China-aligned threat actors tracked as SHADOW-EARTH-053 are exploiting old but unpatched Microsoft Exchange and IIS vulnerabilities to run a stealthy, multi-stage espionage campaign across Asian governments, critical infrastructure, and one NATO member state.
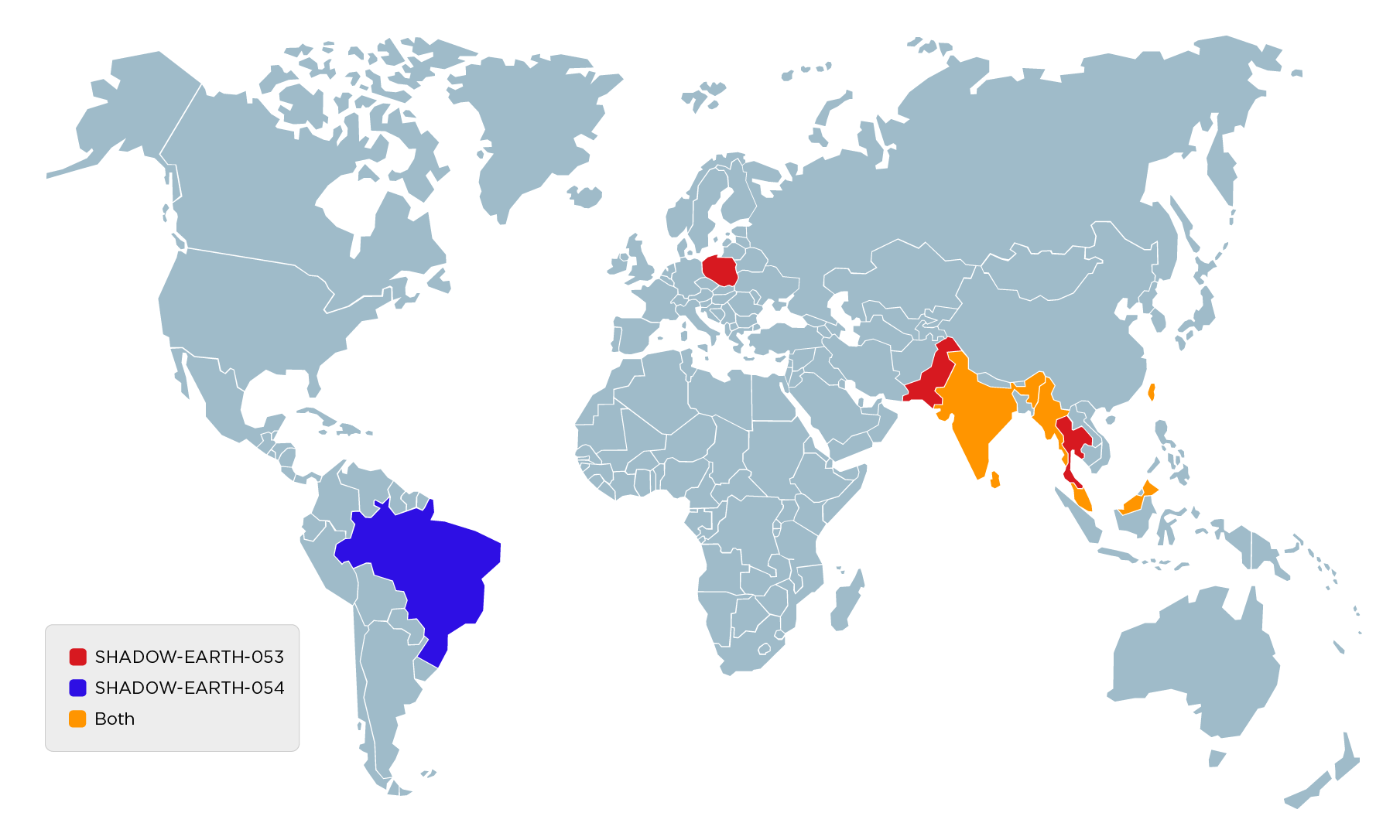
The group primarily targets government entities and critical infrastructure in South, East, and Southeast Asia, with additional activity against at least one NATO government in Europe.
Victims also include defense-adjacent IT consulting providers and transportation organizations, indicating a mix of direct and supply-chain targeting.
Nearly half of the victims were previously compromised by a related intrusion set dubbed SHADOW-EARTH-054, which shares identical tool hashes and overlapping techniques.
TrendAI Research tracks this activity as a temporary intrusion set called SHADOW-EARTH-053, active since at least December 2024 and assessed as aligned with China’s strategic interests.
However, timelines and tooling suggest independent exploitation of the same vulnerabilities rather than tightly coordinated operations.
SHADOW-EARTH-053 relies on N‑day vulnerabilities in internet-facing Microsoft Exchange and IIS servers, notably the ProxyLogon chain (CVE‑2021‑26855, ‑26857, ‑26858, -27065).
Despite being long patched, these bugs remain effective where legacy or unmaintained Exchange installations are still exposed.
Once a server is compromised, the attackers deploy ASP.NET web shells, commonly GODZILLA, using filenames such as error.aspx, warn.aspx, TimeinLogout.aspx, and tunnel.ashx under standard web and Exchange paths.
