Attackers are increasingly combining QR codes, fake CAPTCHA gates, and ClickFix-style tricks to steal credentials at scale, even as major phishing-as-a-service (PhaaS) platforms face disruption.
These tactics shift risk from traditional malware attachments to highly convincing, hosted phishing flows that are harder for both users and email filters to spot.
Across this volume, 78% of threats were link-based, underscoring attackers’ increasing preference for hosted infrastructure over static payloads.
Malicious attachments drove 19% of attacks in January fueled by big HTML and ZIP waves before stabilizing at 13% in February and March as link-based credential phishing took the lead.
During Q1 2026, Microsoft Threat Intelligence recorded roughly 8.3 billion email-based phishing threats, with monthly volumes easing from about 2.9 billion in January to 2.6 billion in March.
Credential harvesting remained the dominant goal behind these payloads, whether users were sent to remote phishing pages or tricked into opening locally rendered sign-in clones.
The quarter began with Tycoon2FA in a period of reduced activity. January volumes represented a 54% decline from December 2025.

This pattern, combined with the rise of infrastructure-heavy campaigns, shows actors deliberately investing in resilient phishing backends instead of one-off malware deliveries.
CAPTCHA and ClickFix as evasion
A standout trend in Q1 was the evolution of CAPTCHA-gated phishing, where fake verification pages act as both social engineering and anti-analysis shields.
Attackers force users to “prove” they are human before revealing a phishing login page, cutting the chances that automated scanners will observe the full attack chain.
After declining in both January (-45%) and February (-8%), CAPTCHA-gated phishing volumes exploded in March, more than doubling (+125%) to 11.9 million attacks, the highest volume observed over the last year.
Microsoft observed CAPTCHA-gated volumes drop in January and February, then spike 125% in March to about 11.9 million attacks, marking their highest level in the past year.
At the same time, threat actors continued to weaponize CAPTCHA-like flows in ClickFix campaigns, which instruct users to copy and run malicious PowerShell or shell commands under the guise of resolving an error or completing an extra security step.
Rather than clicking an obvious link, victims effectively execute the payload themselves often from trusted interfaces like the Run dialog making conventional “don’t click suspicious links” training less effective.
By blending CAPTCHAs, pseudo-helpdesk prompts, and command execution, attackers turn user trust and familiarity with verification prompts into reliable initial access.
