When configuration becomes a vulnerability: Exploitable misconfigurations in AI apps
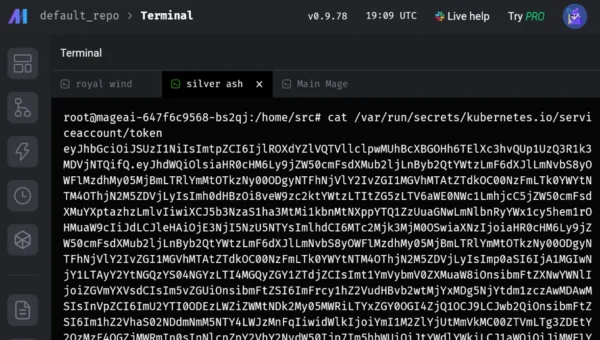
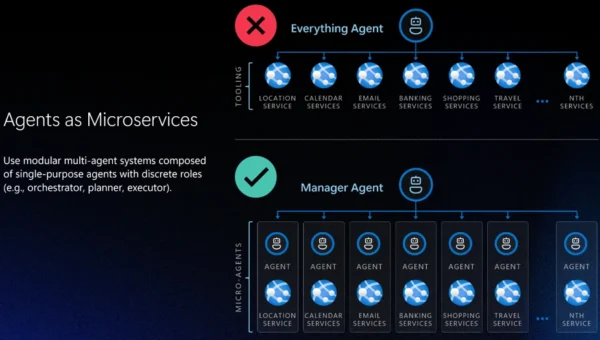
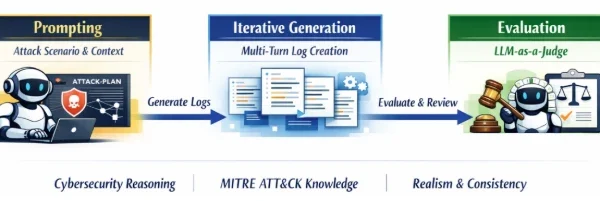
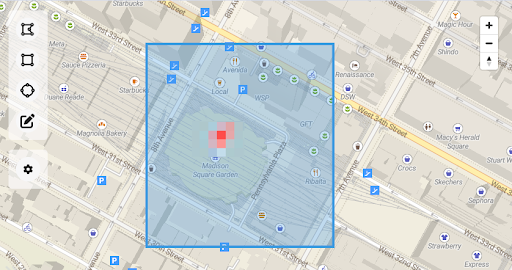
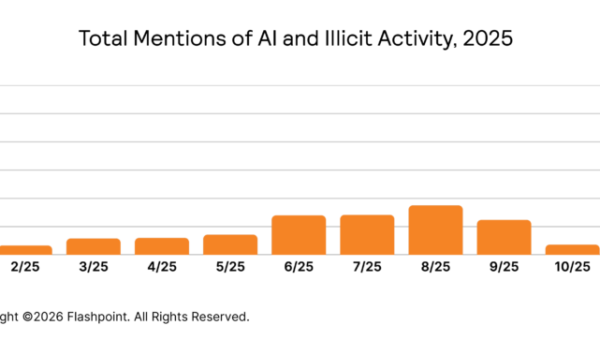
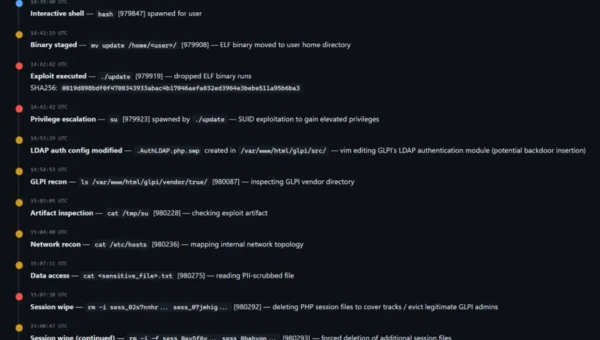
In this article AI and agentic application deployments on cloud-native platforms are increasing, and they often prioritize speed over secure configuration. Our observations from aggregated…