IT consulting firms holding government contracts, particularly those that listed the Ministry of Defense as one of their customers.
These web shells provide persistent remote command execution, often running under the IIS worker process (w3wp.exe) and forming the base from which the rest of the intrusion chain unfolds.
In some intrusions, ShadowPad samples were also delivered via AnyDesk or dropped during exploitation of newer server-side issues like CVE‑2025‑55182 (“React2Shell”), showing the group’s flexibility in entry vectors.
Post-compromise, SHADOW-EARTH-053 conducts extensive Active Directory and Exchange reconnaissance directly from the web shell, including domain admin enumeration, domain controller discovery via nltest, AD exports using csvde, and PowerView’s Get-DomainUser for user and mailbox mapping.
A lightweight custom binary, DomainMachines.exe, scans domain hosts over SMB, RDP, web, database, and Kerberos ports to identify high-value systems.
SHADOW-EARTH-054 in Malaysia, Brazil, and Taiwan, operating in similar industries to those targeted by SHADOW-EARTH-053, plus a telecommunications equipment reseller.
The primary backdoor is ShadowPad, a modular malware historically associated with Chinese espionage actors including APT41 and other China-nexus groups.
One notable loader abuses a Toshiba Bluetooth binary (renamed CIATosBtKbd.exe) to sideload TosBtKbd.dll, which fetches shellcode from ahellcode from an HKCUSoftware.
SHADOW-EARTH-053 consistently loads ShadowPad via DLL sideloading of legitimate signed executables from vendors such as Microsoft, Samsung, and others, with the encrypted payload often stored in the registry and deleted after first use.
For lateral movement and tunneling, the group leans on an ecosystem of proxy tools, prominently IOX, which is configured after setting LocalAccountTokenFilterPolicy to 1 to enable Pass‑the‑Hash across local administrator accounts.
Additional tunneling utilities such as GOST and Wstunnel are deployed from C:UsersPublic to maintain redundant SOCKS and HTTPS tunnels to shared command-and-control infrastructure.]
WMIC-driven lateral movement
Lateral movement heavily leverages WMIC to push backdoors and tools to additional Windows hosts, alongside a suspected custom RDP launcher (smss.exe) and the C# tool Sharp-SMBExec.
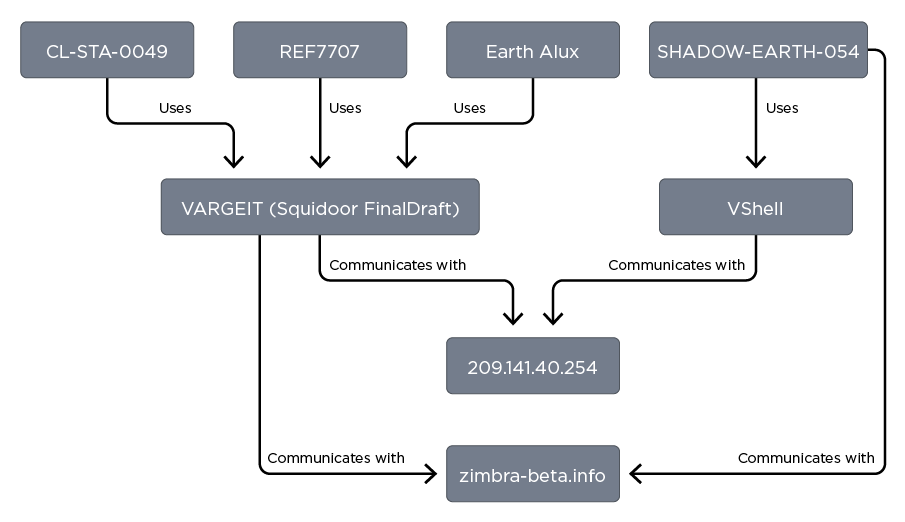
The infection vector used by CL-STA-0049 matches what we observed, however none of the other TTPs match, and we found no traces of VARGEIT.
In several cases, the attackers propagated web shells to internal Exchange servers via administrative shares, rapidly expanding their foothold without introducing new implants.
Credential access relies on tools such as Evil-CreateDump, a modified variant of Microsoft’s create-dump.exe repurposed to dump LSASS memory, and classic Mimikatz, executed through rundll32 from the IIS worker process.
The group also deploys a binary dubbed newdcsync for DCSync-style attacks against domain controllers, enabling theft of high-value credentials and replication secrets.
To evade detection, SHADOW-EARTH-053 uses the RingQ packer, domain names that mimic security products or DNS themes, and extensive process renaming of tools like net.exe and PowerShell into randomized .log filenames.
Telemetry also links Linux NOODLERAT samples retrieved from the same infrastructure and controlled via office365-themed domains to this intrusion set with low confidence, suggesting experimentation with cross-platform espionage tooling.
For defenders, the campaign underscores that unpatched Exchange and IIS servers remain high-risk assets, and that web shell detection, registry-resident loaders, WMIC abuse, and covert proxy tooling must be core hunting priorities, especially in government, defense, and critical infrastructure environments across Asia and allied states.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.