QR code phishing was the fastest-growing vector in early 2026, with volumes climbing from about 7.6 million in January to 18.7 million in March a 146% quarterly increase.
Most lures used PDFs embedding QR codes that redirect users to mobile devices outside corporate controls, with smaller but growing use of DOCX attachments and QR images placed directly in email bodies.
This approach sidesteps text-based URL inspection and exploits the habit of scanning codes with unmanaged smartphones.
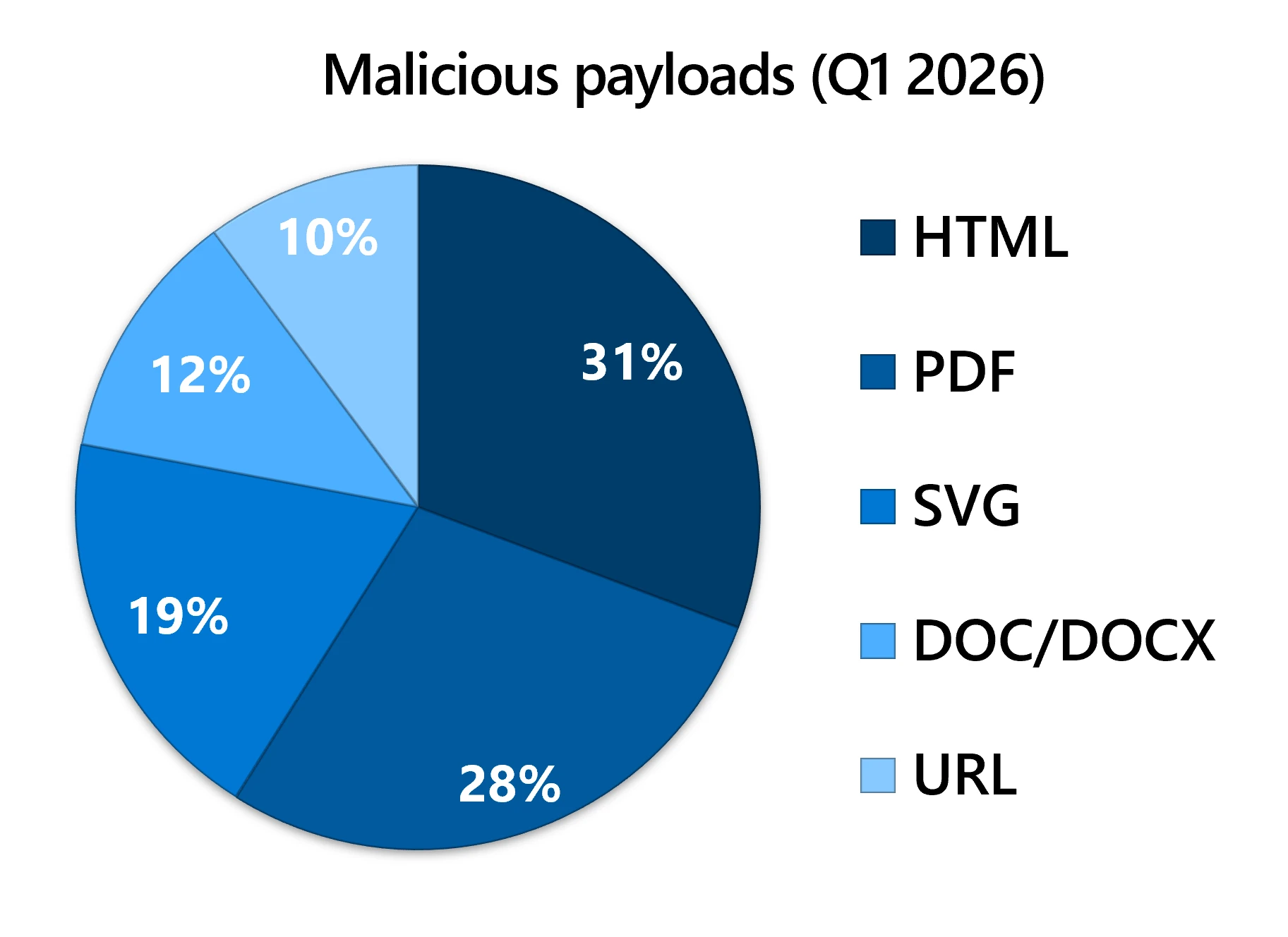
HTML, PDF, ZIP/GZIP, and SVG attachments surged or dipped week to week based on large-scale campaigns, but they consistently funneled users into credential theft flows, sometimes after multi-step staging and CAPTCHA checks.
Underlying these tactics is an active PhaaS ecosystem. Tycoon2FA, a leading AiTM platform that uses self-hosted CAPTCHAs and dynamic phishing portals, saw a 15% decline in associated email volume after a coordinated disruption led by Microsoft’s Digital Crimes Unit and Europol in early March 2026.

However, Tycoon2FA quickly retooled, shifting away from providers like Cloudflare, rotating to new TLDs and .RU-heavy registrations, and regaining partial capacity rather than collapsing completely.
Defense priorities for credential theft
Parallel offerings such as Kratos and EvilTokens are expanding, with the latter driving AI-enabled device code phishing that abuses legitimate OAuth device flows to obtain long-lived tokens for BEC and account takeover.
File-based malicious payloads were volatile by type but stable in purpose: by the end of Q1, around 94–95% of payload-based attacks were credential phishing, while traditional malware deliveries shrank to roughly 5–6%.
Given these trends, defenders should focus on layered email and identity controls rather than relying on attachment scanning alone.
Strong policies for Microsoft Defender for Office 365 Safe Links, Safe Attachments, Zero-hour auto purge (ZAP), and Threat Explorer-based hunting help detect and retroactively remove QR, CAPTCHA, and ClickFix-style campaigns.
On the identity side, password-less and phishing-resistant MFA, conditional access for privileged accounts, and network protection in Defender for Endpoint reduce the impact of stolen credentials and session tokens.
Equally important is targeted user training that explicitly covers QR-based lures, CAPTCHA-gated logins, and scenarios where users are asked to paste commands or device codes as part of “verification.”
Reinforcing the message that security checks should never require copying opaque commands or codes from untrusted prompts can blunt both CAPTCHA abuse and ClickFix-style techniques.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.







