Extreme Transparency or Corporate Security Responsibility?

Source link
Related Articles
All Mix →A Year In HackerOne’s Bug Bounty Program
Table of Contents Hackers Report The Most Vulnerabilities In 2022 To Keep The Platform Secure Acquisitions And Third Party Software Flaws Were The Biggest…
Flattr, and Why It’s Brilliant
Flattr is an exciting new social networking / micro-payment service that allows you to set a donation amount that gets divided among all the different…
Detectify security updates for 31 October
Table of Contents CVE-2017-7529: NGINX Remote Integer Overflow / Memory Leak F5-Networks / Big-IP Cookie Information Exposure CVE-2018-9206: jQuery-File-Upload Arbitrary File Upload Spring Boot Actuator…
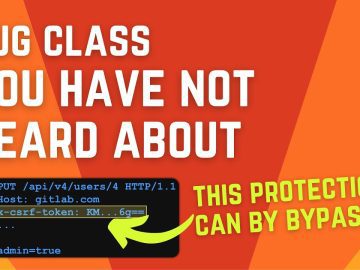
Client-side path traversal vulnerability class explained – $6,580 GitLab bug bounty
Client-side path traversal vulnerability class explained – $6,580 GitLab bug bounty Source link
Basic GPG Commands | Daniel Miessler
Table of Contents Examples Main Functions Links I hate forgetting things. Here are a few GPG commands for doing the basics from the command line.…
Why You Should Dump Internet Explorer
The time has come to dump Internet Explorer. I know, I know — you may have heard the same thing before from those that think…