Cross-Site Scripting (XSS) Explained

Source link
Related Articles
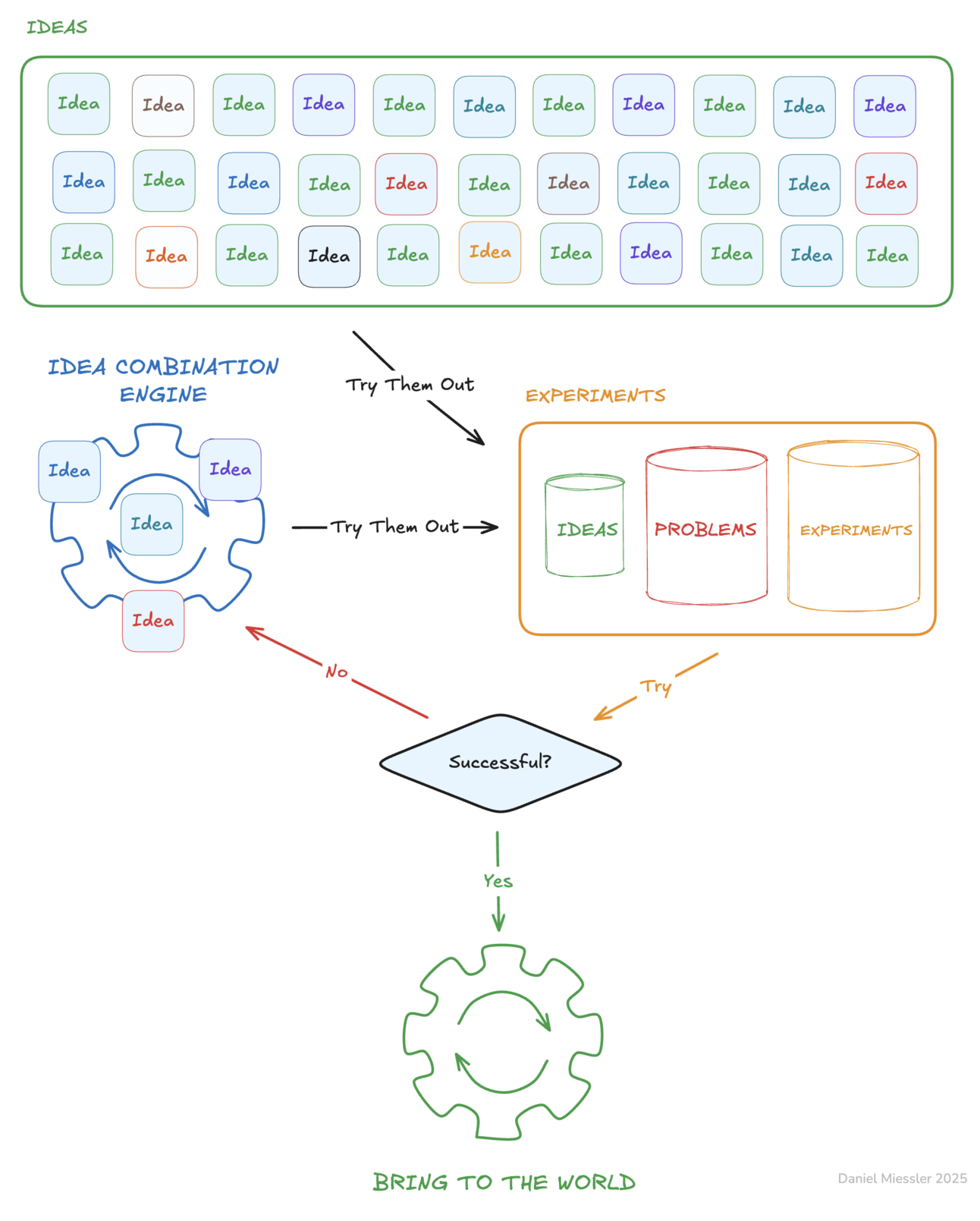
All Mix →A Possible Path to ASI
Table of Contents A Definition of ASI Extending AGI to Get to ASI A Possible Path to Both AGI and ASI Summary I’ve had what…
AJAX : What’s All The Commotion?
If you’re a geek like me (which you might be if you’re reading this), you’ve maybe heard the buzz about something called AJAX. Well, what…
How Security Edge Revolutionizes API Security
Table of Contents Why Are You Sending API Traffic Through a CDN? What Sets Security Edge Apart? Security Edge: The New Standard for API Protection…
Hive Five 221 – Underdoing the Competition
Table of Contents The Bee's Knees Updates Work Level up Member edition sneak peek The Member Edition I’m still running daily, but I’ve swapped some…
Security@ 2021 Call for Speakers is Open
HackerOne’s global Security@ conference is back for its fifth year on September 20, 2021. Today, we’ve opened our call for speakers! Are you interested in…
How Human Testers Improve Application Security
A suite of DevSecOps tools is available to automate reviews, audits, tests, and scans throughout the development pipeline, which have become standard in application security…