Introducing Cyber Threat Exposure Bundle: A Unified Approach to External Risk
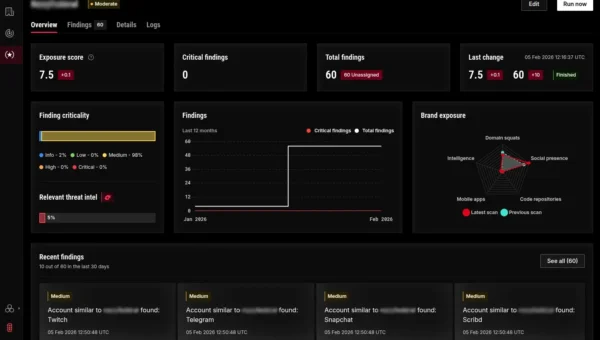
The expanding attack surface Organizations today defend an ever-expanding attack surface. The rapid integration of technology, including software as a service (SaaS) and customer-facing digital…