Were you affected? Retroactive Threat Detection on Verity471 helps you find out in an instant.
When a new threat surfaces, every CISO wants an answer to the question: “Were we affected?”. For security operations, answering this has often meant pulling analysts off other work to manually extract indicators, build custom queries for each detection tool, and search historical logs across platforms. This process — the final step in turning intelligence into action — delays response, extends attacker dwell time, and ties up the most experienced people on the team.
At Intel 471, we’ve been working to overcome these obstacles with Retroactive Threat Detection (RTD) on the Verity471 cyber intelligence platform. RTD eliminates the manual work of extracting indicators of compromise (IOCs) and query writing, dynamically translating IOCs from reports on Verity471 into ready-to-run detection queries tailored for all major endpoint detection and response (EDR) and Security Information and Event Management (SIEM) platforms.
Look back at logs for threats, don’t just block forward
While most teams use IOCs to detect and block future threats, RTD lets teams act swiftly against threats already inside their environment. In this way, RTD is like reviewing CCTV footage armed with information about a suspect’s appearance. Now, when a new report arrives on Verity471, analysts can quickly match IOCs from the report — such as IP addresses, domains and file hashes — to their historical telemetry to confirm whether they were impacted by a threat prior to receiving new intelligence. For threats that persist quietly for long periods, sometimes months before detection, teams now have an opportunity to disrupt attackers before they move laterally, gain persistence or exfiltrate data.
A significant value for analysts is that RTD-generated queries are delivered within Verity471 intelligence reports. This means when an analyst runs an RTD query on EDR or SIEM logs that flags a matching IP address, they will still know what threat actor, campaign, geopolitical event and other indicators it was related to — critical context that is often discarded by platforms that aggregate IOCs into blocklists. This context enables better communication between CTI, the security operations center (SOC) and incident response as findings are used to disrupt an active intrusion, confirm a past breach or understand what systems were impacted by malicious infrastructure.
RTD generated query configured for multiple tools, delivered within the Verity471 report to retain CTI context.
Powered by high-fidelity IOCs and tooling knowledge
Cyber HUMINT advantage
Ultimately, detection queries are only as good as the intelligence they’re built on. The strength of RTD lies in the speed it allows analysts to operationalize unique intelligence and data from Intel 471’s global cyber HUMINT program. Our Adversary Intelligence team leverages deeply embedded sources to bring context to IOCs derived from scraping and the unique malware samples, logs and data sets they source directly from threat actors. Analysts using Verity471 know that intelligence and IOCs in reports on the platform are validated and contextualized with deep insights into the threat actor, spanning their handles and aliases, tactics, techniques and procedures (TTPs), tooling, campaigns and targeting. RTD is also available in malware campaign reports that leverage high fidelity indicators from our patented Malware Emulation and Tracking System (METS), which provides near real-time, pre-validated command-and-control (C2) configuration information and file- and network-based indicators from over 400 malware families under surveillance.
Bringing HUNTER’s know-how to RTD
Turning indicators into performant, tool-specific detection queries brings incredible value to retroactive detection and investigations, but the process isn’t straightforward. Analysts typically need to manually extract relevant IOCs, identify the right data sources, and translate IOCs into tool-specific query syntax with correct field mappings — often a slow, error-prone process.
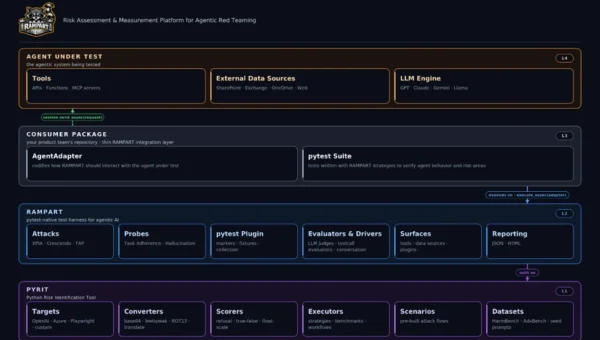
RTD overcomes these obstacles by leveraging HUNTER’s content engine to deliver native log detection queries for over 20 EDR, XDR and SIEM platforms. HUNTER also accounts for what each tool can and cannot see. A key limitation of TTP-driven hunting with Sigma-based detection rules is that it may assume the underlying telemetry exists in the target tool. But different security tools capture different data. For example, detection rules that reference telemetry sources such as process creation, DNS resolution, or image load events may return no results — not due to the absence of adversary activity, but due to gaps in the underlying data collection capability of the deployed tooling.
RTD only generates IOC-based queries where the target tool has the necessary visibility to capture that data, preventing analysts from using queries that would yield false negatives, giving them a false sense of security. On Verity471, analysts can set up their RTD query environment with the EDR and SIEM tools they use. RTD then generates detection content tailored for specific tools with the correct field mappings, ensuring that when a query can run, it’s looking in the right place.
