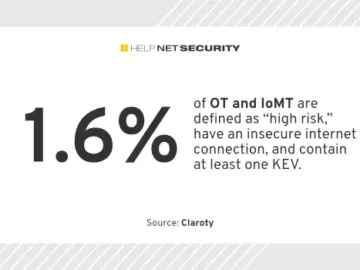
Cybersecurity analysis exposes high-risk assets in power and healthcare sectors
Traditional approaches to vulnerability management result in a narrow focus of the enterprise attack surface area that overlooks a considerable amount of risk, according to…