Hackers Hit Indian Defense, Energy Sectors with Malware Posing as Air Force Invite
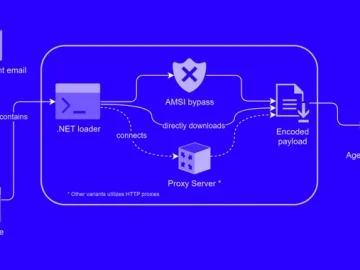
Mar 27, 2024NewsroomCyber Espionage / Data Breach Indian government entities and energy companies have been targeted by unknown threat actors with an aim to deliver…