Key benefits of RTD include:
- Analysts can move from report to a ready-to-execute query in clicks
- Detection queries based on proprietary Intel 471 CTI and malware analysis
- Queries live alongside intelligence reports with complete context (threat actor, campaign, IOC and entities)
- Tool-native, field-mapped queries tailored to the customer environment
- Multi-tool support via HUNTER environment configuration (SIEM, XDR, EDR)
The new RTD tool is available today in real-time field reports from the Adversary Intelligence team’s HUMINT collection, Finished Intelligence reports on Verity471, such as malware campaign reports, and cyber campaign reports on the Geopolitical Intelligence module.
How RTD on Verity471 helps you scale retroactive detection
1. Putting RTD in the analyst workflow
When a breach alert affecting a key third-party appears on Verity471, one of the first places analysts look at is Information Reports from our Adversary Intelligence researchers. These tactical field reports contain first-hand insights into breaches, access offers, and new cybercrime products and services our researchers gain through direct engagement. The reports contain researcher comments, a reliability assessment of the actor’s information, their TTPs, and observed IOCs and entities, such as domains, URLs, IP addresses, file hashes and different aliases the actors have used on different underground forums.
Rather than manually extracting relevant IOCs, RTD generates a tool-specific query based on IOCs and entities in the report. The RTD query is delivered within the report, ensuring that context is retained after executing the query on a SIEM, EDR or XDR platform. This in-report workflow provides analysts with the full chain of provenance and context when an RTD query results in a match in logs. The analyst may then hand off to the threat hunt team to conduct a search for behaviors associated with the threat, create or tune detection logic, or use the query to block future threats.
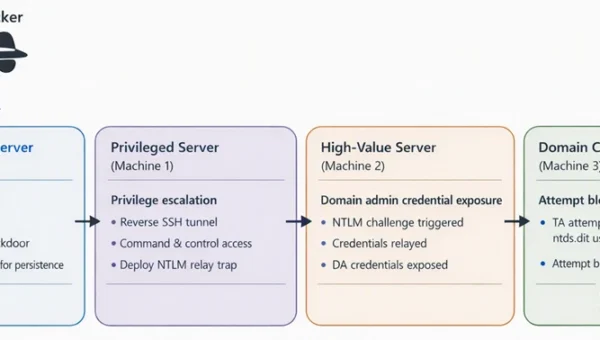
2. Using new intelligence to uncover stealthy threats
Some threats can persist silently on networks for long periods, using trusted tools to blend into normal network traffic and methods to avoid triggering alerts. When IOCs are uncovered during an investigation into the incident, RTD on cyber campaign reports in Verity471’s Geopolitical Intelligence module enables teams to quickly generate queries and confirm whether the threat is present in logs during a known active campaign window.
If a threat from a report is found in an environment, the report can be a useful pivot point into threat hunts for broader behavioral patterns not seen in IOCs. Geopolitical Intelligence reports contain links to relevant behavioral threat hunting packages from the HUNTER library. Hunt packages are tagged with threat actors, MITRE ATT&CK technique identifiers. When an analyst runs an RTD query and verifies the presence of matching IOCs in logs, they can share the RTD query and contextualized IOCs with the threat hunt team or incident response, which can use the query as an input for detection engineering and hunt prioritization.
3. Running RTD in parallel with HUNTER behavioral hunts
When a new threat report lands, CTI analysts can use RTD queries in parallel with hunt teams using HUNTER threat hunt packages. Executing IOC-based RTD queries lets you search your environment for the specific IPs, domains, and URLs associated with the campaign. The same CTI can help prioritize hunts, enabling the hunt team to select behavioral hunt packages against the same actor’s known TTPs.
The reason you need both is that IOCs are disposable. A threat actor can rotate infrastructure between campaigns with a configuration change, resulting in new IPs, domains, URLs. By the time intelligence is published, some of those indicators may already be stale and of little value to new telemetry. Behaviors are harder to change. The way an actor establishes persistence, moves laterally, or stages data tends to remain consistent even as their infrastructure changes. Behavioral hunt packages let you search for behavioral patterns independently of specific indicators.
RTD brings these CTI and hunt together in a single workflow — so while you’re blocking and tackling on the IOC side, you’re simultaneously hunting for the underlying behaviors that will remain relevant long after the indicators have rotated.
Conclusion
The gap between receiving threat intelligence and acting on it has long been one of the most costly inefficiencies in security operations. Every hour spent manually extracting IOCs, writing queries, and searching logs is an hour an attacker may be moving laterally, exfiltrating data, or establishing persistence.
Retroactive Threat Detection on Verity471 is available today to help your security teams detect, investigate and respond faster to increasingly complex threats. RTD turns your historical telemetry into an active line of defense leveraging Intel 471’s premier cyber HUMINT and underground data collection.
Looking to get started with RTD? Contact us to organize a demo today. Existing customers interested in RTD can contact their customer success rep and learn more about it on Verity471.