture, identity risk, workload security, IaC validation, and runtime detection into a single view, then applying TruRisk context to prioritize what carries real business impact.
The objective is not broader visibility alone. It is better decisions, made earlier.
Conclusion
Cloud security does not begin in production because risk does not begin there.
The strongest security programs stop treating test environments as operational placeholders and start treating them as strategic control points. Because the weakest attack surface in the organization is rarely the one everyone is watching.
See how Qualys TotalCloud helps you identify, prioritize, and fix cloud risk early for better cloud resilience.
FAQs
Why are QA environments considered a cloud security risk?
QA environments often contain real infrastructure, privileged identities, automation pipelines, and cloud workloads. Because governance is lighter than production, misconfigurations and excessive permissions can persist without visibility.
What is the most common cloud security issue in test environments?
Misconfiguration remains the most common issue. Broad access permissions, insecure defaults, and unreviewed configurations create exposure long before applications reach production.
How can QA teams improve cloud security?
By integrating security checks into standard workflows: reviewing configurations, validating permissions, securing workloads, and evaluating Infrastructure as Code before deployment. Security improves when visibility exists before release, not after.
What is “shift left” security in this context?
Moving security earlier into the development and QA process so risks are caught and fixed before they reach production environments.
How does Qualys TotalCloud help secure non-production environments?
It provides unified visibility, risk-based prioritization, IaC scanning, CIEM, and workload protection across test and production — all in a single platform.