A critical authentication bypass vulnerability affecting cPanel and WHM servers, identified as CVE-2026-41940, is currently under active exploitation by a highly sophisticated and elusive cybercriminal syndicate known as Mr_Rot13.
The vulnerability carries a maximum severity CVSS score of 9.8, allowing unauthenticated remote attackers to completely bypass standard authentication protocols and gain full administrator privileges over affected Linux systems.
XLab researchers indicate that this advanced hacking group has operated covertly for over six years with an exceptionally low detection rate across all major cybersecurity products.
The current exploitation campaign aggressively leverages this critical flaw to deploy advanced Go-based payload injectors, implant persistent, hidden backdoors, and establish comprehensive remote control capabilities across compromised virtual host management environments worldwide.
cPanel and WHM Servers Targeted
Since the public disclosure of the vulnerability in late April 2026, global threat monitoring systems have recorded massive automated exploitation attempts originating from over 2,000 distinct IP addresses worldwide.
Ctrl-Alt-Intel reported a significant security incident in early May in which hackers successfully exploited this cPanel vulnerability to infiltrate Southeast Asian government and military networks and exfiltrate over 4 gigabytes of highly sensitive data.
The primary attack chain utilized by the Mr_Rot13 syndicate involves a custom Go-based payload infector that is downloaded from remote servers and executed silently in the background of compromised machines.
XLab researchers discovered that this specific infector systematically modifies root system passwords, implants custom SSH public keys labeled as cpanel-updater to bypass standard logins, and drops a Python-based webshell to ensure redundant administrative access.
The payload infector also exhibits unique structural characteristics, suggesting its underlying code may have been partially generated by artificial intelligence and that it contains extensive Turkish log output during execution.
To further solidify their unauthorized access, the attackers inject highly customized malicious JavaScript code directly into the cPanel login interface through modified server template files.
This custom JavaScript silently intercepts user credentials, user-agent strings, and active session details whenever a legitimate administrator attempts to log into the compromised WHM or cPanel interface.
XLab researchers noted that the stolen authentication data is rapidly exfiltrated either to attacker-controlled domains obfuscated using the classic ROT13 algorithm or directly routed to a dedicated Telegram channel securely operated by the threat actors.
The threat group demonstrates high operational awareness by continuously updating the tokens of their Telegram bot to maintain strict operational security, especially when external security researchers attempt to interact with or probe their automated data exfiltration infrastructure.
Persistent Remote Control and Stealth Operations
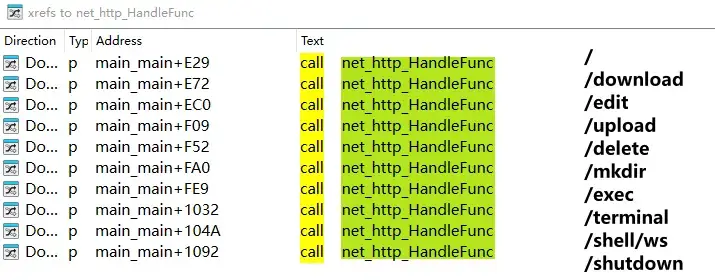
Beyond routine credential harvesting, the Mr_Rot13 group consistently deploys a robust, cross-platform remote control Trojan known internally as filemanager to maintain long-term, unrestricted access to infected server environments.
This statically linked executable application silently listens on specific network ports. It provides remote attackers with a comprehensive, web-based graphical user interface for seamless system file management, unauthorized remote command execution, and direct, persistent shell access.
XLab researchers highlighted that this bespoke Trojan utilizes advanced bcrypt cryptographic hashing for authentication, deliberately rejecting straightforward plaintext password transmissions to significantly enhance its stealth and operational security against standard network traffic interception tools.
The deliberate sophistication and specialized nature of these bespoke administrative tools highlight the advanced technical capabilities of the threat actors orchestrating this widespread server compromise campaign.
Tracing the network infrastructure used in these recent cPanel attacks revealed deep historical connections to previously undetected malicious server activities.
Security analysts successfully linked the current command-and-control domains to a deeply obfuscated PHP backdoor that was initially uploaded to public malware-scanning repositories in 2022 and, miraculously, maintained a zero-detection rate for multiple years.
This historical PHP backdoor primarily targeted vulnerable WordPress content management system installations, using complex XOR-based string concatenation to conceal its malicious communication routines from signature-based antivirus scanners completely.
XLab researchers emphasize that the persistent use of the same network domains and encoding techniques over several consecutive years confirms that Mr_Rot13 is not an opportunistic operation, but rather a highly disciplined cyber espionage or organized cybercrime group dedicated to long-term enterprise server compromise, sensitive data theft, and persistent network infiltration.
IOC
MD5
2286f126ab4740ccf2595ad1fa0c615c *help.php
2de27ca8d97124adaf604b18161a441e *Update
29222f5e73dd10088fcf1204aa21f87f *Update
fb1bc3f935fdeb3555465070ba2db33c *Update
45fc93426cf08f91c9f9de5f04a12263 *filemanager-darwin-amd64
711afb014f64c97d7b31685709c34ce7 *filemanager-darwin-arm64
22613c952459e65ce09fb6b5c1c03d47 *filemanager-linux-386
9305b4ebbb4d39907cf36b62989a6af3 *filemanager-linux-amd64
e49f68a363c867608972680799389daf *filemanager-linux-arm64
e1ec6ebb96cf87c785ee6a7da677c059 *filemanager-linux-armv7
02a5990b11293236e01f174f5999df20 *filemanager-windows-386.exe_
bae1f1bce7c82fa86f05b12e2e254cfc *filemanager-windows-amd64.exe_
C2
wrned.]comNote: IP addresses and domains are intentionally defanged (e.g., [.]) to prevent accidental resolution or hyperlinking. Re-fang only within controlled threat intelligence platforms such as MISP, VirusTotal, or your SIEM.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.