ClickFix started as a Windows problem. It is no longer one. Microsoft’s Defender Security Research Team published a detailed analysis documenting an active ClickFix campaign that is targeting macOS users since at least January 2026. The primary goal is delivering infostealers by convincing users to paste malicious commands into their own Terminal, framed as routine system maintenance.
ClickFix is a social engineering technique that bypasses conventional malware delivery entirely. Rather than exploiting a vulnerability or compromising a download link, it presents the victim with a fake problem. A disk space alert, a system error, a software installation guide — and instructs them to copy a command and paste it into Terminal to fix it. The user becomes the unwitting installer of their own malware. No exploit required, no drive-by download, no suspicious attachment.
How This Campaign Works
Microsoft observed threat actors seeding malicious commands across blog sites and user-driven content platforms where people search for macOS advice — optimizing disk space, fixing system errors, installing utilities. The pages look credible. The instructions look legitimate. When the user runs the command, they are not installing a disk cleaner but instead loading one of three infostealers: Macsync, Shub Stealer, or Atomic macOS Stealer (AMOS).
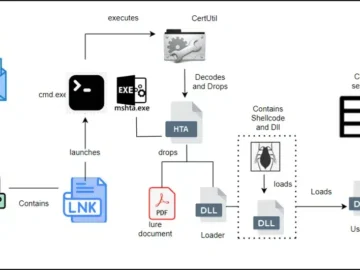
Since February 2026, one observed campaign variant uses curl to pull a loader shell from attacker infrastructure the moment the ClickFix command runs. That loader is a zsh script, a macOS default shell that decodes and decompresses an embedded payload using Base64 and Gzip before executing it in memory using eval.
Before delivering any payload, the script performs a critical environmental check. It looks for Russian and CIS-region keyboard layouts on the device. If it finds one, it reports a cis_blocked event to the attacker’s server and stops. This is a deliberate kill switch to avoid infecting operators’ compatriots or tripping sandbox environments operated by CIS-based security researchers.
A second campaign, active from late January 2026, used a macOS executable named “helper” or “update” instead of a shell loader. A first-stage script decoded a Base64 payload, decompressed it with Gunzip, and dropped a malicious Mach-O binary — native macOS executable code — into /tmp/helper or /tmp/update. To avoid triggering macOS security warnings, the binary had its extended attributes removed before execution. The infection chain used an AppleScript-based stager with array subtraction obfuscation to conceal its strings and commands from static analysis.

Also read: ClickFix macOS Attack Uses Script Editor to Bypass Security Controls
What Gets Stolen
Once installed, the three infostealer families converge on the same targets which includes media files, iCloud data, Keychain entries — Apple’s built-in credential management system — and cryptocurrency wallet keys.
In some campaigns, the malware goes further. it replaces legitimate cryptocurrency wallet applications on the victim’s device with trojanized versions, embedding persistent access that survives beyond the initial infection window and activates on the user’s next interaction with their wallet.
The macOS Assumption Problem
The sustained and escalating investment in macOS-targeted ClickFix campaigns reflects a calculation that security researchers have documented with increasing clarity through early 2026. MacOS users skew toward higher-value credential profiles. Developer machines run on Macs. Cloud engineers, financial professionals, and cryptocurrency holders disproportionately use macOS. AWS credentials, SSH keys, Kubernetes configuration files, crypto seed phrases, and corporate SSO sessions all live in Keychain or browser credential stores on those machines — and AMOS, MacSync, and Shub Stealer are all purpose-built to harvest exactly that data.
At least 20 distinct malware campaigns targeted AI and developer tools between February and March 2026 alone, nine of which targeted both Windows and macOS, with seven targeting macOS exclusively.
What Apple Has Done — and What It Does Not Cover
Apple added a Terminal security warning to macOS Tahoe 26.4 that alerts users when they attempt to paste potentially suspicious commands. Attackers have already adapted. Jamf Threat Labs documented a variant that routes execution through macOS Script Editor via the applescript:// URL scheme rather than Terminal, bypassing the new warning entirely. Users on older operating system versions, and those who dismiss the new warning, remain fully exposed.
Microsoft recommends monitoring for Terminal activity involving curl, Base64 decoding, gunzip, osascript, or JavaScript for Automation invocations. Defenders should treat any unsigned DMG or unofficial “terminal fix” utility as high-risk, and organizations should enable custom detection rules covering abnormal Keychain access, browser credential store queries, and cloud credential file reads.