A newly uncovered cyber campaign dubbed “EtherRAT” is raising concerns across enterprise environments, as attackers combine SEO poisoning, GitHub abuse, and blockchain-based infrastructure to target high-privilege IT professionals.
Instead of broadly targeting users, the attackers deliberately impersonate trusted administrative tools, increasing the likelihood that victims already have elevated system access.
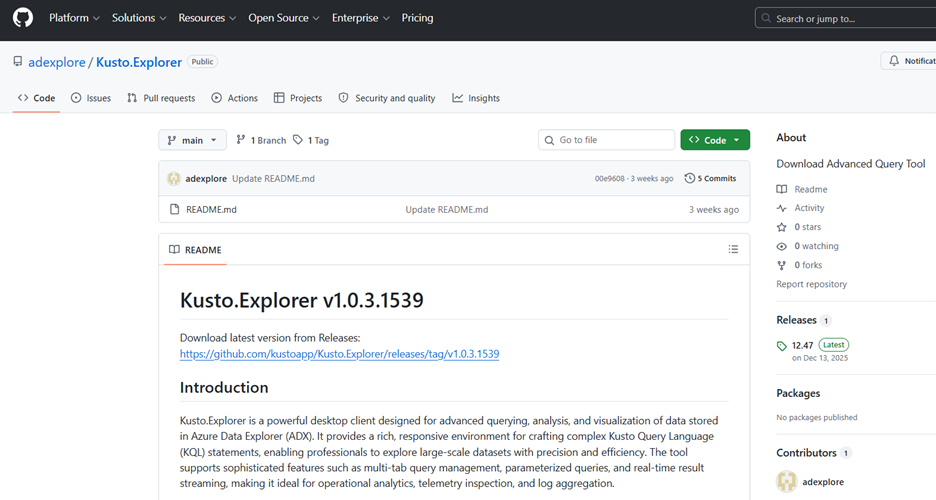
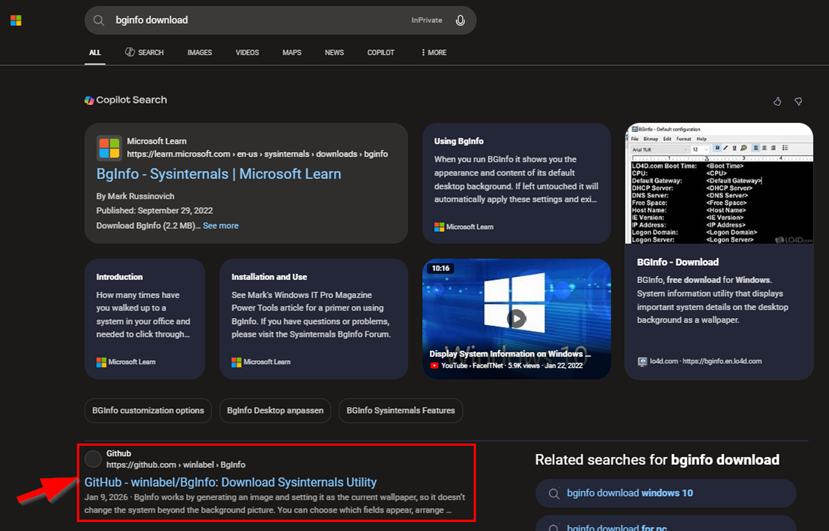
The attack chain begins with SEO poisoning across search engines such as Bing, Yahoo, DuckDuckGo, and Yandex. Threat actors manipulate search rankings so that malicious GitHub repositories appear as top results for queries like “Kusto Explorer download” or “Sysmon tool.”
These repositories act as clean “facades.” They contain convincing documentation but no malware. Instead, users are redirected via README links to a second GitHub repository, which hosts the actual malicious MSI installer.
Discovered by the Atos Threat Research Center (TRC) in March 2026, the operation focuses on administrators, DevOps engineers, and security analysts.
This dual-stage setup provides resilience. If the payload repository is removed, attackers can quickly replace it while keeping the SEO-ranked facade intact, preserving visibility and infection flow.
Targeting High-Privilege Users
The campaign specifically impersonates widely used administrative tools, including PsExec, AzCopy, Sysmon, LAPS, and WinDbg. These tools are typically used only by IT professionals with elevated privileges.
A user seeking Kusto Explorer – critical tool for engineers and analysts querying Azure Data Explorer via KQL – is led toward a non-malicious storefront designed to build initial trust.
This approach acts as built-in victim profiling. If someone downloads and executes these tools, they are likely an administrator. A successful infection, therefore, provides attackers with immediate access to critical systems often described as “keys to the kingdom.”
The tactic also leverages trust. Security professionals may unknowingly download a malicious version of a tool they use daily, especially when it appears prominently in search results.
The delivered payload is a malicious MSI installer that deploys a multi-stage, fileless-style Remote Access Trojan (RAT) written in JavaScript.
Execution begins with an obfuscated batch script that installs Node.js and launches the next stage. Subsequent stages decrypt and execute payloads in memory using AES-256 encryption, making detection difficult.
Persistence is achieved through Windows registry Run keys, while the final RAT operates under legitimate processes like conhost.exe to avoid suspicion. The first repository the user opens is a storefront that impersonates the targeted administrative tool.
The malware continuously communicates with its operators, executes remote commands, and can exfiltrate sensitive data.
What sets EtherRAT apart is its use of Ethereum blockchain technology for command-and-control (C2).
Instead of hardcoding server addresses, the malware queries a smart contract on the Ethereum network via public RPC endpoints. The contract stores the current C2 address, which attackers can update at any time.
This method provides two key advantages:
- Infrastructure resilience: No fixed domain or IP to block.
- Dynamic control: A single blockchain transaction can redirect all infected systems.
Because public blockchain services are widely accessible, traditional takedown efforts are largely ineffective.
Ongoing Activity and Attribution Links
Atos researchers identified at least 44 malicious GitHub facade repositories between December 2025 and April 2026, indicating sustained activity. The malware continues to evolve, with multiple variants and expanding infrastructure.
Dominant search presence effectively masks the threat, as the facade repositories appear as the primary, verified download locations for essential IT tools.
Security researchers have also noted similarities between EtherRAT and tools linked to advanced threat groups such as Lazarus (North Korea) and MuddyWater (Iran), though attribution remains under investigation.
Unlike typical mass malware campaigns, EtherRAT emphasizes stealth, persistence, and strategic access. After initial compromise, attackers perform quiet network reconnaissance rather than noisy actions, reducing detection chances.
Organizations are advised to verify software sources, restrict administrative privileges, and monitor unusual outbound connections especially to blockchain-related services.
This campaign highlights a growing trend: attackers blending legitimate platforms and decentralized technologies to build highly resilient and targeted threats.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.