Malicious Go Module Poses as SSH Brute-Force Tool, Steals Credentials via Telegram Bot
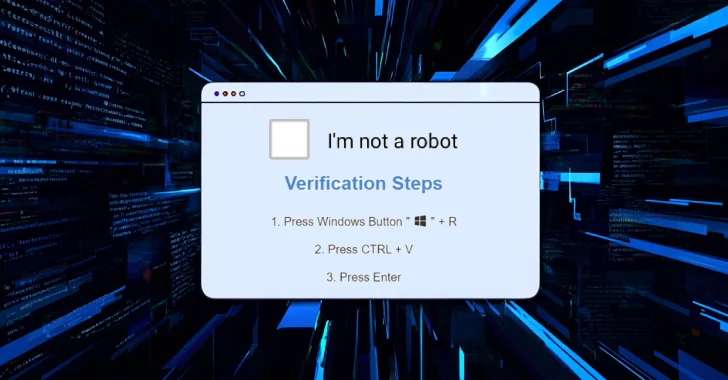
Aug 24, 2025Ravie LakshmananMalware / Supply Chain Security Cybersecurity researchers have discovered a malicious Go module that presents itself as a brute-force tool for SSH…