Broken Access Control – Lab #7 User ID controlled by request parameter | Short Version

Source link
Related Articles
All Mix →Introducing Burp Suite’s game-changing performance update | Blog
Table of Contents Hands-on security testers need the best tools for the job. Tools you have faith in, and enjoy using all day long. Burp…
IT Sec FAQ – Detectify Blog
Table of Contents Detectify’s IT Security FAQ – Click on the question you want to learn more about! IT Security FAQ 1: What should you…
Updated Hacker Invitations: Hack more, hack better
Hello hackers! We’ve rolled out some changes over the past few weeks to make it easier for you to manage the invitations you receive on…
Broken Access Control – Lab #9 UID controlled by param with data leakage in redirect | Short Version
Broken Access Control – Lab #9 UID controlled by param with data leakage in redirect | Short Version Source link
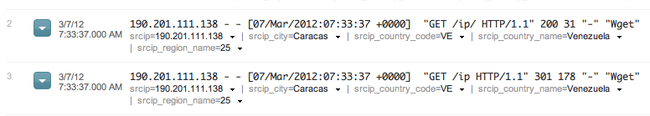
Getting Real IP Addresses Using CloudFlare, Nginx, and Varnish
March 6, 2012 CloudFlare is a great service that proxies your site’s traffic in order to offer performance gains and filtering options. It can compress…
Managing Balances
Intelligence may be seen as a mastery of a series of life’s compromises. One must be versed extensively in the extremes of all spectrums and…