Cybercrime is Not Hacking!

Source link
Related Articles
All Mix →6 months after the launch of Detectify Crowdsource: What has happened so far?
Table of Contents What is Crowdsource? What have we found? Who has joined Crowdsource? The future of Crowdsource? Utilize our hacker community to test your…
The Left’s Brexit | Daniel Miessler
I think Trump’s conviction might be the American Left’s version of Brexit. Let me explain. First off, I think Trump is the worst president we’ve…
New features means new bugs. Sometimes new features designed to… | by Sean (zseano)
Sometimes new features designed to generate revenue for a company can be rushed and sometimes not enough thought has gone into how to securely implement…
An automatic interactive pre-commit checklist, in the style of infomercials
How to set up an interactive checklist using a Git pre-commit hook script. What’s that, you say? You’ve become tired of regular old boring paper…
Q&A with HackerOne’s VP of Customer Success Jeff McBride
“As cliche as it sounds, customer success is everyone’s job. Everyone’s,” said Jeff McBride when we asked him about his relatively new role as the…
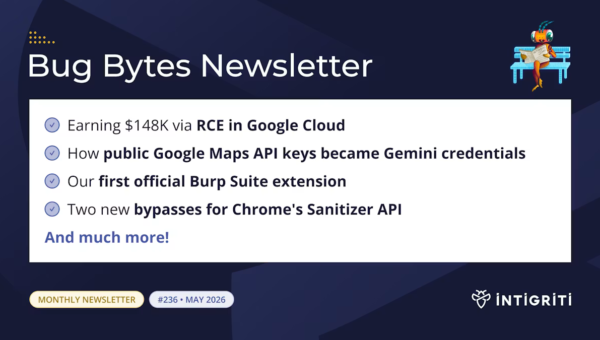
Intigriti Bug Bytes #236 – May 2026
Table of Contents Blogs & videos Exploiting SQL injection vulnerabilities Tools Google API Keys Weren't Secrets. But then Gemini Changed the Rules. BountySync+Social London Hacker…